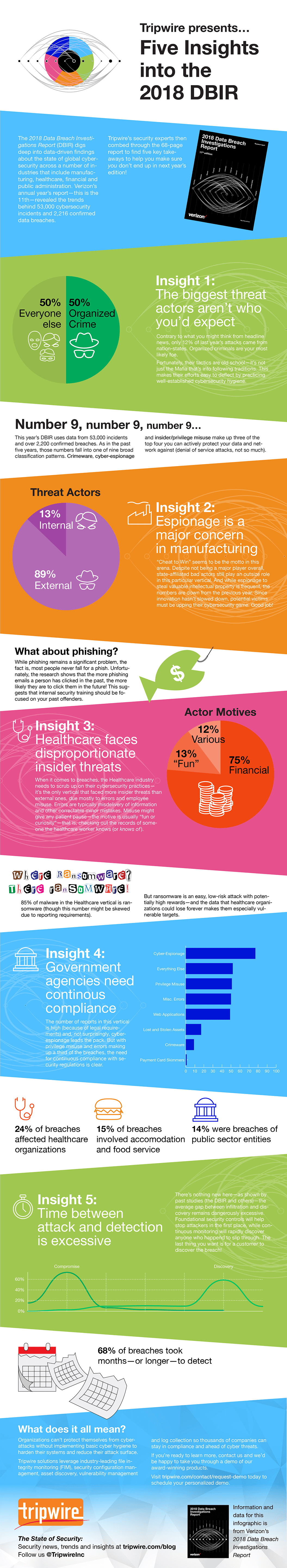
The 2018 Data Breach Investigations Report digs deep into data-driven findings about the state of global cybersecurity across a number of industries that include manufacturing, healthcare, financial and public administration. Verizon’s 11th annual report revealed the trends behind 53,000 cybersecurity incidents and 2,216 confirmed data breaches. As Verizon puts it, “The DBIR was created to provide a place for a security practitioner to look for data-driven, real-world views on what commonly befalls companies with regard to cybercrime.”
Biggest Threat Actors
If you only read headlines, you’d believe that most cybercrime comes from independent hackers or nation states. Organized crime was behind 50% of all breaches, leveraging established tactics. If you’re picturing a Mob Boss in the command line, you are not alone. It’s a strange image. But if it makes you feel any better, these operations are not exactly leading new strategies. They often use established procedures and techniques. If your organization uses best practices or frameworks like MITRE ATT&CK, you’ll be fine. What about phishing? Phishing remains a significant problem, as a bank found out when their cybersecurity insurance refused to pay out for two phishing scams. Contrary to popular belief, most people do not fall for phishing. Those that do, however, are more likely to click phishing emails in the future.
Espionage in Manufacturing
Eighty-nine percent of threat actors in manufacturing are external after valuable intellectual property. However, insider threats are still an issue, as Tesla learned earlier this year. Elon Musk’s electric car company enlisted the help of its lawyers to sue a former employee for allegedly stealing manufacturing secrets. The good news: these numbers are down from 2017. Shady companies will use competitor secrets to make their own goods. Malicious hackers aren’t only after money; some have a bit of national pride. Governments want a competitive leg-up when it comes to international economics. This past May, the FBI warned American router owners to reset and update the firmware on their routers due to the possible presence of Russian malware. Overall, espionage for competitive advantage motivated 47 percent of attacks.
Healthcare
The healthcare industry has a greater insider threat than an external threat. Seventy-five percent of these hacks are for financial gain, 13 percent are for fun and 12 percent for various reasons. Before Kanye made his iPhone password a superstar, he was the center of another cybersecurity scandal. During his 2016 hospitalization, several hospital workers released Kanye’s confidential documents to the media. The core of the problem boiled down to privilege escalation, which is where an employee gains access to more data than they’re meant to see. However, insider threats are not the only problem plaguing the healthcare industry. Eighty-five percent of malware in the healthcare vertical is ransomware. Ransomware is an easy, low-risk attack with potentially high rewards. For example, WannaCry cost Britain’s NHS about 100 million dollars.
Government Agencies
Privilege misuse and internal error account for one-third of governmental breaches. Privilege escalation also plagues government agencies, especially where these agencies intersect with the healthcare industry. Twenty-four percent affected healthcare organizations, and 15 percent involved accommodation and food service. Fourteen percent of these breaches were public sector entities, like the City of Atlanta’s recent cyberattack.
Discovering Attacks
It takes minutes to carry out an attack but months to discover that it occurred. By the time system comprises are discovered, the damage has already been done. Sixty-eight percent of breaches took months or even longer to detect. For example, Facebook recently notified users about a security hole that took advantage of three separate bugs. The social media giant removed the feature and fixed the issue, but private information of 29 million users had already been revealed. To view more insights and Tripwire’s takeaways from the 2018 DBIR, download the whitepaper here.

About the Author: Katrina Roberts is a technical writer and illustrator. She enjoys cheesy puns, jasmine bubble tea, watching horror movies and crafting illustrations. You can find her on Twitter @punslikepizza and at PunsLikePizza.com. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.

