
Sometimes things would be better if people didn't keep their word. Take hackers, for instance. Hackers using the online handle "DotGovs" published information about 9,000 Department of Homeland Security (DHS) workers earlier this week after stealing it from the Department of Justice's intranet. Many of us probably hoped that DotGovs couldn't be relied upon to keep their promise of following-up by also releasing the details of some 20,000 FBI officials. And yet, on Monday evening, DotGovs posted a message on Twitter claiming to have released the information to the same place where they had distributed the earlier DHS dump - CryptoBin.org.

If you haven't heard of CryptoBin before, it's similar to PasteBin. Launched in 2011, it describes itself as "a secure pastebin service" that allows posters to encrypt their submissions. In order to view the encrypted content, you have to enter a password.
So, you would imagine that interested parties are right now visiting the CryptoBin link that DotGovs tweeted, entering the password ("lol") and taking a gander at the list of supposed FBI employees, their job titles, phone numbers and email addresses. However, if you go to CryptoBin.org right now this is what you will see.
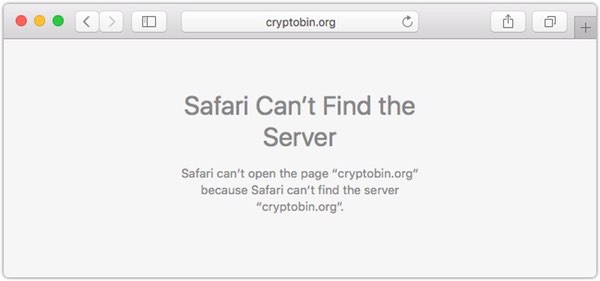
Yes, currently CryptoBin is only accessible through its numeric IP address (151.236.7.117) as its alphabetic address appears to have gone kaput. Furthermore, the paste which the hackers claimed contained the details of 20,000 FBI staff is no longer accessible. It is possible that the authorities have made it harder access CryptoBin in an attempt to prevent further potentially damaging information from leaking out? It's hard to say for certain, and judging by their recent tweets DotGovs seems be losing interest in this particular game:
FBI and DHS info is dropped and that's all we came to do, so now its time to go, bye folks! #FreePalestine Anyone got a good lawyer ?!?!?
Whether DotGovs is joking about needing legal representation, or genuinely believes that the FBI are hot on his heels remains a mystery - as does quite what has happened to CryptoBin. Whatever is going on with CryptoBin, one thing is clear. After hacking a single DOJ staffer's email account, a hacker was able to socially engineer a support desk into handing over an authentication code that allowed access to the organisation's web portal. And from there it seems to have been trivial to access work PCs and download the database of workers. We can patch computers all we like, and introduce layered security to reduce our exposure to threat, but as long as humans continue to make simple mistakes hackers will continue to take advantage. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

