
It's no secret that there are a lot of websites on the internet hosting malicious content whether they be phishing pages, scams or malware itself. Every day we hear of new attacks, there's a common denominator of either a user having clicked on a link to a fraudulent website or a site having played host to code that pulled a malicious payload down from a third-party server. Security products generally do a decent job of watching over the shoulder of your users, blocking access to sites that are known to be malicious and examining content as it is served up to a browser in an attempt to determine if it could be up to no good. But security researchers at Palo Alto Networks propose that there might be an additional simple step your company might like to take to better defend your users against threats: aggressively block all domains less than one month old. As a piece of advice, blocking newly-registered domains (NRDs) certainly makes some sense. One of the major differences between fraudulent and legitimate sites is that sites specifically created with the purpose of committing a cybercrime tend to be much younger. And by their very nature, once they are recognized as malicious, they are often shut down or abandoned soon after their birth. Most of the sites that your users have a legitimate reason to visit will be established sites that have existed for longer than one month. There should be relatively few instances where their browser has a legitimate business reason to reach a website hosted on a domain that has only just been registered. As the researchers describe, NRDs are often used for a variety of murky activities including but not limited to malware distribution, typosquatting, phishing, adware, spam and as part of command and control infrastructure.
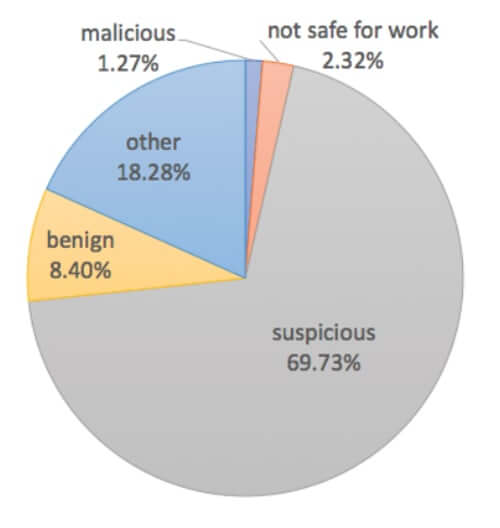
Our analysis shows that more than 70% of NRDs are “malicious” or “suspicious” or “not safe for work.” This ratio is almost 10 times higher than the ratio observed in Alexa’s top 10,000 domains. Also, most NRDs used for malicious purposes are very short-lived. They can be alive only for a few hours or a couple of days, sometimes even before any security vendor can detect it. This is why blocking NRDs is a necessary, preventive security measure for enterprises.
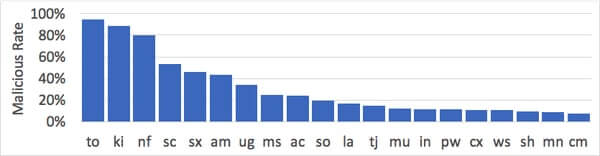
For the purposes of its research, Palo Alto Networks' team defined a newly-registered domain as one that had been registered or changed in the previous 32 days. Of course, there are implications to consider if your business decides to aggressively block newly-registered domains. Your users might, for instance, find themselves unable to access sites set up to promote a brand new product or event or web pages on which a company has recently rebranded itself. There will be times when it's inconvenient, but to my mind, the very real risks posed by NRDs probably outweigh the nuisance of not being able to reach a site easily. The researchers suggest that if access to NRDs is going to be allowed inside your organisation, "alerts should be set up for additional visibility." If, however, you want to heighten security, then you may wish to completely block certain top level domains often associated with cybercriminal activity. According to the researchers, TLDs such as .to, .kl and .nf are much more likely to host malicious content.
Your organisation must decide whether it will be happy to tolerate a potentially higher level of false alarms through blocking NRDs and entire TLDs. That being said, there seems to be little doubt that it will reduce your firm's potential exposure to attack.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

