
Data breaches at large companies, such as Target or Home Depot, call to mind concerns about cloud infrastructure security. However, does the media do these cases justice, or is security in the cloud actually better than ever?
How do medium and large businesses – enterprises – perceive cloud security systems?
Cloud security is both a benefit and cause for concern for enterprises, according to a new study about the state of cloud security in the enterprise market. While businesses ranked security as the number one benefit of cloud computing, they also named it the most frequently encountered challenge. These mixed feelings shed light on not only how enterprises perceive the benefits of cloud computing but also how they can combat concerns about security to take full advantage of the platform.
Cloud Security Nay Sayers
With more than 90 percent of businesses using cloud infrastructure and most using the platform to store mission critical data, concerns about privacy and data security remain prominent. Part of what perpetuates the myth of cloud computing as a security risk is media coverage of high-profile attacks. For example, tens of millions of customers’ credit card numbers were compromised after a security breach at both Target and Home Depot in 2014. Additionally, the controversial Apple iCloud hack resulted in the publication of numerous nude images of celebrities. However, these narratives ignore that the security breaches had nothing to do with weaknesses in the cloud.
- The Target breach occurred because a third party had access to the company’s network and hackers stole the third party’s login credentials.
- The incident at Home Depot mirrors the Target case, with hackers stealing a vendor’s login, accessing the network, and using custom malware to go around Home Depot’s antivirus software.
- Finally, even the Apple iCloud hack occurred indirectly, with hackers accessing celebrity accounts using brute force and phishing.
Trusting your data to a cloud service provider (CSP) is actually much safer than using an on-premise data storage solution. CSPs simply have more resources to dedicate to security.
“Many recent data breaches have been reported incorrectly. … No one was hacking the cloud. It was human error, and the cloud cannot protect you from that,” explains Jason Reichl, CEO of Go Nimbly.
Cloud Security Versus Legacy Systems
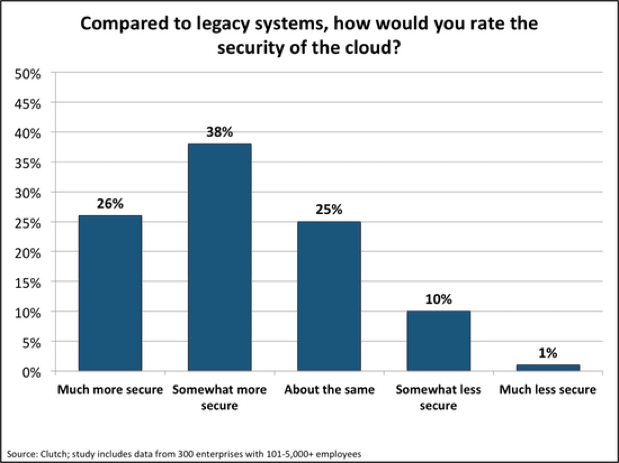
As cloud computing technology has evolved and improved throughout the past few years, businesses’ impressions of cloud security systems have transformed, as well. In fact, 64 percent of enterprises believe cloud infrastructure is more secure than legacy systems.
"A couple years ago, security in the cloud was the biggest concern, and it is what prevented a lot of companies from adopting the cloud," explains Jose Alvarez, Director of IT Infrastructure, Auxis. "But these days, the cloud offers more security than an on-premise platform because cloud vendors have developed tools and services to monitor and react quickly to security threats or attacks."
What features make cloud infrastructure a more secure option? According to industry thought leaders, distrust of the cloud often arises from a lack of knowledge about the security safeguards cloud service providers use to keep data safe. These safeguards include:
- 24-7 monitoring;
- Multi-layered security measures, such as encryption, standards and compliance and identity-based access policies; and
- Proactive management structures that ensure quick reactions to security breaches and continuous security updates.
Overlapping Benefits and Challenges of Cloud Computing
Overall, nearly half of enterprises (47 percent) identify increased efficiency as the main benefit of cloud computing. However, when asked to rank a list of features from one to three, with one signifying the primary benefit of cloud computing, security comes out on top.
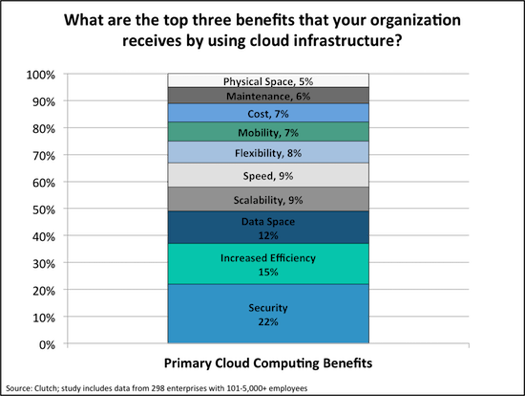
Although the cloud may be more recognized for the other benefits it offers, such as increased efficiency, scalability, and speed, newfound trust in cloud security systems is a positive sign for the technology.
"Using the Cloud is like putting your money in the bank versus under your mattress," observes David Linthicum, Senior Vice President, Cloud Technology Partners. "Even though your money, or data, is not on-premise, the bank will do a much better job protecting it because it has vaults and security cameras – more than what a single enterprise company can do."
At the same time, enterprises indicated that security was the challenge they encountered most frequently with cloud computing, followed by training and cost. This trend suggests that migrating to the cloud raises awareness about data insecurity and triggers a flurry of activity to implement the property security structures. Reichl, CEO of Go Nimbly, points out that in reality, companies should already have implemented security measures, but migrating to the cloud seems to make the need for data security more apparent.
Additional Security Measures Offset Concerns About Security in the Cloud
Is the cloud secure enough on its own, out-of-the-box? Additional security protections are necessary when using cloud infrastructure, according to industry leaders.
"In reality, the Cloud has two major components: the backend cloud vendor infrastructure, which is secured by the vendor, and the company-specific cloud infrastructure, which must be secured by the company," notes Alvarez.
This means businesses must identify weaknesses in their cloud platforms and fill in the gaps based on their needs. Amplified cognizance of the type of security structures that are needed actually leads to better security practices overall.
Closing Reflections
Thoughts on security will continue to change as cloud infrastructure technology improves over time. The positive outlook expressed in the study hints at a bright future for cloud computing. As more businesses overcome their security concerns and embrace the cloud, the platform’s benefits will become even clearer.
About the Author: Sarah Patrick is an analyst at Clutch. As a member of the marketing team, she conducts research that aims to help consumers select agencies and firms and use IT services and software that enhance their business. Clutch is a Washington, DC-based research, reviews, and ratings platform for B2B. It identifies leading software and professional services firms that deliver results for their clients. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc. Title image courtesy of ShutterStock

