
When it comes to known unknowns, there is one fact you can be sure of, which is based on the conundrum of “Am I being, or have I been hacked?” – with the knowing component here representing the high probability that the answer is in the affirmative. However, when reflecting on the unknown element, this may well result in a number of unknown answers to a number of valid questions, such as when, target, timeline, asset(s), exposure, and impact. OK, so it may be that some readers may feel that such a state of the unknown is the product of an overactive brain, looking towards the darker side of expectations. Sadly, this opinion is based on reflective facts drawn from the real world concerning utility companies, the financial services sector and government institutions who suffered incursions from unaccounted sources, manifesting in the unknown impact resulting from the late detection of an in-flight, or historical breach. In fact, according to a report released by the Ponemon Institute, once a data breach occurs, it takes 98 days – on average – for financial services companies to detect the incursion on their networks and 197 days in the retail sector, allowing a much extended window of undetected manipulation to exist, which has been known on a number of occasions to offer unfettered access to critical systems and data assets. So, kicking off on the premise that we live in a technological society in which bad things can happen, linked to the expectation that adverse conditions will be encountered which implicate organisational assets and operations – let’s set the accepted scene that you have been, or will be hacked. Here, I will expand on my last Tripwire blog Ten Keys to Cyber Survival, and drill down into some of the internal components, which can enrich the outcome of incident management. Upon an actual or suspected security incident being encountered is not the time to work out how the empowered team will operate – and this is most certainly not the time for making it up as you go along. The recommended approach here is to identify and map those common attack vectors and eventualities, and then to create what are referred to as run-books, story-boards, or incident response process charts, which lay down the steps that will be followed by the CSIRT/First Responder when engaging an incident to both protect and to mitigate social, or logical adversity. For example, start by drawing up your top areas of encountered events and with the benefit of hindsight, create the documented process which will be introduced into your security team, SOC and CSIRT. Here are five suggested run-books which fill a gap:
- DDoS Attacks
- Malware Incidents
- Ransomware
- Cyber Extortion
- Unauthorised Exfiltration (such as DPA, or PCI-DSS)
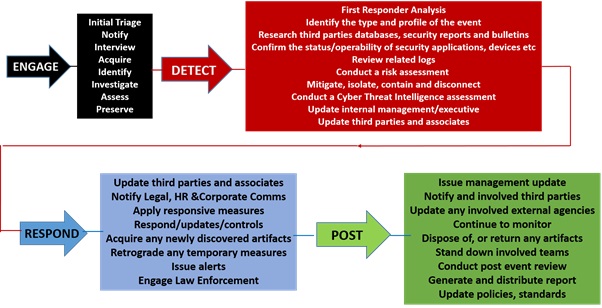
Upon a security team or CSIRT implementing such an approach, there will be an immediate realization of the benefits delivered out of such robust processes, realizing consistency, guidance, and a one-fit-for-all with globalized CSIRT communities. Another benefit of a well-ordered framework of documents will empower junior members of the team by making available the agreed protocols of engagement, which will underpin the First Responder when under stressful working conditions. As an example here, take a look at the images below which show an extract from a run-book:
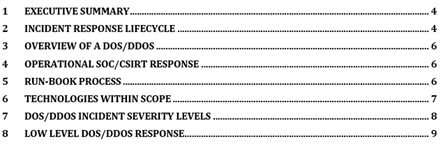
Run-Book Content Listing
Along with a high-level view of what is documented within the body of the document as shown below:
High Level CSIRT Engagement Process
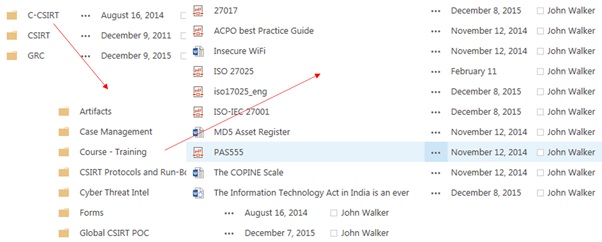
There is, of course, an operational expectation that the CSIRT will be provisioned with underpinning supporting components, such as a case management/CSIRT framework that accommodates any current, or past investigations. And contrary to commercial opinion, if funds are low such an operational environment may be developed on a platform like SharePoint, which can be effectively leveraged to deliver an adequate level of cost-effective service. In fact, I have delivered such a system into one operational environment located in Dubai, which has now evolved into a full-blown appliance, providing a portal and repositories storing run-books, tools and other such CSIRT dependent operational instruments. The other value-add out of using SharePoint is it may be attached within Outlook as a sub-folder, ensuring that the First Responder has a Martini type experience of connectivity, and access to the remote resources (anytime, anywhere). This may not be rocket service, but at the end of the day, it can provide the organization with a very simple solution with which to manage their CSIRT/security engagements. Shown below is a simple example of such a SharePoint folder interrelationship cascade.
SharePoint Delivery
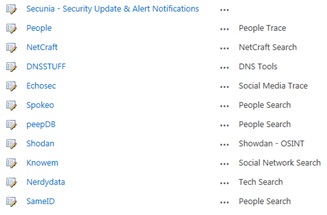
Another important element for the CSIRT First Responder is having the available tools and online resources to conduct a Cyber Threat Assessment Triage – to take a look at any hostile actors, or potential adversaries. Here again, we can use a single platform populated with tools focusing on online cyber threat Intelligence, OSINT and search capabilities to support the investigation – as shown below in our SharePoint delivery.
Cyber Threat Intelligence, OSINT and Search Capabilities
I fully accept that the above approach is not, as I have repeated throughout this article, anywhere near what could be regarded as rocket science, and for many purists it may not satisfy their high-end expiations – but then this is not the objective. Given the state of the real world, and what I have observed to be missing, it does, however, provision a practical recourse to get the CSIRT and First Responder conversation moving. Furthermore, it has been proven to deliver the cost-effective base capabilities into organizations where nothing existed, providing an environment which may be further exploited and evolved as the organizational function matures. And above all, it does not cost a fortune to deliver – all that is required is a little knowledge and the application of imagination. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc. Title image courtesy of ShutterStock

