
Endpoints are more important than ever in today's connected world. As business increases, most organizations find it necessary to connect a variety of new devices to their networks to keep up with the demands of competing in a global economy. Each of these endpoint nodes may be devices with which employees interact on an ongoing basis, but they might not. They could be point-of-sale (PoS) terminals, financial trading processes, or other systems that require little user interaction but which are nevertheless critical to the success of the business. Regardless of the extent to which users handle them, all network endpoints need to be protected against threats. Attackers would love nothing more than to steal enterprises' intellectual property, payment card details, and/or personal information, and in most cases, they could find a way to exfiltrate those types of data if they successfully located where they were stored. Those instances of data theft simply require that the attackers gain access to the corporate network first. To fulfill that crucial part of their scheme, criminals would likely look for a vulnerable laptop, server, or other endpoint device installed the network that they could abuse for access. The risk of data exfiltration is just one of the threats confronting organizations today. That is why Tripwire is so committed to spreading awareness about the changing face of endpoint security. Tripwire recently hosted a webinar with Eric Ogren, senior security analyst at 451 Group and Gajraj Singh, VP of Product Marketing at Tripwire on the evolution of how security teams can protect their organizations' endpoints. The duo explained that we are seeing a shift in security in today's organizations. On the one hand, there is an increased demand for security to align with businesses' needs. This trend is in part due to the rise of compliance – a model of continuous security which fundamentally relates to how a business runs. Each critical business process depends on the endpoint network devices that drive it forward. Today's security models, therefore, need to take those processes into consideration in order to understand how an endpoint should be behaving and what needs protecting. Only then can security enable business agility, including growth, competitiveness, ops efficiency and customer experience.
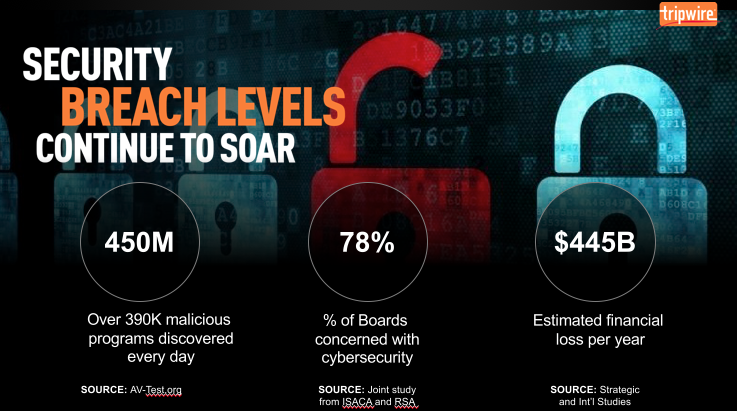
At the same time, Ogren and Singh note that security teams and boards are hypersensitive to the increasing costs of a data breach. To avoid becoming the next victim, organizations need to be able to detect the early stages of an intrusion before significant financial and reputational costs are incurred. Enterprises can hope to do this and achieve cyber resiliency by adopting a proactive detection and response approach, one which balances a contextual understanding of how each endpoint is supposed to behave with a thorough review of the core issues following each potential incident. Prevention will never completely go away. But in the presenters' minds, the future of endpoint security rests with organizations adopting a diagnostic and fix service model that proactively looks for anomalous endpoint behavior. To learn more about what steps go into this model and how you can leverage its insights to protect your endpoints, view Tripwire's webcast on endpoint security here. You can also click here to obtain your free copy of Endpoint Detection and Response For Dummies Title image courtesy of ShutterStock

