
In December of 2011, Tripwire published a list of security’s top 25 influencers. More than three years later, we are pleased to announce a new list for 2015 -- The Infosec Avengers! For each influencer whom we have selected, we include their Twitter handle, blog URL and reasoning for selecting them. We also include their answer for what infosec-related superpower they would choose to have. This year’s list (in no particular order) has some old faces and some new. Do you agree with our choices? Who else would you have chosen?
BILL BRENNER | @BillBrenner70

Blog: The Akamai Blog Brenner is Senior Program Manager for Editorial, Information Security Group at Akamai Technologies. He has contributed much to our industry, having written for a number of tech news websites and publications, including TechTarget and CSO Magazine, and served as a member of the Board of Directors for the National Information Security Group (NAISG). Besides sharing his thoughts on infosec matters, he runs OCD Diaries, a blog dedicated to overcoming anxiety, fear, and doubt. If you could have one infosec-related superpower, what would it be? If I could be granted one superpower, it would be to unlock the secret to preventing data breaches. Then I would write a book on it.
WENDY NATHER | @RCISCwendy

Blog: Idoneous Security Nather is Research Director at the Retail Cyber Intelligence Sharing Center. She has worked in all aspects of IT Security at various companies, including Texas Education Agency and Swiss Bank Corp (now USB). SC Magazine featured Nather as a “Power Player” in security in 2014. We originally featured her in our original “Top Influencers” post, and we feel she more than deserves to be listed once again. If you could have one infosec-related superpower, what would it be? If I had an infosec superpower, I would like it to be mind control. I could use it for social engineering pentests: “You will give me all your admin passwords, let me into the data center, and bring me pizza.” I could use it on auditors: “This is not the material finding you were looking for.” But most importantly, I could use it to get all the budget I wanted: “Not only can we finally afford enough staff and technology, but every member of the team gets a Tesla!”
MIKKO HYPPONEN | @mikko

Blog: Mikko Hypponen Hypponen is a respected teacher, speaker, and commentator on all things information security. Aside from acting as the CRO at F-Secure, in the past he was part of the Conficker Working Group and participated in classified meetings on the Stuxnet worm. He has also assisted law enforcement agencies in the U.S., Europe, and other regions on cybercrime cases. Hypponen in turn uses this extensive experience to keep his followers informed about the latest trends in information security. If you could have one infosec-related superpower, what would it be? I'd like to be able to copy an image of anybody's hard drive or mobile phone just by waving my hand over it. That could come in handy. For example, if you lost your files and had no backup, you could always ask me for a copy.
GRAHAM CLULEY | @gcluley

Blog: Graham Cluley Graham Cluley was inducted into the InfoSecurity Europe Hall of Fame in 2011, and was given an honorary mention in the “10 Greatest Britons in IT History” for his contribution as a leading authority in Internet security. Given his prestigious research and influence in the field, we are happy to say Cluley is a regular contributor to our blog. Most recently, he wrote an article about the hacker group Anunak. If you could have one infosec-related superpower, what would it be? Everyone who works in computer security is already a superhero, of course. It’s just that they normally don't feel brave enough to wear their underpants on the outside. My super power would be extrasignum complexitus. Through remote mind mesmerism, I would be able to look at any person about to sign up for a website and inject extended characters and symbols into their fingertips. That or hypnotize them into naming their pet cat “Rif2caiLd2Or3uG4.”
WIM REMES | @wimremes

Blog: Wim Remes Remes is Manager Strategic Services EMEA at Rapid7. He is also co-organizer of BruCon and recently completed a three-year term as Director of (ISC)2. Remes has spoken at a number of conferences, such as Black Hat. Additionally, Infosecurity Magazine interviewed him this past October. In 2013, we named Remes as one of the rising stars in infosec education. We are pleased to announce that he is now one of the top names in the industry. If you could have one infosec-related superpower, what would it be If I had the ability to make all current and future vulnerabilities go away, life would get a little bit boring so definitely not that. I would love to have the ability to connect people across cultures and interests to make them care enough about security. With technology becoming important in all of our lives, we could no longer deny our responsibility, and owning that, affecting change, starts with caring. Caring about ourselves but more importantly about our children, about our elders and about others.
NEIRA JONES | @neirajones

Blog: Neira Jones Jones serves on the advisory board of a number of different organizations, including Emerging Payments Association, GiveADay, and Ensygnia. Given her expertise in both information security and personal branding, we at Tripwire are glad to have gained Jones’ thoughts on how to better connect security to the business back in 2013. If you could have one infosec-related superpower, what would it be? If I had an Infosec super power, it would be the ability to make everyone immune to phishing attacks. A sort of “activate shields!” for the chair to computer interface... Wouldn’t that make a dent to ID Theft and all sorts of woes? Given that breaches with more than 10 million identities exposed grew from 1 in 2012 to 8 in 2013 (a 700% increase)*, I think that would sort out a lot of problems in one fell swoop. (*Source: Symantec Internet Security Threat Report April 2014)
GENE KIM | @RealGeneKim

