
Internet users are doomed. I don't mean you or me; the fact that we're reading this article on Tripwire's The State of Security blog means we at least have a passing interest in protecting ourselves online. No, I mean those folks who, like us, use the internet but don't take the steps necessary to put in place the most rudimentary defenses to prevent themselves from being hacked. Sadly, I suspect I'm talking about the vast majority of internet users. Most people don't use password managers to generate hard-to-crack unique passwords, preferring to rely on their puny brains instead and inevitably reusing login credentials between multiple services. Most people don't run a VPN, leaving themselves exposed to having their data grabbed when they use a public Wi-Fi hotspot. And, as a presentation by Google software engineer Grzegorz Milka this week revealed, hardly anyone is is using two-factor authentication (2FA). A well-implemented two-factor authentication system ensures that it's no longer the case that the only thing stopping a hacker from being able to access your online account is whether they can determine your username (often just your email address) and password. Even if a hacker has managed to determine your password (perhaps because you chose a poor one or perhaps because you made the mistake of using the same password on multiple websites), then the two-factor authentication check will request that they enter a one-time six-digit passcode generated by a tag on your keyring or an authentication app on your smartphone.
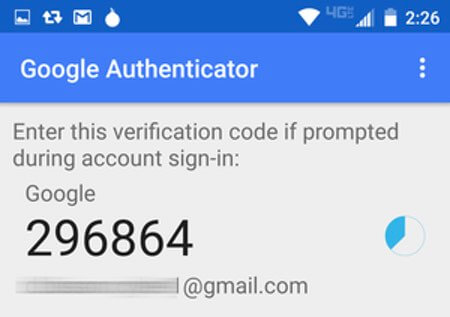
No one-time passcode? No entry. Clearly, it's a higher level of security, and one which is enough to encourage a typical hacker to look for someone else's account to break into rather than yours.
And yet, as reported by Iain Thomson of The Register, Grzegorz Milka revealed at Usenix's Enigma 2018 security conference in California that less than one in 10 Google users have enabled two-step authentication to lock down their accounts. That's a depressing statistic for a security feature that Google introduced nearly seven years ago and that most security professionals would describe as a "must-have" for anyone keen to keep unauthorised parties out of their accounts. Don't delay. If you haven't already done so, please enable Google 2-step verification. To help the over 90% of active Gmail users who have still not recognised the benefits of this additional security layer, Google has a simple step-by-step process that will hold your hand as you boost your defences.
One step beyond
So, what if you have already protected your Gmail with two-step authentication but still want to go even further to keep hackers out of your account? Last year, Google unveiled an Advanced Protection feature for those users who felt that they might be especially at risk such as journalists wishing to protect their sources or individuals in abusive relationships. Advanced Protection goes beyond Google's existing authentication services, disabling the sending of authentication codes via SMS or usage of an authentication app and instead demanding that a physical security key is inserted into your computer's USB port instead.
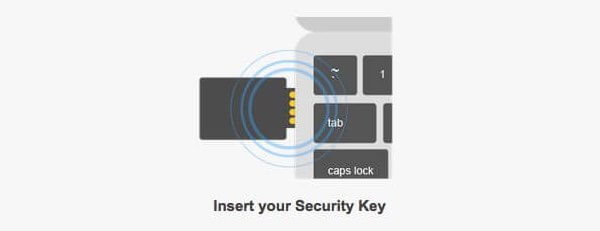
Advanced Protection certainly isn't for everybody, and my suspicion is that many users would find it too restrictive for use on their everyday accounts. For instance, it prevents you from using third-party apps to access your Gmail or data held on Google Drive. But it's good to see Google offering these features for those people who do need heightened security. Now if only we could see some more people recognize and adopt even the most basic form of two-step verification. We would make the work of malicious hackers so much more difficult. Do your bit to help your friends, family, and colleagues avoid having their accounts hacked. Explain to them the benefits of multi-factor authentication and help them to enable it for as many online services (not just Gmail) as possible. Because left to their own devices, many internet users surely are doomed. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.

