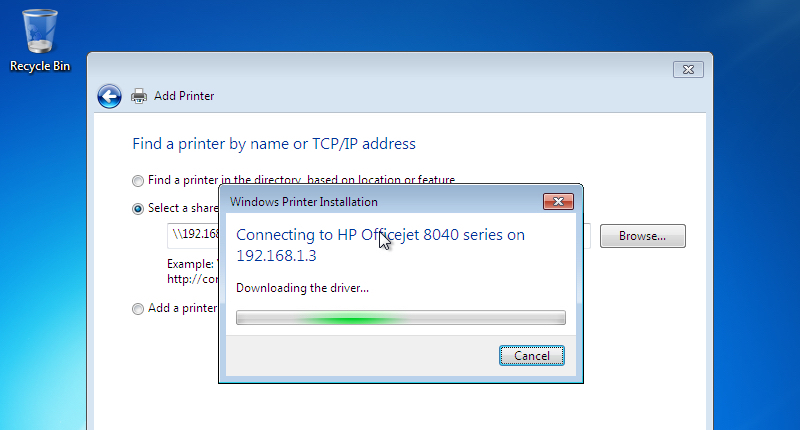
You visit a company on business, and want to print something out. You visit another department in your office and need a hard copy of a document in your email. You're a guest at someone's home and want to print off directions to the airport. What do you? Simple. You get Windows to quickly search for and add a printer hosted on the network, and off you go... But first, Windows needs to install a driver for that printer. And that's where a serious problem rears its ugly head, according to security researchers at Vectra Networks who discovered a vulnerability that has been present in Microsoft Windows for over 20 years:
"This attack results in having 'system' rights on any workstation that connect to your printer. We are effectively transforming a printer in an internal drive-by exploit kit, where we can just wait for people to come get infected without any warning." "Not only will that unit be able to infect multiple machines in your network, but it would also be able to reinfect over and over. Finding the root cause might be harder since the printer itself might not be your usual suspect."
Günter Ollmann, CSO of Vectra Networks, warns that printer drivers have been able to circumvent security measures that other software has to pass through:
"This particular vulnerability enables an attacker to exploit the ease with which Windows machines connect to printers on networks. While most devices require specific user or administrative permission before software is downloaded onto a machine, it is possible for printer drivers to bypass these restrictions."
Furthermore, once it has managed to infect one computer, it wouldn't be hard for the malware to exploit its system-level controls to spread further across the network, compromising more and more PCs. The problem is compounded by the fact that printers are often not treated as being as much of a priority to patch and update as regular PCs, meaning they can be left vulnerable to attack through vulnerabilities - allowing an attacker to compromise the device and replace a genuine printer driver for one containing a malicious payload. Sure enough, the researchers were able to demonstrate how they were able to reverse engineer an unnamed printer's firmware in order to serve up a malicious driver. But even if the drivers stored on printers haven't been compromised by malicious hackers, there is still a way in which attackers could exploit the flaw. It's easy to imagine, for instance, that a malicious hacker could advertise a fake printer on the network, and wait for an unsuspecting user to connect. The following YouTube video describes the printer vulnerabilities in greater depth. https://www.youtube.com/watch?v=DuMk-yxZApA&rel=0 In a critical security update issued on Tuesday for all supported versions of Windows, Microsoft said that it was addressing the vulnerability by correcting how the Windows Print Spooler service writes to the file system, and issuing a warning to users who attempt to install untrusted printer drivers. It's good to see Microsoft attempting to tackle the issue, as it's clear that this is a security hole that attackers would be sorely tempted to exploit. But I worry that the typical user will just ignore a warning message in their haste to get their documents printed out. It's chilling to think that the flaw has been lurking for so long without it being uncovered until now. And, of course, although Microsoft has issued a patch for all supported versions of Windows - that doesn't include earlier editions such as Windows XP and Windows 95. These legacy operating systems are, according to Vectra, also vulnerable - meaning that we have been unwisely trusting printers to install software on our computers for over 20 years. Editor’s Note: The opinions expressed in this and other guest author articles are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