Blog: Real Gene Kim Kim wrote the original version of Tripwire when he was an undergraduate student at Purdue University in 1992. Without him, none of this would be possible. Tripwire has since expanded, as has Kim’s influence on social media within the information security community. He now blogs regularly on DevOps, organizational learning, and other topics that are central to our field. If you could have one infosec-related superpower, what would it be? My ideal infosec superpower would be the Justice Embodiment, so I could show infosec that DevOps is not a way for Dev and Ops to avoid security objectives. Instead, DevOps is how to finally make Dev and Ops accountable for security — and all the other non-functional requirements, as well!
KEN WESTIN | @kwestin

Blog: The State of Security Westin is a security researcher with 14 years experience building and breaking things through the use/misuse of technology. His technology exploits and endeavors have been featured in numerous publications, and he has won awards from MIT, CTIA, Oregon Technology Awards, SXSW, and Entrepreneur. He is also a frequent contributor on The State of Security. If you could have one infosec-related superpower, what would it be? Seen the movie Lucy? The point where she is using so much of her brain that she can actually see data flowing through the air and extract data simply using her mind. That is the super power I want.
BRUCE SCHNEIER | @SchneierBlog

Blog: Schneier on Security Schneier is an internationally renowned security technologist. He has written 12 books, including Liars and Outliers: Enabling the Trust Society Needs to Thrive, not to mention published hundreds of articles and essays. His blog has is read by over 250,000 people, and he is regularly quoted by the press. Additionally, he regularly testifies before Congress and is an advisory board member for EFF and EPIC, among other organizations. If you could have one infosec-related superpower, what would it be? Most superpowers are pretty lame: super strength, super speed, super sight, super stretchiness. Teleportation would probably be the most useful given my schedule, but for subverting security systems, you can't beat invisibility. You can bypass almost every physical security measure with invisibility, and when you trip an alarm -- say, a motion sensor -- the guards that respond will conclude that you're a false alarm. Oh, you want an “infosec” superpower. Hmmm. The ability to detect the origin of packets? The ability to bypass firewalls without a sound? The ability to mimic anyone’s biometric? Those are all too techy for me. Maybe the ability to translate my thoughts into articles and books without going through the tedious process of writing. But then, what would I do on long airplane flights? So maybe I need teleportation after all.
LEIGH HONEYWELL | @hypatiadotca

Blog: Hypatia Honeywell’s views on security-related events, especially her perspectives on geek feminism, are invaluable in our field. We are therefore honored that PeerReach ranked us together among the Top 100 Infosec Worldwide Twitter accounts. Looking ahead, we are confident that Honeywell’s voice will only grow in reach and repute as more women choose to embrace infosec. If you could have one infosec-related superpower, what would it be? As I sit here in Auckland airport en route home from speaking at Kiwicon, my infosec superpower would definitely be teleportation, to make it easier to get to hang out with the friends around the world I've made over my years in the field.
RICK HOLLAND | @rickhholland

Blog: Rick Holland's Blog Holland is Principal Analyst at Forrester Research and currently serves as the Founding Board Member of the Security Advisor Alliance. He speaks regularly at a variety of security conferences, including the RSA conference and SANS summits. He also is frequently quoted by the media and is invited to speak at the University of Texas at Dallas as a guest lecturer. If you could have one infosec-related superpower, what would it be? My infosec superpower would be similar to perennial X-Men villain Magneto’s ability to control and manipulate metal, except that my power would be over network packets. I would be able to identify and strip out any malicious packets targeting my enterprise. Given our lack of ability to detect and contain intrusions, this could be the silver bullet we have all been waiting for. If I were so inclined, I could also reverse these malicious packets and target them back at the original source in the most epic of hack-backs.
JAVVAD MALIK | @J4vv4D

Blog: J4vv4D Malik is a Security Analyst at The 451 Group and co-founder of Security B-Sides London. His Twitter account, per his own words, represents an “unholy alliance between information security and cynicism wrapped up in storytelling and YouTube”—a truly unique and productive approach to security. If you could have one infosec-related superpower, what would it be? Can I name two super powers? One option could be the ability to gain root on any system. I’d be the guardian of the Internet and only say one line, “I am root.” Or I’d be attribution man. I’d want the ability to attribute every ping, scan, poke, comment or any activity back to the true and original perpetrator.
JAYSON E. STREET | @jaysonstreet

