
On October 2-4, 2017, the Retail Cyber Intelligence Sharing Center (R-CISC) hosted Securing Retail 002, the second iteration of its annual summit first held in April 2016. Speakers from Microsoft, Target and other Fortune 500 companies shared their thoughts on the retail digital security landscape with attendees over the course of the two-day event. Presented below are some of the top talks from this year's conference along with some amazing visualizations created in real-time by graphic recording artist Kelly Kingman. https://www.slideshare.net/Tripwire/the-top-12-talks-from-the-2017-rcisc-summit
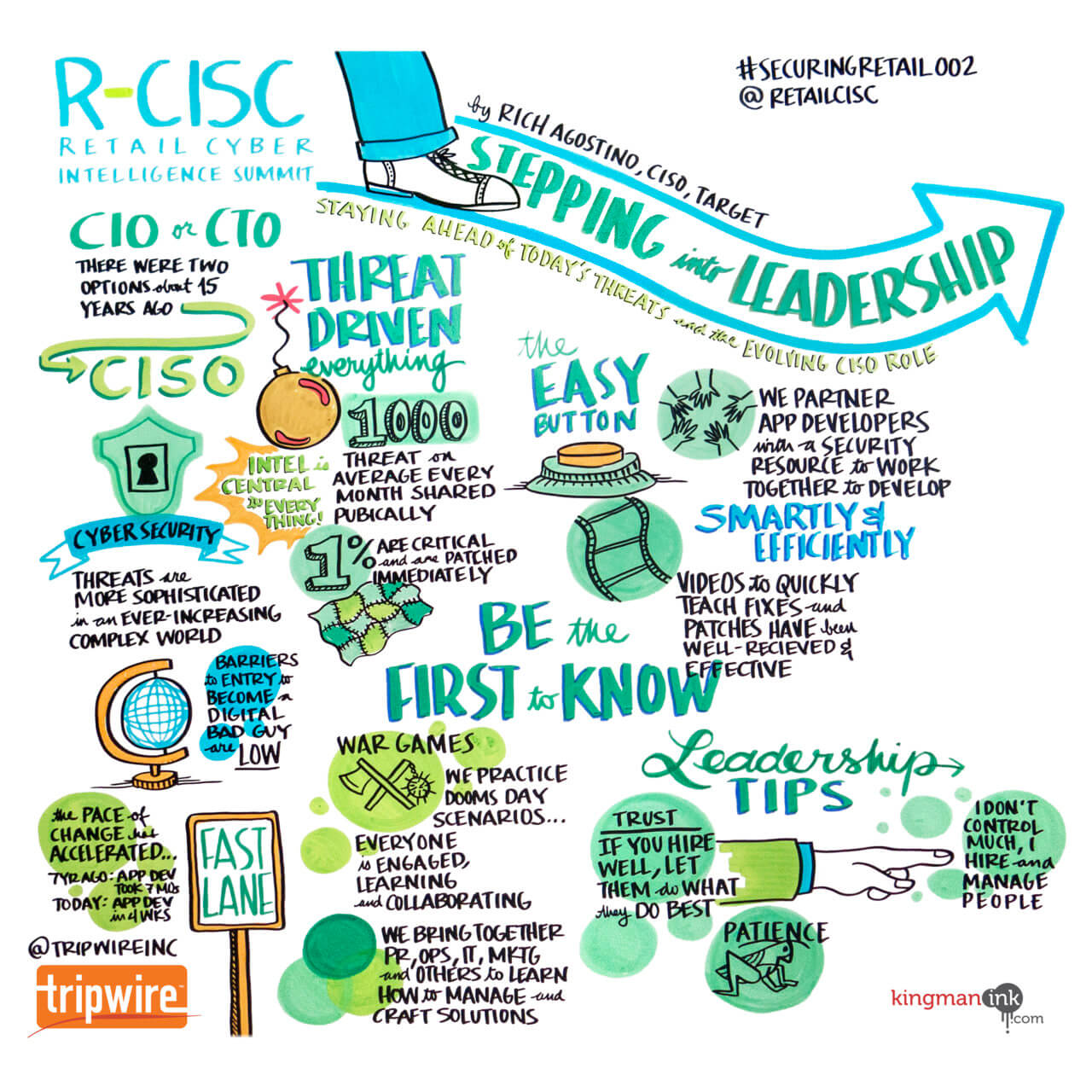
Stepping Into Leadership: Staying Ahead of Today’s Threats and the Evolving CISO Role
Speaker: Rich Agostino, senior vice president and chief information security officer for Target In his presentation, Rich Agostino pointed out that chief information officers (CIOs) and chief technology officers (CTOs) were the only C-level executives in IT 15 years ago. Since then, they've been joined by the chief information security officer (CISO). Agostino then drew upon his experience of elevating Target's digital security practices to discuss what it takes to be a CISO. He said leadership has a lot to do with it. CISOs must hire well and then learn to manage people by bringing together PR, Ops, IT, marketing, and others in an effort to manage and craft solutions. CISOs, he went on to note, should also strive to be the first to know about potential security issues and to partner with app developers who have a security resource so that they can work together to develop smartly and efficiently.
