
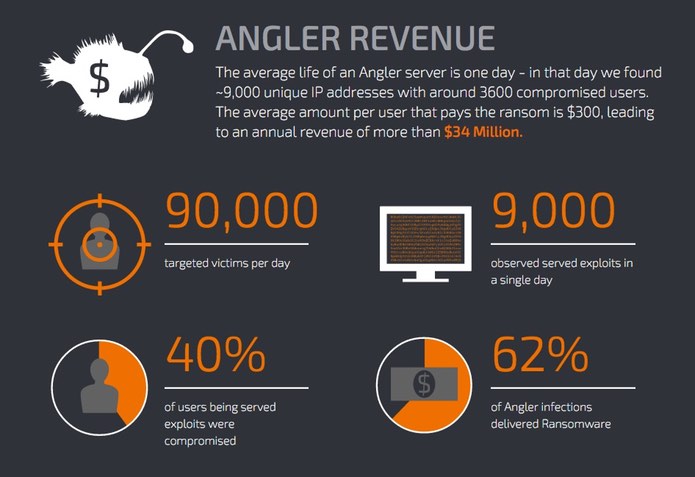
The internet is a little bit safer today, and that is something we should all be grateful for. The reason? Security researchers have taken on organised criminal gangs who have been using the notorious Angler Exploit Kit in malware campaigns stealing up to $3 million each month through ransomware attacks. The Angler Exploit Kit is a prime weapon in the arsenal of online criminals, helping them to infect vulnerable computers with malware through compromised legitimate websites as well as sites controlled by the hackers themselves. In over 60% of the cases, the malware installed by such attacks was the CryptoWall or TeslaCrypt ransomware, designed to take users' computers hostage, demanding a ransom be paid in order to regain access to the device or files. Cisco's Talos Security Intelligence and Research Group have analysed the Angler Exploit Kit closely in recent months, and came across evidence that up to 90,000 innocent victims were being targeted each day, earning crime gangs potentially more than $30 million annually.
But further than this, the researchers determined that the primary locations for the proxy servers used by the exploit kit were hosted on servers belonging to Dallas-based Limestone Networks and Bavarian firm Hetzner, as the following graph of IP addresses used by Angler during July 2015 demonstrates.
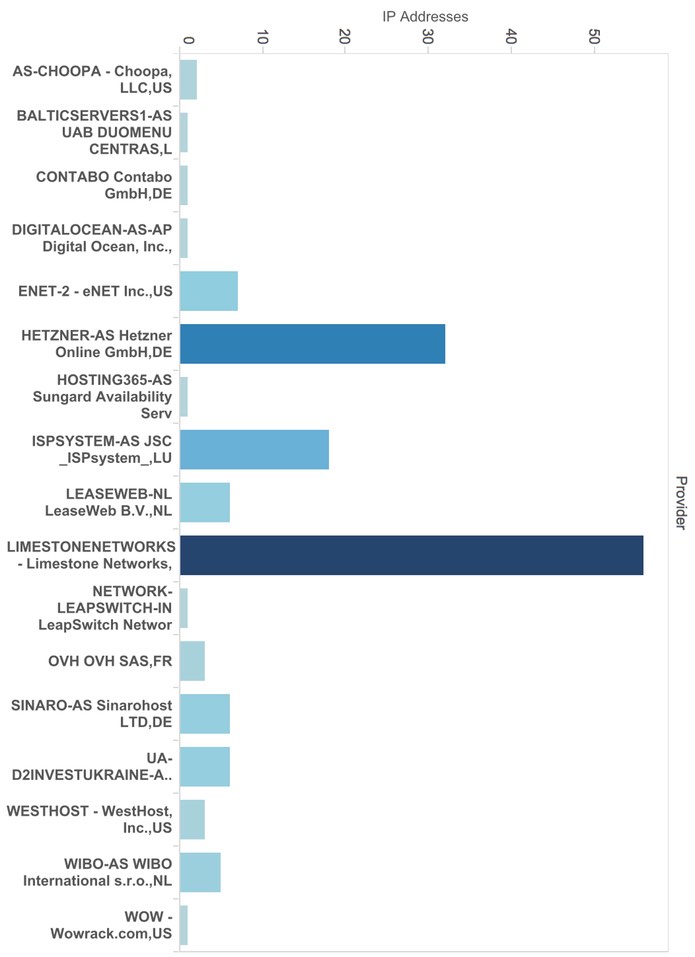
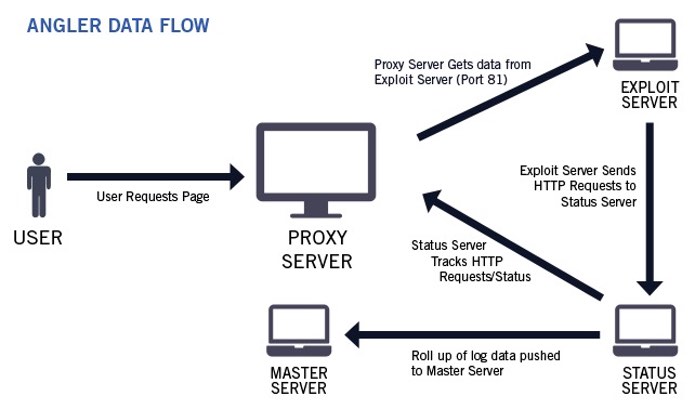
Talos says that it reached out to Limestone and Hetzner, and received a response and co-operation from Limestone, who helped provide information that built a picture of how the criminals had architected their infrastructure. It transpired that Limestone was suffering to the tune of $10,000 in cost and lost revenue each month due to gangs using the company's services to assist their Angler Exploit Kit campaigns, much of it due to charge backs due to fraudulent credit card use. After analysing the operation of the exploit kit on Limestone's systems, Cisco updates its networking products to block redirects to Angler's proxy servers, effectively protecting customers from infections. In this way, something like 50% of all malicious activity connected to the Angler Exploit Kit has been nullified. The result of action being taken against Angler's abuse of Limestone's infrastructure has been dramatic. During the month of July 2015, for instance, more than a third of the IP addresses serving up the Angler Exploit Kit were hosted by Limestone Networks. The trend continued during August, albeit in lower volume. Today, the activity has stopped on Limestone's infrastructure.
"With the help of Talos, Angler has stopped using them as a source of malicious activity, both saving Limestone money and eliminating one more conduit for Angler to exploit. Limestone Networks was also able to provide us with copies of images of the servers that were being used as well as network captures of the communications the servers were conducting for short time periods. As a result of this Talos was able to get valuable information that exposed previously undisclosed aspects of Angler, as well as the scope of the users impacted."
We shouldn't fool ourselves into thinking that Cisco's action will serve a killer blow to the Angler Exploit Kit, but it will have bloodied its nose and disrupted the criminals' activities. Of course, the organised criminals behind such attacks are not going to roll over and give up. They will be back, looking for alternative mechanisms and web hosting services to help them infect unsuspecting web users' computers. All the same, we owe the security community our thanks for working tirelessly in co-operation to make the internet that little bit safer today. For further information be sure to read the full report from Cisco's Talos security researchers.