Blog: f0rb1dd3n Street is an Infosec Ranger at Pwnie Express, as well as the Founder and Hacker for Hire at Stratagem 1 Solutions. He is author of Dissecting the Hack: The F0rb1dd3n Network and has presented at a number of security conferences, including Def Con. We are grateful that Street revealed his security mentor for us in an article back in the fall of 2013. If you could have one infosec-related superpower, what would it be My Infosec superpower would be communication. I would not only be able to speak in terms and ways that management, developers and users would understand. I would also be able to listen and understand what they were telling me! Which would help me be in a better position to protect and defend our networks. I think that is a super power worth having!
JENNIFER MINELLA | @jjx

Blog: Security Uncorked Jennifer Minella is a Contributing Analyst at Securosis and currently serves on the (ISC)2 Board of Directors. She has been named among the top women in security by SC Magazine and Information Security Buzz, and in November, NCTA announced her as 2014’s Tech Woman of the Year. Acknowledging her influence, we are pleased that she contributed to one of our articles about women being underrepresented in infosec. If you could have one infosec-related superpower, what would it be? There are so many super powers I’d love to have. Most of them would be useless 99% of the time, but fantastic parlor tricks. Like gravity control; who wouldn’t love that!? For InfoSec though, I’d have to narrow the field to: precognition, time travel or skill mimicry. Skill mimicry might be too little, too late, so we turn to precognition and time travel -- which would yield similar results. Both a DeLorean and Einstein have demonstrated that time travel really screws with the whole space-time continuum, so to play it safe I’d have to pick precognition. Wouldn’t it be great to know what would happen and save yourself (your company, or your data) from something bad before it came to be?
BRIAN KREBS | @briankrebs

Blog: Krebs on Security Krebs is well known as an independent investigative journalist of all things security-related. He commonly breaks stories in our industry, providing a calm, rational analysis of each and every incident. As such, he has informed numerous articles that we have published on our blog. For more of his insights, you can read his newest book Spam Nation: The Inside Story of Organized Cybercrime -- a New York Times best seller. If you could have one infosec-related superpower, what would it be? It would be to turn any DoS or DDoS attack back on its attacker (not the hosts doing the attacking, mind you). I realize this isn't technically feasible in many cases, but you said I had a superpower so as long as we're playing make-believe, then that's what it would be. These DDoS attacks are so disruptive and time-wasting; the Internet would be a much better and productive place without them.
DAVE LEWIS | @gattaca

Blog: Liquid Matrix Lewis is a Security Senior Advocate at Akamai who shares Tweets on security conferences and the day-to-day challenges (and humorous moments) of working in our field. We are grateful that we were able to capture a bit of his perspective when we interviewed him, along with Javvad Malik, about why conferences like Black Hat and Defcon are so important. If you could have one infosec-related superpower, what would it be? If I could have an Infosec super power, it would be like Wolverine, to have to ability to heal web servers and networks dynamically and then use my claws to put an end to the problem. All the while chomping on a cigar.
KATIE MOUSSOURIS | @k8em0

Blog: HackerOne Moussouris is the Chief Policy Officer at HackerOne. She has extensive experience in the field, having worked at Microsoft and Symantec for several years. SC Magazine recently named Moussouris among 2014’s Top Women in IT Security, and she has spoken at a number of high-profile conferences, including RSA. If you could have one infosec-related superpower, what would it be? I would like to see all the available patches for every system applied. Since most vulnerability exploitation today occurs using vulnerabilities for which a patch is already available, this action would force attackers to burn 0-day at a faster rate. Each time a new attack took place, another set of vulnerabilities could be detected and then fixed. If the cycle continued, not only would more issues be exposed and fixed, but the window of exploitation would be smaller.
JACK DANIEL | @jack_daniel
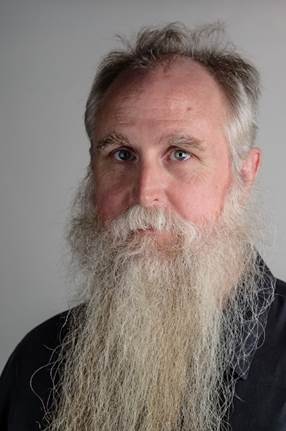
Blog: Uncommon Sense Security A self-proclaimed “information security curmudgeon,” Daniel is the Security BSides Co-Founder and a strategist at Tenable Network Security. He is also co-host of the Security Weekly podcast. Daniel has a knack for putting things into perspective, something that we at Tripwire value. Recently, helped explain on our blog that all conferences, both big and small, help to support the infosec community. If you could have one infosec-related superpower, what would it be? I think “InfoSec Superpower” is an oxymoron. Security needs to be an integral and a foundational part of an organization to be effective. “Superpower” implies something special, and what we actually need is to be so good we become mundane. But, indulging in the fantasy, I would love the InfoSec Superpower of Attribution. Imagine it, FUD, misinformation, and confusion everywhere, but along comes Attribution Man, beard flowing in the breeze, streaming a trail of truth behind me. Dream with me: “Unnamed sources say DPRK behind latest APT…” NO, that’s nonsense! A smokescreen for poor security! “An email purported to be from…” Purported maybe, but it came from a PR agency! “Appears to be the work of Anonymous…” NO, it’s a false flag event; it is budget time! “The attack has been attributed to…” OK, look, you got one right. Great kid. Don’t get cocky.
DWAYNE MELANCON | @ThatDwayne