Big Threats, Small Shop: Tracking Major Campaigns with Limited Resources
Speaker: Jason Lay, threat intelligence lead at QVC Developing an effective, efficient, and evolving cybersecurity program requires a targeted approach. A common challenge is a lack of resources, but Jason Lay is of a firm mind that intelligence teams can still leverage preexisting methods for adequate protection. During his talk, he said that it's all about a few major initiatives: establishing intelligence requirements, leveraging strategic communication (what's going on in the industry) and internal intelligence (what's happening on the network), and closing the loop with a "so what" factor. This final element usually consists of analyzing trends and patterns along with discussing insights from major campaigns as well as from low hanging fruit like phishing attacks. Intelligence teams can and should refer to other departments, tools and resources, and security products to help make their point, Lay noted.
The Next Evolution of Information Security
Speaker: Kostas Georgakopoulous, CISO at Procter & Gamble From his experience in financial services, federal-level security investigations, and partnerships with leading security groups and companies, Kostas Georgakopoulous knows that CISOs struggle with three realities: threats, complexity, and budget. At the same time, cyber attackers are getting faster and more sophisticated. Georgakopoulous said in his presentation that CISOs can counter those malicious attackers by using open-sourced capabilities that are already available. Those tools include Wazuh, which allows you to search incidents in just seconds; machine learning; the cloud; and telemetry.
The First Person You Must Lead is You
Speaker: Becky Halstead, retired brigadier general of the U.S. Army and founder of STEADFAST Leadership, LLC Retired Brigadier General Becky Halstead reflected on how her time in the United States Army has shaped her understanding of leadership in the corporate community. To her, leadership means championing change and acting as the "calm in the chaos" through any adjustments that ensue. Halstead also believes that leaders must be authentic to themselves and exercise a healthy dose of curiosity. Only then can they think differently and lead diverse peoples by example so that their team members can feel empowered and claim ownership of the project at hand.
