
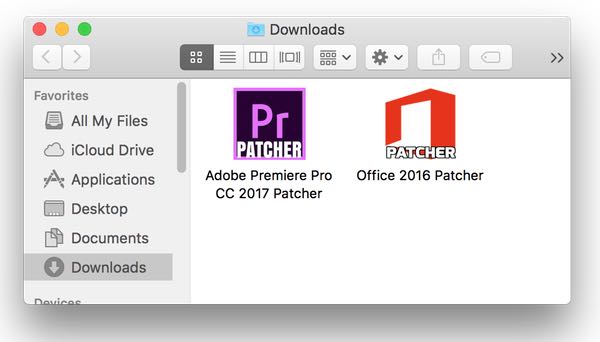
In their ever-increasing aggressiveness to wring even more money out of victims, it's perhaps no surprise to see some online extortionists creating ransomware targeted against affluent Mac users. The latest example of Mac ransomware, OSX/Filecoder.E, has been discovered by malware analysts at ESET after it was distributed via BitTorrent distribution sites as cracks to pirate software. Examples found by the researchers included patchers for Adobe Premier Pro and Microsoft Office for Mac.
When the malicious apps, coded in Swift, are executed a somewhat peculiar transparent dialog is displayed inviting the user to click a "Start" button to (allegedly) begin the process of cracking the commercial software.

Of course, the malware is not doing what it claims at all. Instead, it is encrypting files on the user's hard drive and mounted external and network drives using, for its key, a random 25-character string. At the same time, the Filecoder ransomware is dropping a README!.txt file in the victims' directories, with instructions on how a 0.25 Bitcoin payment (approximately US $280) should be made for the safe recovery of their data.
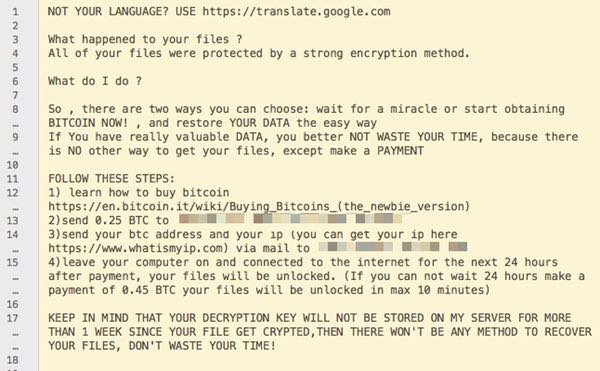
The message advises that users should leave their computer connected to the internet for 24 hours to ensure that decryption takes place after the ransom has been paid. For those victims who are feeling impatient they can choose a ten minute fast-track option, claims the message, by paying 0.45 BTC (approximately US $510). ESET's research team, however, believes that there is no point in paying the ransom as the files can not be decrypted:
There is one big problem with this ransomware: it doesn't have any code to communicate with any C&C server. This means that there is no way the key that was used to encrypt the files can be sent to the malware operators. This also means that there is no way for them to provide a way to decrypt a victim’s files. Paying the ransom in this case will not bring you back your files. That's one of the reasons we advise that victims never pay the ransom when hit by ransomware.
All of which means that I hope you took sensible precautions to backup your data before having your Mac hit by this ransomware. If ransomware isn't enough of a reason to convince you to make regular secure backups (and it should be) then consider the danger of hard drives failing, the ease with which you might accidentally erase important files, or the risk that your computer is stolen or lost. Oh, and it should go without saying, that if you're downloading cracks to pirate commercial software don't be surprised if you get stung by an online criminal using that disguise as a means to spread their malware. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.