Blog: The State of Security Melancon is the CTO of Tripwire. Not only does he oversee the functions of our blog, but he has also contributed a number of posts himself. Melancon is well respected in the information security field and is a regular speaker at a number of our industry’s better known conferences. On the side, he runs Genuine Curisosity, where he talks about security, tech, health, travel and other general interest topics. If you could have one infosec-related superpower, what would it be? I’d be one of those multi-faceted superheroes. I would have the power of proportional security response. Regardless of the threat or security issue, I’d instantly be able to marshal exactly the right type and amount of security countermeasures to mitigate the threat. Additionally, I’d have the ability to securely configure any infrastructure in the blink of an eye to make it invulnerable to attacks. I would have the ability to instantly determine who is responsible for an attack. Finally, I’d have the power to separate reality from hype and immediately get to the root cause of any situation. I like this collection of abilities because I think too much of enterprise security activities are driven by hype, focused on response (instead of preparation), and lacking in the fundamentals. Lacking those things, I’d settle for unlimited budget and omnipotent, primary decision-making abilities.
BRIAN HONAN | @BrianHonan

Blog: SecurityWatch An author, Founder & Head of Ireland's CSIRT, and Special Advisor on Internet Security to Europol, Honan is an internationally recognized leader in information security. His contributions help shape the world in which we live. Honan also inspires the next generation of infosec professionals by serving as an adjunct lecturer in information security management at the University College of Dublin. If you could have one infosec-related superpower, what would it be? My infosec super power would be the “Power of Persuasion.” The reason for this super power would be to enable me to persuade board directors and senior management to take security seriously; to persuade vendors not to hype their products using FUD; to persuade computer users on how to use their computers and the internet safely; and to persuade governments, law enforcement agencies, courts, and industry leaders to cooperate and invest more time and resources into fighting online crime.
INFOSEC TAYLOR SWIFT | @SwiftOnSecurity

Blog: Swift on Security Infosec Taylor Swift is one of the most popular infosec parody accounts on Twitter. “She” blends security sarcasm with references to the singer Taylor Swift’s songs and life. Infosec Taylor Swift has been featured by numerous publications, including ZDNet and carbonated.tv. We respect the influence she commands and are grateful for making the security profession a little lighter with her posts. If you could have one infosec-related superpower, what would it be If I had a superpower, I would pose this question to everyone who configures, or designs, electronic systems: What is your job? Make a decision. What is your role in society? Don’t be hasty in a response. You have lots of power and knowledge. A gift. And gifts to give. What problems are you solving with those gifts? And whose problems are they? Is your neighbor any more secure by the things you build and the things you preach? Or do you betray them from your ivory tower by abandoning them to the wolves you empower? What is a gift, used only to build things the common cannot operate? Tools by which they are victimized for thinking you built a tool to serve them, rather than people only like yourself? Building that isn't a gift. It’s a curse. So tell me again. What is your job?
JOSH CORMAN | @joshcorman
Blog: Cognitive Dissidents Corman is Chief Technology Officer at Sonatype. His experience in the field is extensive; he spent several years in management roles at IBM Security Systems, the 451 Research Group, and Akamai Technologies. Given his level of expertise, Corman has been invited to speak at RSA and Def Con and has been featured by CSO Online, among other publications. If you could have one infosec-related superpower, what would it be? Empathy. Security is great at finding WHAT is flawed or HOW we broke it, but less so WHY it matters. We're weaker at listening, compromising, translating, or being ambassadors to stakeholders out of the echo chamber. When launching our cyber safety initiative “I am The Cavalry”, @k8em0 said: “If we're going to change the world, we need to change ourselves. We have an Empathy Deficit.” Empathy is a muscle; you can build it. We've succeeded by meeting others at their level/terminology and internalizing their realities. Bonus: Empathy makes us more effective at work and with our loved ones. This super power is available to anyone. Don't forget to follow these influential infosec leaders on Twitter. You can find a Twitter List with all 22 here!
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

