
The nation’s critical infrastructure experienced a 20 percent increase in cyber incidents in the fiscal year 2015, said government experts.
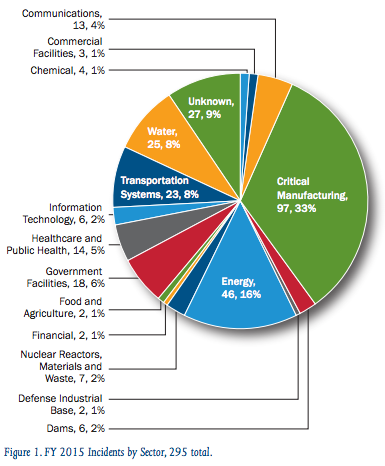
Source: ICS-CERT According to an end-of-year report by the Industrial Control Systems Cybersecurity Emergency Response Team (ICS-CERT), investigators responded to 295 reported incidents involving critical infrastructure in the U.S., compared to 245 in the previous year. The critical manufacturing sector was the most commonly targeted with 97 reported attacks, representing 33 percent of the total incidents. “This increase over previous years . . . is primarily related to a widespread spear-phishing campaign that targeted critical manufacturing companies along with limited targets in other sectors,” read the ICS-CERT report. Companies in the energy sector were also among the top targets, which reported 46 incidents in 2015; water and transportation systems followed, reporting a total of 25 and 23 incidents, respectively.
“While sophisticated intrusions against asset owners persist, in FY 2015, ICS-CERT responded to a significant number of incidents enabled by insufficiently architected networks,” explained the report.
Such incidents included ICS networks being directly connected to the Internet or to corporate networks, where spear-phishing could enable access. It is unclear whether this trend was a change in targeting by adversaries or if these systems merely represented targets of opportunity, states the report. “Regardless of the cause, this reinforces the need for asset owners/operators to focus on security fundaments,” said ICS-CERT. The report also outlines the various techniques used in the intrusion attempts on critical infrastructure systems. Although, in most cases (38 percent), investigators could not identify the initial infection vector, more than 100 incidents involved spear phishing (37 percent). Other common techniques included network scanning/probing (9 percent) and weak authentication (6 percent). Fortunately, the majority of incidents investigated by ICS-CERT (69 percent) had no evidence of successful intrusion into the asset owner’s environment. However, 12 percent of incidents observed in FY 2015 did, in fact, have evidence of intrusion into the control system environment. The report does not state whether any proprietary or critical information was stolen during these reported attacks. For more information, read the full ICS-CERT Fiscal Year 2015: Final Incident Response Statistics report here (page 4).

