Image

Image
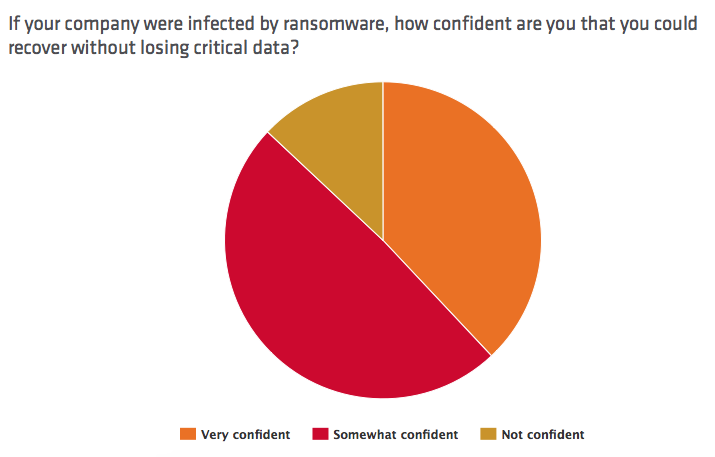
"The decision to pay a ransom comes down to the confidence and financial cost of recreating or restoring data from a previous backup," said Travis Smith, senior security researcher for Tripwire. "Since most ransomware samples we have seen have a time limit to pay, it’s important to have confidence that you can restore the majority of data on short notice. Organizations should focus on improving backup and restoration procedures to reduce the cost of restoring data and services after a potential breach."Companies should also strengthen their security awareness programs in an attempt to prevent ransomware infections in the first place. Towards that end, Tripwire recently conducted a poll on Twitter asking respondents to reflect on the most important step users can take to prevent an infection. https://twitter.com/TripwireInc/status/712553244711641089 In total, Tripwire received 175 responses. Close to half (47 percent) of participants voted "Don't click suspect links" as the best way users can defend against ransomware. This preference suggests that anti-phishing user education can go a long way towards preventing against a malware infection. https://twitter.com/5683Monkey/status/712707587318366209 Backing up one's data received a little more than a third of the vote at 37 percent, followed by "Install software patches" and "Use an AV solution" at a combined 16 percent. While not a preventive measure per se, some respondents ultimately felt backing up one's data was the most suitable option by which users could confront the ransomware threat. https://twitter.com/En3pY/status/712698514195787776 The list of options presented in Tripwire's poll is not exhaustive. For more information and insight on how you can prevent a ransomware infection, please click here. If you think you have been infected by crypto-ransomware, please click here to see if you can use a tool to decrypt your files for free. Title image courtesy of ShutterStock
