
Japanese game developer Capcom has revealed that it suffered a security breach earlier this week which saw malicious hackers access its internal systems. The maker of such well-known video games as "Resident Evil" and "Street Fighter" disclosed in a short press release that in the early hours of Monday some of its networks "experienced issues" that affected access to email and file servers. In response, the company has shut down some of its systems. However, in what must be a big relief to fans of Capcom video games, the attack is said not to have affected players' online access to the firm's video games and websites. But might whoever managed to hack their way into Capcom's network have accessed any sensitive data, such as customer details? At the moment the company's official statement says that "at present there is no indication that any customer information was breached." Of course, as security commentators love to point out, an absence of evidence is not an evidence of absence. If you have ever shared sensitive information with Capcom you might be wise to assume that those details might now be in the hands of cybercriminals, and - as ever - be cautious about unsolicited emails and other attacks that often occur following a data breach. And even if no customer information has been stolen from Capcom's internal servers and email accounts, there might have been other sensitive data stolen - such as intellectual property from the video game developer, or details of the firm's plans for future video game releases. There is some reason to be concerned that a data breach might have happened. Just last month, ZDNet reported that two other video game companies, Ubisoft and Crytek, appeared to have suffered a security breach that saw stolen files posted on the dark web. Those breaches appear to have been the work of a ransomware gang calling itself Egregor, whose malware is said to be closely related to another family of ransomware known as Sekhmet. Researchers at Malwarebytes have warned that cybercriminals who were previously making use of the Maze ransomware (which recently retired from active service) have shifted towards Egregor. For now, however, it is unclear what precisely may have happened at Ubisoft and Crytek, and whether the firms' data was encrypted by the ransomware like Egregor or just stolen.
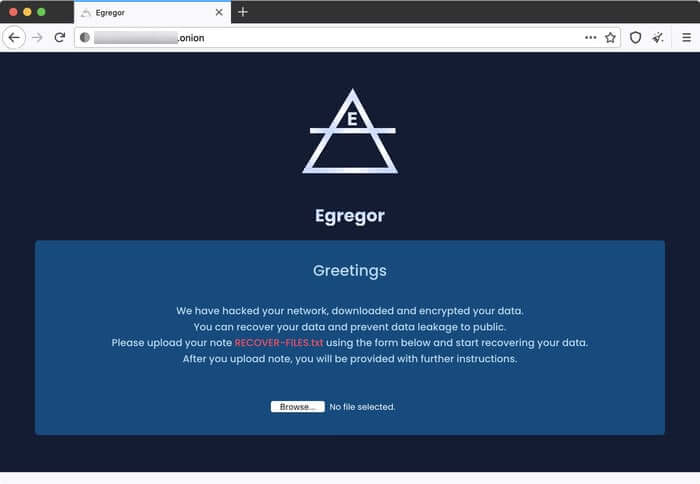
If Capcom has been hit by the Egregor ransomware, then chances are that they will have been directed to a darknet website operated by the hackers, demanding a cryptocurrency payment in exchange for a decryption key and the promise that stolen data will not be leaked publicly. In its press release, Capcom expresses "its deepest regret for any inconvenience" that may have been caused by the hack and its aftermath. The firm says that it has informed the computer crime authorities about the incident, and is working to restore its systems. Presently it is unclear how long it will take Capcom to return to its normal operations.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

