
Researchers have detected a new ransomware family they're calling "PureLocker" which attackers are using to target enterprises' production servers. Intezer detected a sample of the ransomware masquerading as the Crypto++ C++ cryptography library. In their analysis of the sample, they noticed something unusual when they saw that alleged library contained functions related to music playback. The research team conducted a more detailed analysis after a search on VirusTotal revealed that nothing had been reported about the sample for several weeks. This effort uncovered that the sample lacked a code connection to Crypto++. Even more importantly, the researchers found that sample both reused code from the “more_eggs” backdoor as well as used new code that translated into unusual techniques for a family of crypto-ransomware. Named "PureLocker" for being written in the PureBasic programming language, the ransomware sample verified its file extension, the current year and other information surrounding its execution, for instance. The threat exited without performing its malicious activity if any of those checks failed. As it notes in its research, Intezer feels these techniques effectively differentiated PureLocker from more opportunistic ransomware attacks.
This type of behavior is not common in ransomware, which typically prefer to infect as many victims as possible in the hopes of gaining as much profit as possible. Additionally, being a DLL file designed to be executed in a very specific manner reveals this ransomware is a later-stage component of a multi-stage attack.
The security firm also found that the ransomware was uncharacteristic in its use of anti-evasion techniques. It specifically observed PureLocker using a tactic to evade user-mode hooking of ntdll functions. It also noticed that the threat used the compiled-in purebasic crypto library instead of the Windows Crypto API functions to execute its encryption routine. Upon completion of its encryption activity, the ransomware displayed a ransom note that instructed victims to reach out to an email address hosted through ProtonMail.
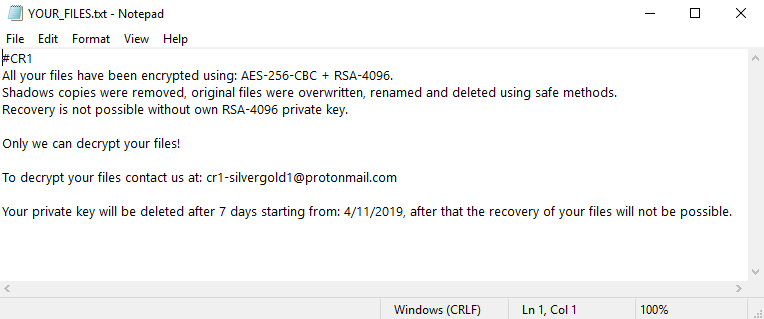
PureLocker's ransom note. (Source: Intezer) PureLocker demonstrates how digital criminals sometimes create unusual ransomware strains to serve their unique purposes. This realization gives organizations even more incentive to prevent a ransomware infection in the first place.

