
RFID is one of those ubiquitous technologies showing up everywhere from contactless payment cards to the neighborhood swimming pool. Some of these technologies offer appropriate security controls but many applications still use legacy technology that is easily subverted by an attacker. Back in 2013, data from HID Global indicated that 70-80% of physical access control deployments in the US were using legacy technology. A variety of tools are now available making it possible for researchers and penetration testers to explore and compromise many systems. Meanwhile advancements in 3D printing have created new opportunities for physical penetration testers to use these tools in practical attacks. These two factors inspired the research behind my upcoming DEF CON 23 talk, “How To Train Your RFID Hacking Tools”. The general objective of this presentation is to help make it easier for others to not only use existing tools but also to better utilize them by extending firmware, combining them with other devices, and concealing them for practical attack.
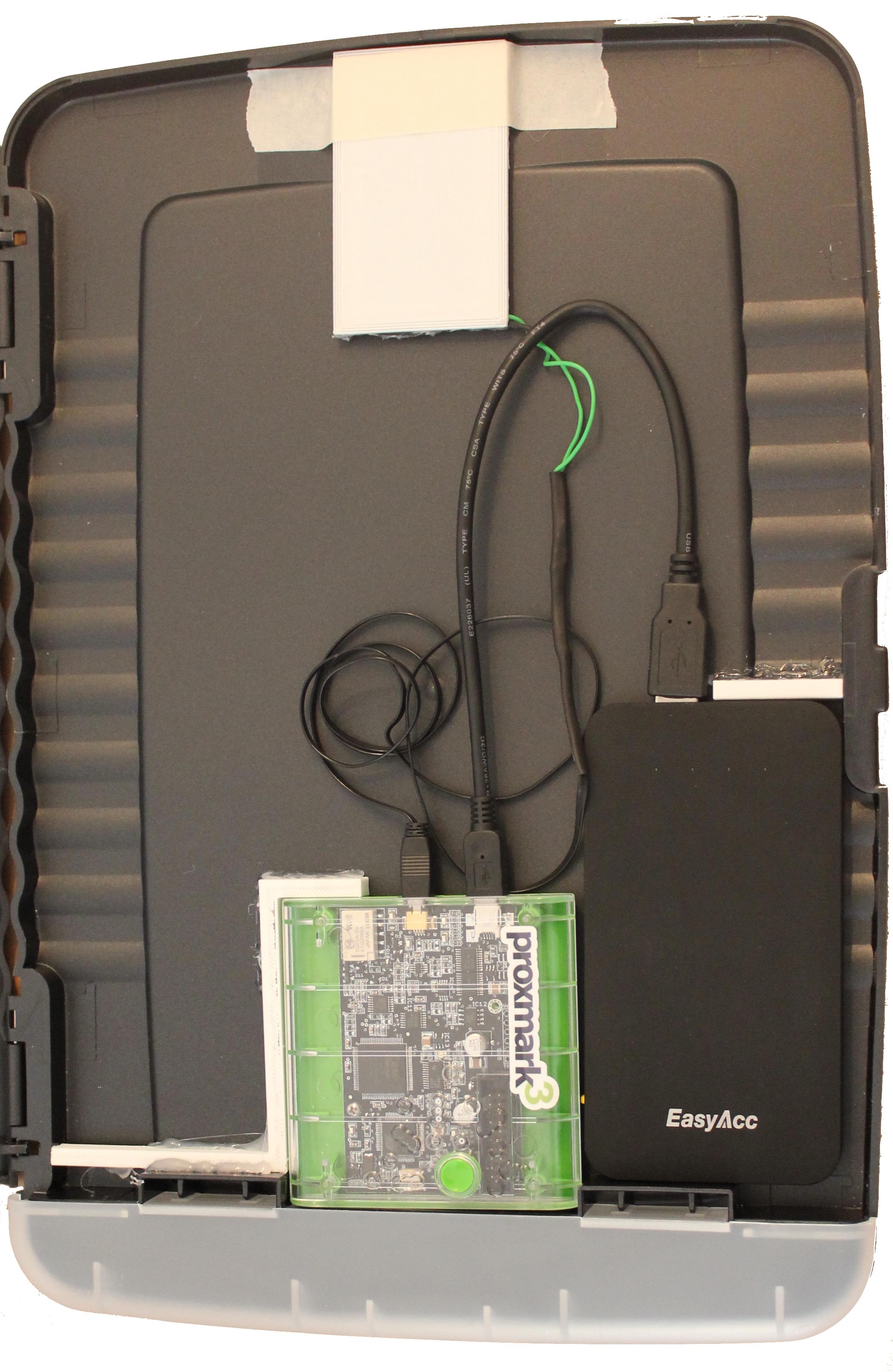
The first challenge when preparing practical RFID attacks is hiding the gear. Getting the antenna coil close enough to read a badge or simulate a tag without raising any alarms can be tricky. Constructing a coil using a 3D printed form allows it to be more easily disguised within another object. As such the first task in this project was a crash course in electromagnetic theory so that I could prepare a 3D model suitable for forming an antenna coil. This turned out to be relatively easy and effective leading to an antenna that was actually cheaper and more effective than an off-the-shelf antenna. (The DIY antenna yielded stronger signals than a commercial antenna that cost about five times as much.) The resulting antenna design can then be integrated into or camouflaged by other objects like fake readers or badges, storage clipboards, or phone cases. On Friday I will be showing some of the tools I made as well as discussing how to obtain and make use of models as well as the benefits of combining some tools with secondary embedded computers like RaspberryPi or USB Armory. Once the hacking tool is concealed appropriately for the situation, it may be necessary to compliment it with purpose built firmware to perform mission specific functions. While open source tools make it possible to create custom patches, it is not always easy to know where to begin when diving into unfamiliar code. This is why I felt it important to create tutorial like examples of firmware enhancements. Since it is by far the most reliable open source tool I had access to, I decided to target my firmware changes at the Proxmark. The presentation will demonstrate how to use some of the recently added advanced features as well as how to create new commands and stand-alone modes for the Proxmark. (The code changes are discussed at length in a soon to be released whitepaper.) After some thought I decided to add commands for working with an unsupported tag format and add NFC capability to stand-alone mode. These changes make good educational tools and useful features. Although Proxmark has support for a wide range of tag formats I noticed that there was no support for working with the AWID26. While perhaps not as prevalent as something like the HID ProxCard II, AWID tags are commonly used to enforce access controls for parking garages, elevators, pools, offices and more. These cards are particularly interesting in that they can be simulated or even duplicated using only information printed on the tag.

Code for this new stand-alone mode as well as the new AWID command context is now available in GitHub. The presentation will discuss at a high level what was needed to make these changes and how to use the new features. The code changes are also discussed in much greater detail within the upcoming whitepaper. Whether you have extensive knowledge about RFID systems or are just curious about the technology, I hope you will join me at DEF CON track 1 this Friday at 6:30PM. Please also don’t forget to check out the first ever DEF CON IoT Village where I will be presenting research on vulnerabilities in ‘Smart Home Hubs’ on Sunday at 10:00AM. Title image courtesy of ShutterStock
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

