
The term APT (Advanced Persistent Threat), like many other acronyms in the world of IT/Information/Cyber Security entered our vocabulary some years ago, along with other partnering phrases, such as Advanced Evasion Techniques (AET), which at the time took the headlines as something new. Whilst these new outlined logical dangers do serve up a very real threat to the modern era of high-dependency computerisation, in their base form, they are actually nothing new – they simply reinvented themselves but nobody seemed to have noticed,which is why the ‘P’ for Persistent is so very apt. However, there is one subtle difference between those historical threats, and the current danger posed by the evolution of insecurity insofar as, those who create AETs apply methodologies based on serious planning and project management to provision higher assurance of the anticipated malicious outcomes.
Way back in 1993 whilst serving with the Royal Air Force in the field of Computer Security based on the works of Fred Cohen and Ralph Burger, I conducted research into what was the then newish phenomenon of the computer virus, and came up with the madcap idea of circumventing anti-virus defences by employing single layer, or multiple layers of deep encapsulation to transport hidden malicious payloads, which would evade any anti-viral protection – which to the dismay of some attending delegates at Virus Bulletin 93 actually worked. The point to this introduction is, if such a malicious construction idea was to enter the fray in 2015, it would not doubt also be tagged as an APT! Today, there is a tendency in our cyber security communities to apply a label to every risk encountered along with an all-encompassing descriptive tag, which is then passed off to some associated tech-protection schema, which accommodates where practicable a fully automated, or semi-automated security solution to provision the required level of Silver-Bulleted mitigation and defence. Yet in the case of the APT, this approach does not take into account the multi-faceted capabilities of attack. For instance, is the APT a virus? Is it a zero-day exploit? Is it a system vulnerability? Is it a brand new malicious script? The answer to all of these statements is confusingly, NO/YES!
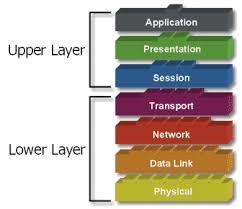
To gain a deeper insight and understanding of the capabilities and objectives of what an APT may be, it can help to view the threat alongside the top down 7 layered OSI stack as an exemplar to demonstrate just how the creator of an APT may employ their imagination to leverage his/her conjoined vectored-spectrum of attack against a target to exploit one, or more of the associated upper or lower layers as shown below:
- Application
- Presentation
- Session
- Transport
- Network
- Data Link
- Physical
It is also important when engaging threats posed by an APT to also appreciate that they can, and will morph into whatever shape their creator wishes, leveraging on multiple points of propositioned attack vectors to deliver the attack, with an intention to exploit some element, or elements of the associated with the stack – thus to some extent, such crafted and yet to be crafted APTs represent the manifestation of the unknown unknowns, which we are seeking (trying) blindly to defend against. For instance, it may be that our assailant has decided to focus their malicious attention on the upper layer of the stack and seeks to achieve direct exploitation at that level, which may in turn, create an opportunity for the secondary level of exploitation and compromise closer to the technological interfaces of the OSI model by using social engineering to hook the human target, followed by a payload, which delivers technical attacks against an asset with an objective of targeting the network layer. And so, at this juncture, it may be opportune to introduce a definition of what an APT really is:
‘A logical or physical condition which supports an attack, leveraging a composite vectored adverse condition in an attempt to compromise people, applications, or systems, to achieve direct, or indirect access to facilitate a part, or full exploitation of a targeted asset or assets.’
The most prolific danger posed by the APT is the fact that we simply don’t know what they may logically resemble when they arrive, and as to what levels of the stack our creator has targeted to achieve the architected end goal of exploitation. For instance, it may be that the attack is provisioned against a person or multiple persons via a blended spear phishing attack with the objective of delivering a payload, which will seek to exploit a legacy Windows XP systems, or a direct attack against the perimeter security infrastructure with an obfuscated, or manipulated IP header designed to confuse the protective systems in a way that they misunderstand what is logically presented, and thus allow a malicious connection to be achieved at the Network Layer. It could be with such an unauthorised egress our attacker then invokes a Command Line (Shell) on the internal targeted system, which in turn runs a powerful Windows Management Instrumentation Command Line (wmic.exe) to interrogate the compromised networked environment, map a segment, or to deliver a Forensic Imaging application over the network to a collocated server. Other forms of APT may be created to again exploit the human element targeting human physiology and the foibles of the inquisitive. An example here which has been employed against one London-based company involved the scattering of USB keys in the company car park baited with labels like Personal Finances, Redundancies 2015, or Girlfriend Pictures. However, the USB drives were actually loaded up with malicious attack agents based on Hacksaw and Switchblade with the objective of compromising systems via the I/O into which they the miscreant USB keys were introduced. In the overall amalgam of the targeted APT, there can be an association with a precursor of footprinting the proposed target of interest, employing Open Source Intelligence (OSINT) and any other forms of intelligence the attacker may dig up (intelligence may be considered to be of low value in isolation, but when aggregated can underpin an attack with usable facts to enhance the prospects of success). For instance, it may be that our target is leaking intelligence through Metadata based artifacts, which are published on mass to their website with unawareness that they are revealing much internal information, ranging from IP addresses, User ID’s, local system names, folders, Operating Systems, and the version levels of utilised applications, such as Oracle – all of use to our prospective attacker.

