
Regularly in the news we hear about organisations having their Twitter or Facebook accounts compromised by cybercriminals - but they're not the only social media outlets which hackers and fraudsters have an interest in hijacking. Researchers at Symantec have warned this week of an increasing number of phishing emails being spammed out, claiming to come from LinkedIn's support team.
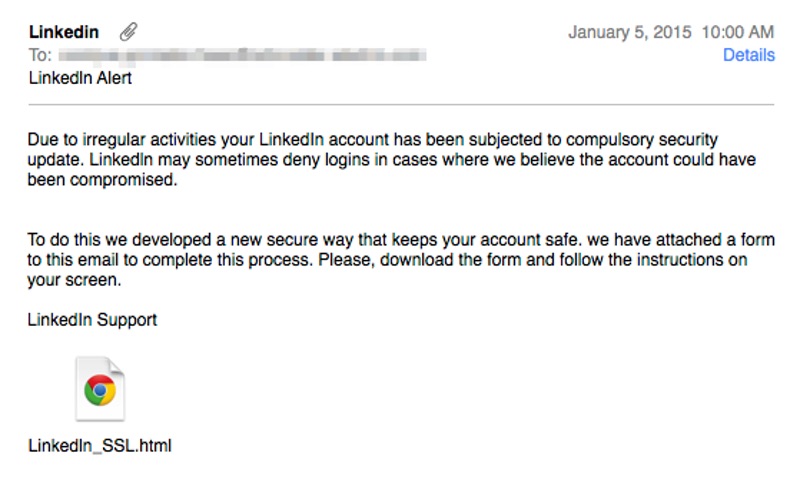
Due to irregular activities your Linkedln account has been subjected to compulsory security update. Linkedln may sometimes deny logins in cases where we believe the account could have been compromised. To do this we developed a new secure way that keeps your account safe. we have attached a form to this email to complete the process. Please, download and follow the instructions on your screen. Linkedln Support
Attached to the email is an HTML file, which contains a copy of the genuine LinkedIn webpage - albeit changed in one significant way. If you open the boobytrapped HTML file and enter your login credentials they will be sent to the cybercriminals.
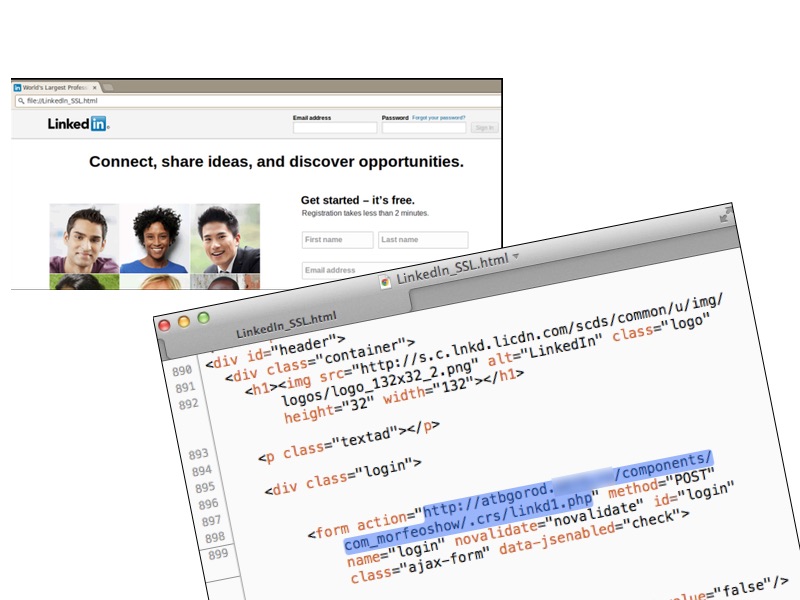
Of course, what's clever about an attack like this is the social engineering involved. The email plays on your security fears, worrying that your LinkedIn account may have been or may become compromised. Ironically, whoever is behind the email is planning to do precisely that! And when the email says that it contains a "new secure way that keeps your account safe", opening and acting upon the attachment is actually the very worst thing you can do. Now, you may think to yourself that you're a cynical old IT security greybeard, who wouldn't fall for a trick like this. But can you say that's true of everybody else at your company? You may have encountered plenty of dodgy emails in your time, and be able to sniff out unusual behaviour - but can you be sure that your staff are not more trusting? The risk is that one of your colleagues could fall for a trick this, and hand control of their account over to online criminals. Once the phishers have control of the account they can pose more convincingly as a member of your organisation, and potentially abuse the business relationships the victim has built up over time for their own criminal and fraudulent purposes. After all, people are far more likely to trust a message which arrives in their LinkedIn inbox with a friend or colleague's mugshot and work profile alongside it, than one which arrives out of the blue in their email intray. One peculiarity in the attack which many people may not notice is that in the email "LinkedIn" is spelt with a lowercase "l" rather than a capital "I". Chances are that the criminals are abusing the (frankly absurd) similarity when these letters are written using the Arial or Helvetica font, in an attempt to avoid spam filters. The confusion between "I" (the uppercase ninth letter of the alphabet) and "l" (the lowercase twelth) has long been one that cybercriminals and fraudsters have been able to use to their advantage. Teach your staff to be careful of unsolicited messages that contain HTML attachments, as they could be attempting to scam credentials. In addition, ensure that LinkedIn accounts are properly hardened against attacks by enabling two-factor authentication. LinkedIn has had its own form of two-factor authentication (2FA), which they call two-step verification, since 2013. At the time, the business network wrote:
"Most internet accounts that become compromised are illegitimately accessed from a new or unknown computer (or device). Two-step verification helps address this problem by requiring you to type a numeric code when logging in from an unrecognized device for the first time. This code will be sent to your phone via SMS. When enabled, two-step verification makes it more difficult for unauthorized users to access your account, requiring them to have both your password and access to your mobile phone."
Enabling 2FA on LinkedIn means that having your username and password isn't going to be enough for a hacker to gain access to your account. You can turn on LinkedIn's two-step verification by going to Settings, clicking on the Account tab and choosing the Manage security settings option.
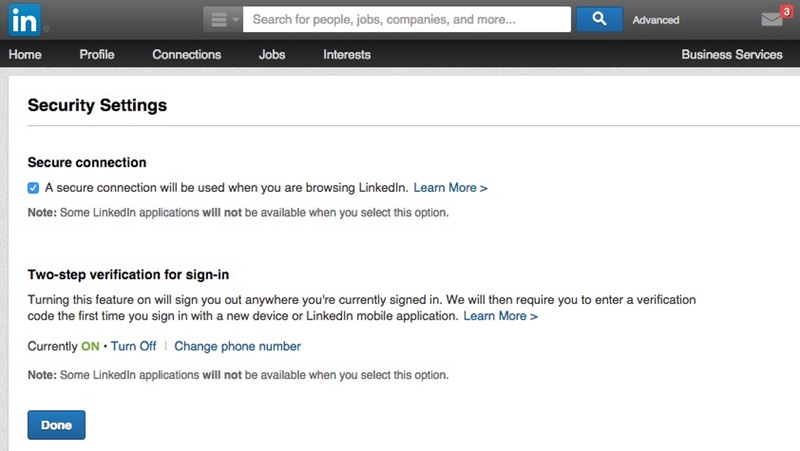
In addition, on this screen you will also be able to tell LinkedIn to always use SSL. In the past, hacked LinkedIn accounts have been used to distribute malicious links, spam out pump-and-dump scams, and defraud business workers. Reduce the chances of that happening to your company by educating your staff, and ensuring that they're doing everything possible to reduce the chances of it being their LinkedIn account that next gets compromised.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