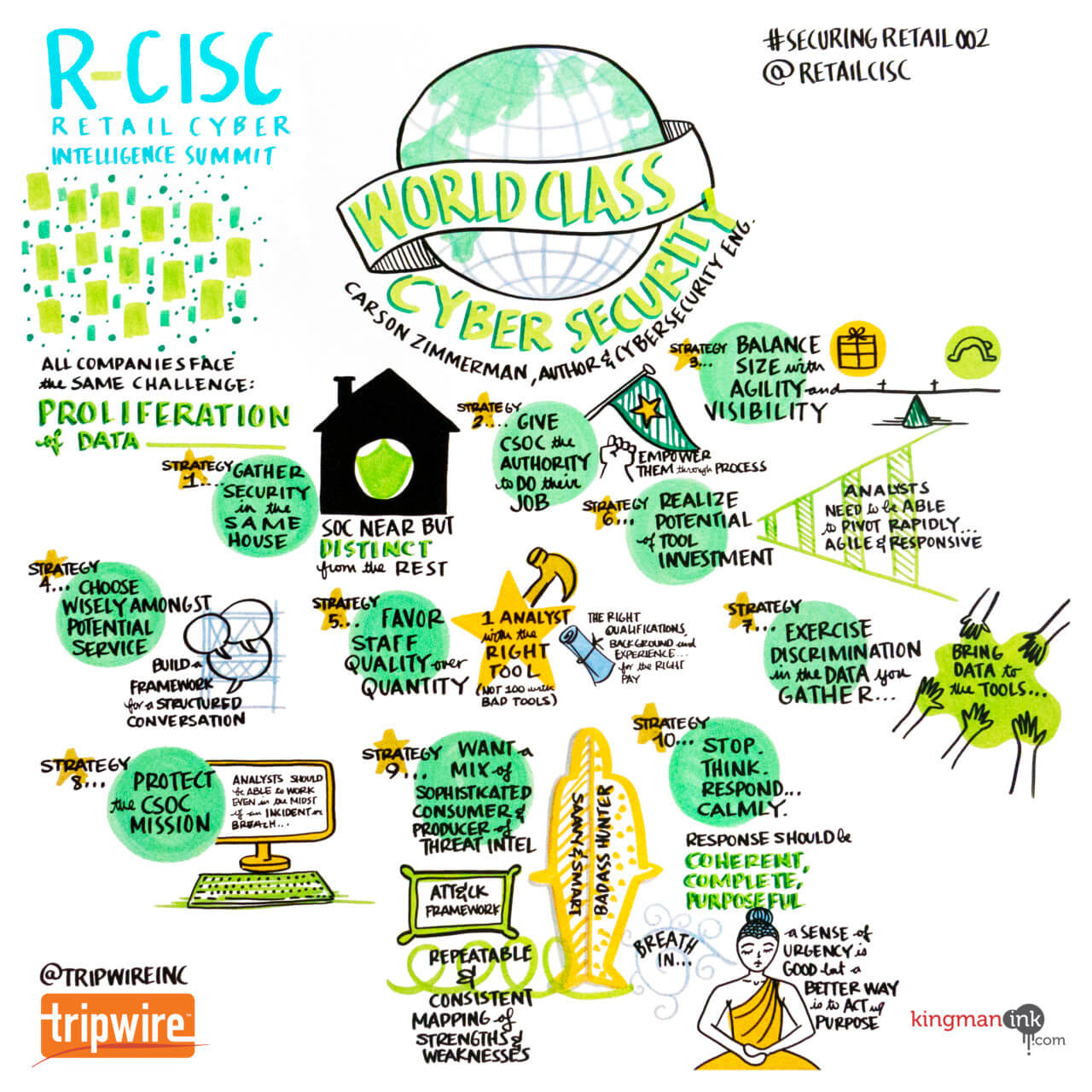
World-Class Cybersecurity Operations
Speaker: Carson Zimmerman, a cyber security operations centers (CSOC) engineering team lead with Microsoft Today’s Cyber Security Operations Centers (CSOCs) should have an array of detection and prevention technologies, a sea of cyber intelligence reporting, and access to a workforce of talented IT professionals to mount defend the ever-changing IT enterprise against ever-evolving digital threats. Currently, many CSOCs fall short in that regard due to the proliferation of data. But they're not powerless to counter it. In his presentation, Carson Zimmerman set out 10 strategies for cyber security operations centers. Those methods included making strategic service decisions, favoring staff quality over quantity, and protecting the CSOC mission.
Navigating Cyber Risk in the Spotlight: The Importance of Being Ready
Speakers: Greg Alexander, vice president and global security advisor for the Priceline Group; Rebecca Janutis, vice president of information security for Kohl’s Department Stores; and Rocco Grillo, executive managing director serving on Stroz Friedberg’s executive management team Greg Alexander, Rebecca Janutis, and Rocco Grillo discussed in their presentation how to limit brand and reputation damage in the wake of a digital security event. Among other things, they pointed out that relationships play an important role in mitigating digital security risk. In particular, they highlighted the relationship between the CEO and CISO as crucial to an organization's digital security strategy. The presenters also explained the benefits of phishing training, insider threat prevention technologies, and strong governance in addressing risk.