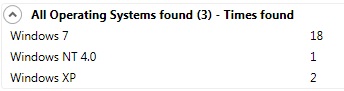
As an example, do organisations really want to tell the world they are still running Windows 4.0 on Service Pack 6a, and that they still have high volumes of Windows XP deployed throughout enterprises? Or say to confirm the business is running an outdated web server, or that they have multiples of medium to high vulnerabilities in existence, which may be further subjected to exploitation? All of which could be valuable to any attacker when framing an APT to focus their project plan against what appear to be vulnerable targets. When considering what may not be important in the area of Data Leakage, and MetaData, consider how such known knowns may allow an assailant to construct an attack. So in this example, we look at the unimportant subliminal information that may be hidden inside a document as MetaData, or under its Properties. Below is a recent example, and as you can see Windows NT 4.0 is still having its part to play in 2015, all these years on in this big name company, so we know there are potentials of exposed systems which are running out-of-patch cycles:
Visiting the part that social engineering has to play in the APT mission, imagine this real-life scenario. In an early footprinting activity, the attacker identified a set of insecure documents belonging to an employee published to a bank's website. Analysis and extraction was conducted and revealed background information about the author under the properties tab, and the associated metadata allowed the attacker to discover some internal information that related to the creation of the document under scrutiny. The next leg was to conduct an in-depth OSINT analysis of the target bank, and the personality in question, making it possible to locate the individual of interest, her department and their extension number which was conveniently associated with her Login User ID. Now, it was a simple case of looking the target up on Facebook and LinkedIn to gather more intelligence, and the strike was ready to run. It was now a matter of calling the subject, using the gathered artifacts and intelligence as the opener to the conversation to gain credibility, and the scene was set to further exploit the now compromised target to receive an infected communication – which she had been advised was on route. Here, we see the use of a multi-faceted APT in progress utilising:
- OSINT
- Analysis of Intelligence
- Social Engineering
- Exploitation of a Targeted PC Asset
- Delivery of Payload
There are, of course, many other methodologies that may be applied to compromise a target – they may not always arrive from one source, and they may not always look obvious. However, do not overlook the fact that such APT attacks may also be blended in with other more obvious conditions of distraction to remove the attention from the dangerous nibbles, and to direct the attention and resource away to the big-banging on the corporate logical defences. The best defence against any logical attack condition is to consider it has a type of the unknown unknowns, and not to look for it by name, brand, or profile, but to deploy a defence that seeks to identify any actual or inferred events, or security anomalies indicating or suggesting an adverse condition is in plays. The days of the "Silver Bullet" to defend the environment are long gone – we live in a world of insecurity which dictates we leverage and maximise our imagination to protect our assets from unknown unknowns. This imposition also dictates that organisations also have high capability effective detection and timely alerting systems in place which, as far as is practicable can map events across the organisation, and where possible interfaced into any remote third-party organisations. As opposed to one ineffective approach taken by a UK company who relied on ITIL and help desk tickets to alert any penetration, unauthorised creation of privileged accounts and viral infections up to four weeks after the reported event. And even then with no guarantee they would be investigated. This is without doubt one of the most dangerous approaches any business can take when dealing with any APT, where there are actually confirmed situations of inner network compromise – an ideal opportunity for any APT-based attack to exploit and remain extant within the network for months or even years! The conclusion to all of the above is, any APT vectors of attack against an organisation may attributed in some way to the levels of the upper and lower levels of the stack, and may seek to conjoin a cross purpose compromise from a singular or multiple levels to facilitate an end goal. Such exploitation techniques may also cross a spectrum of activities, ranging from blended attack, SPAM email, malicious links, right down to the simple, yet effective use of social engineering to compliment the attack. Also, within the landscape of the APT, we should not dismiss the value that OSINT, data leakage, and other forms of subliminal data bring to the benefit of the attacker. The very presence of the unknown unknown security threats posed by project planned APT attacks mean we must consider and investigate every adverse flag that is set to assure that, as far as it practicable, they are not a conditions which will inflict damage of the protected assets. In the year 2015, we must realise that the way in which unconventional APTs are leveraged dictates that conventional defences simply are not fit for purpose. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc. If you are interesting in contributing to The State of Security, contact us here.

