
A cybercrime gang based in Ukraine is estimated to have made as much as $50 million after tricking Bitcoin investors into handing over the login credentials for their online wallets. Security researchers at Cisco Talos describe how a massive phishing operation has been co-ordinated from Ukraine, after criminals purchased Google Adwords posing as online ads for the legitimate and popular blockchain.info Bitcoin wallet website.
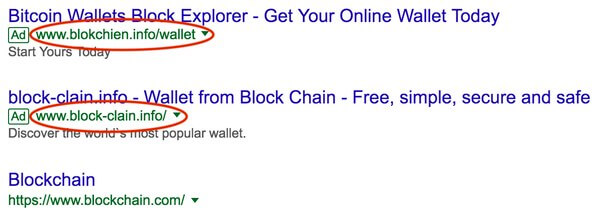
The report explains that by purchasing the ads, the gang - which has been given the name "Coinhoarder" - were able to plant phishing links at the top of Google search results:
When searching for crypto-related keywords such as "blockchain" or "bitcoin wallet," the spoofed links would appear at the top of search results. When clicked, the link would redirect to a "lander" page and serve phishing content in the native language of the geographic region of the victim's IP address. The reach of these poisoned ads can be seen when analyzing DNS query data. In February 2017, Cisco observed spikes in DNS queries for the fake cryptocurrency websites where upwards of 200,000 queries per hour can be seen during the time window the ad was displayed.
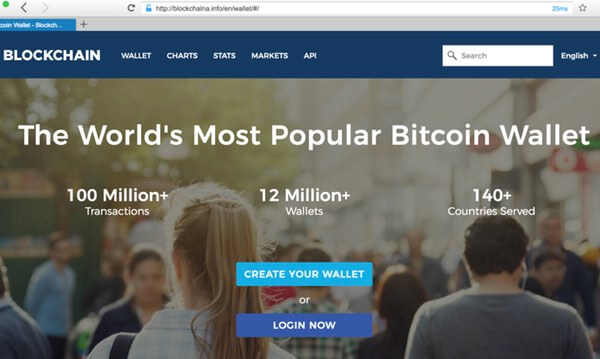
Yes, it's a very simple trick - but that doesn't mean that it isn't also incredibly effective, with researchers estimating that the gang has made approximately $50 million worth of Bitcoin in the past three years. Working with law enforcement agencies in Ukraine, the researchers were able to identify the Bitcoin wallet addresses of the gang and track their activity. In the last four months of 2017 alone, around $10 million was stolen. In one specific run of just 3.5 weeks the Coinhoarder gang made $2 million. Fascinatingly, it appears that the criminals were particularly keen to target individuals in African countries and developing nations where banking facilities may be harder to come by, and - in some cases - local currencies less stable than Bitcoin. And, in an attempt to fool even more unsuspecting Bitcoin investors, the gang was observed creating sites with internationalized domain names (IDNs). Such names can be used in so-called homograph attacks that make it very hard - or virtually impossible - to tell the difference with the naked eye. Of course, as we all know, the price of Bitcoin rose to record heights by the end of 2017 (before dipping more recently). Although you would expect that to be good news for online criminals like the Coinhoarder gang, it has been argued that this may actually have made life harder for them as such huge sums of money become difficult to launder without detection. For now though, despite the Ukrainian authorities successfully shutting down some of the phishing sites, the Coinhoarder group remains at large. There are some steps you can take to reduce the chances of being hit by an attack like this:
- Consider using a hardware wallet rather than an online website to store your cryptocurrency private keys.
- Always take care of the links that you click on - as you cannot be certain whether you might be taken to a phishing site or not.
- Consider running an ad blocker to filter out ads - you'll not only find your web browsing is quicker, but you may also discover that you are no longer exposed to as much online danger.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