The True Cost of Cybercrime
Speaker: Kelly Bissell, global managing director of Accenture Security In his keynote, Kelly Bissell discussed new research from the Ponemon Institute and Accenture that shows how companies' security investments fail to deliver efficiency and effectiveness. Bissell attributed this gap in results to difference of cost vs. value. In general, Bissell said he believes organizations can get better at protection by embracing five business innovations. These changes, he explained, can help strengthen business agility, enhance customers' experience, and help organizations better understand data.
How Leading Security & Fraud Teams Fight Account Takeover
Speaker: Shuman Ghosemajumder is chief technology officer at Shape Security In 2016, more than 3.3 billion credentials were reported stolen, with credential stuffing attacks constituting over 90 percent of the total login traffic on many large retailers. Shuman Ghosemajumder said these figures should motivate retail organizations to protect against account takeover (ATO) attacks. He felt they should begin by defining the problem and then work to develop a framework for protecting clients as well as ensuring collaboration between security and programming. Ghosemajumder also pointed out the importance of machine learning, generalized application defense like two-step verification, and JavaScript finger-printing.
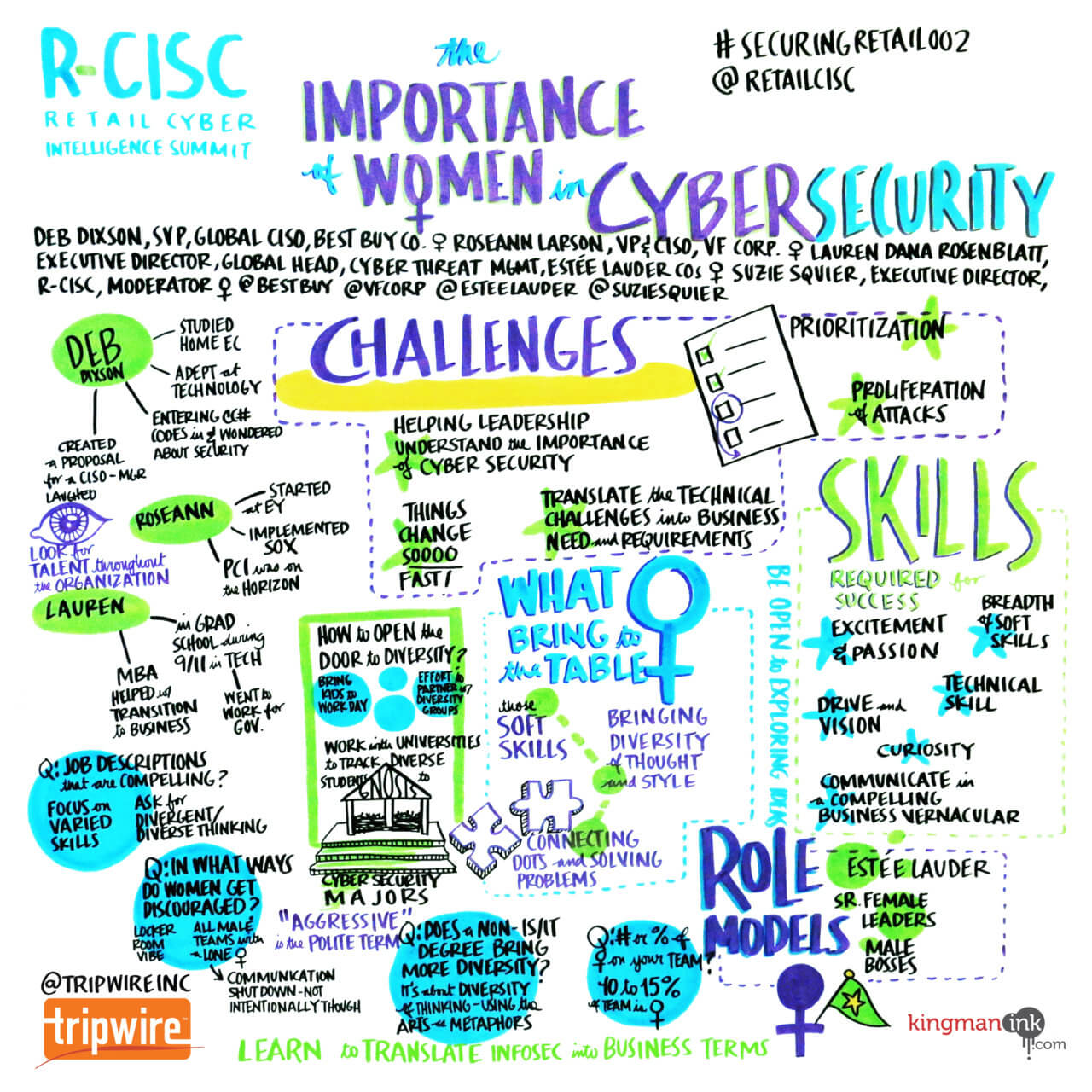
The Importance of Women in Cybersecurity
Speakers: Deborah Dixson, senior vice president of information security and risk at Best Buy Co; Roseann Larson, vice president CISO for VF Corporation; Lauren Dana Rosenblatt, executive director and global head of cyber threat management at The Estée Lauder Companies; and Suzie Squier, executive director of the Retail Cyber Intelligence Sharing Center (R-CISC) According to Women’s Society of Cyberjutsu (WSC) statistic, women represent 11% of the world’s information security workforce. STEM, Cyber Boot Camps, and other programs are helping to attract women to the field, yet an imbalance persists. In this inspiring keynote discussion, leading women in strategic roles within their cybersecurity organizations took on this inequity and reflected on the importance of women in this industry. They shared their stories on how they got involved in security, identified challenges that all security leadership face, and pinpointed specific benefits that women bring to digital security.
