Image

"While the victim thinks the attachment is corrupted, in the background the RAA Ransomware will start to scan all the available drives and determine if the user has read and write access to them. If the drives can be written to, it will scan the drive for targeted file types and use code from the CryptoJS library to encrypt them using AES encryption."Some sources have reported the ransomware is written in JavaScript, another language which is similar to JScript in that they are both derived from ECMAScript. JScript is designed specifically for Windows systems, but while it can run via Internet Explorer, it cannot do so via the newer Edge browser. Other ransomware such as Ransom32 have also made use of scripting languages, but RAA is different in that it doesn't contain the usual binaries, such as a Tor client or modules used to run the script. Researchers at Trend Micro feel RAA's unique coding could help prevent it from being detected by anti-virus solutions:
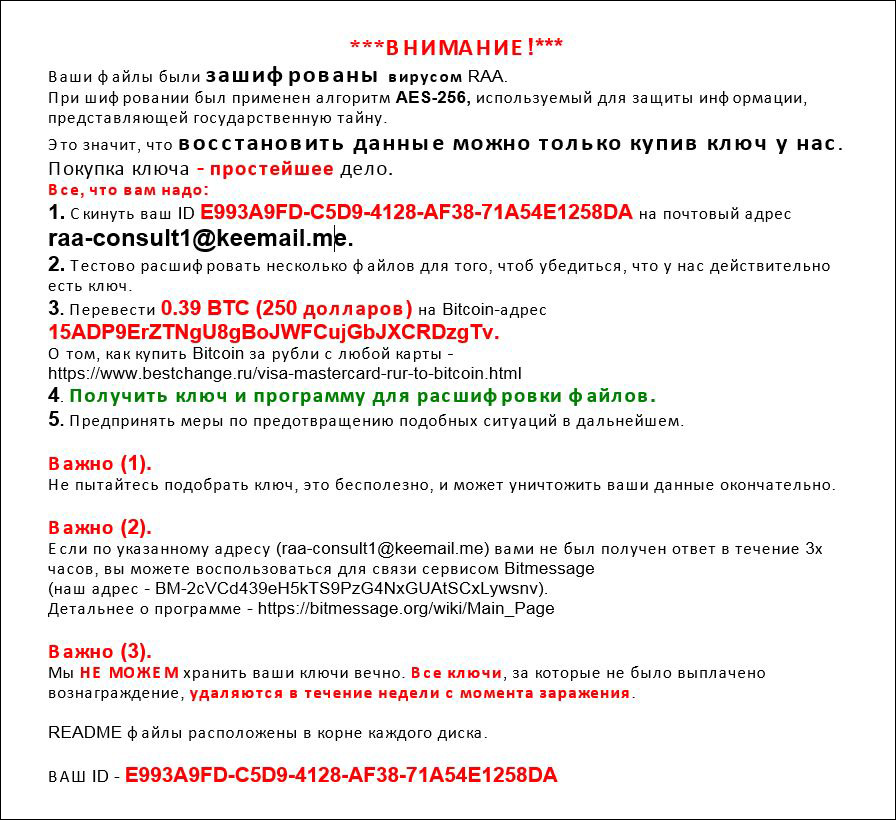
"Since most malware are written in compiled programming languages—with ransomware often taking the form of executables—using a language uncommonly used to deliver malware can be seen as less prone to detection. Cybercriminals know it’s a race; they capitalize on the lapse of time where their malware remains undetected in order to maximize their profit."RAA appends .locked to each file it encrypts, deletes the Windows Shadow Volume Copy Service (VSS), and displays a message written entirely in Russian that asks for approximately $250 USD in ransom.
Image