The Great Teams Understand “The Why”
Speaker: Don Yaeger, nationally acclaimed inspirational speaker, longtime associate editor of Sports Illustrated and author of 26 books Don Yaeger shared his findings from interviews with Olympic Gold Medal winners to reflect on what makes a great security team. He noted that the best teams know their purpose and whom they are in service of while being acutely aware of downstream beneficiaries. In Yaeger's mind, the best teams are also flexible. They let culture come to them and adapt to change all while upholding a sense of commitment, trust, and honor.
Risk and Fraud Mitigation: Insights from The Front Lines
Speakers: Tim Brewer, vice president of engineering & solution delivery at CashStar; Scott Roubic, vice president of internal audit, asset protection and real estate at Jo-Ann Stores; Michel Huffaker, program manager in threat intelligence and vulnerability management at MGM Resorts International; and Dan Holden, CTO and intelligence director at R-CISC Dan Holden moderated this lively discussion on the expanding threat landscape that confronts retailers of all sizes. Tim Brewer, Scott Roubic, and Michel Huffaker together discussed communication, architecture and technology, brand protection, and a number of other items that organizations should consider when it comes to strengthening their security posture.
Driving Security Operations Efficiency Through Orchestration and Automation
Speakers: Vikram Desai, managing director at Accenture Security, and Scott Howitt, senior vice president CISO for MGM Resorts International More than a third of attempted breaches on retail companies over the past year were successful. In light of this development, Vikram Desai and Scott Howitt revealed that they don't think throwing tools will help organizations better protect themselves. Instead they disclosed their belief that security operations need to be simplified and orchestrated. Towards that end, they discussed an instance where they pushed vendors to talk about how to mitigate risks. The culmination of this meeting was a normalized platform that allows tools to talk to one another. For more information on R-CISC, please visit: http://r-cisc.org/.

