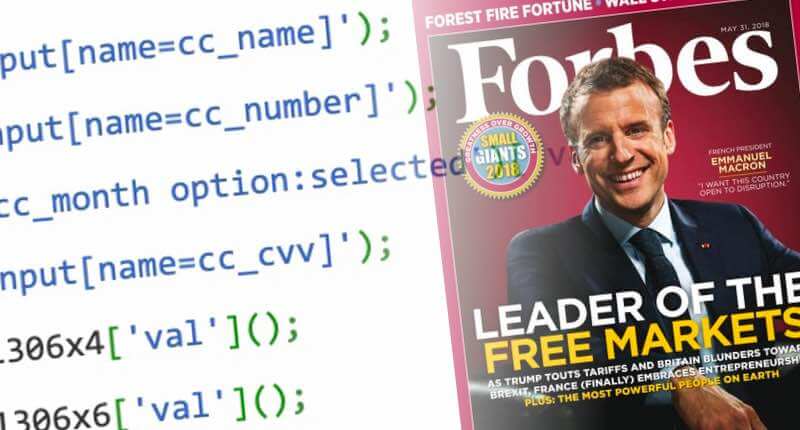
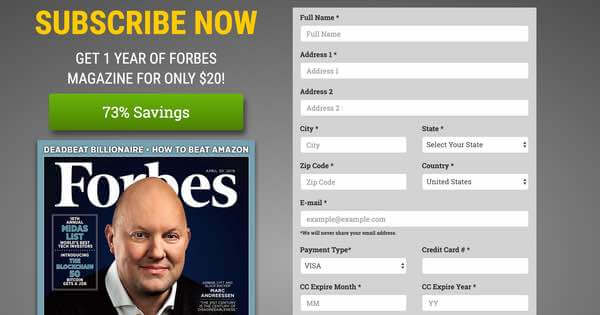
The notorious Magecart malware, that blights online stores by stealing payment card details from unsuspecting shoppers at checkout, has claimed another high profile victim. Security researcher Troy Mursch raised the alarm on Twitter that the Forbes magazine subscription website had been compromised with malicious code that was siphoning off sensitive credit card information as users attempted to sign-up for the paper edition. Unsuspecting subscribers would think they were entering their details to receive regular copies of the magazine, but what they didn't know was that payment card numbers, expiry dates, three digit CVV/CVC security number were being grabbed by hackers, alongside their names, addresses, and phone numbers. It appears that the attackers had planted their malicious code on a third-party website with the name fontsawesome.gq - presumably with the thought that if anyone took the trouble to examine the source code of Forbes magazine's website they might conclude that it was related to the legitimate FontAwesome service, used by many websites to provide fancy icons.
Quite how hackers managed to plant the call to the obfuscated malicious JavaScript onto Forbes's subscription page is currently a mystery, but questions will undoubtedly be asked as to whether the web server's security was properly hardened and kept up-to-date. Another theory is that Forbes may have been the victim of a supply-chain attack. Forbes is a customer of Picreel, a website analytics service, and this weekend it was discovered that Picreel had suffered a security breach that resulted in code used by thousands of websites being compromised. Troy Mursch (who posts as @Bad_Packets on Twitter) made numerous attempts to alert Forbes of the problem on its subscription site. A spokesperson for the company told The Register that it was not aware of any credit card information being stolen by the criminals, although an investigation was taking place. Nonetheless, it seems sensible for anyone who has recently been to the site to check their financial statements for unusual activity. Fortunately, the fontawesome.gq domain hosting the malicious code was taken down quickly, effectively neutralising the attack (for now at least). Forbes is just the latest in a long line of companies to have been hit by a Magecart attack. Past victims have included British Airways, Feedify, Umbro, Vision Direct and Newegg. Unfortunately for Forbes, they are no strangers to being targeted by online criminals. In the past the magazine's website has been compromised by the Syrian Electronic Army hacking group (who broke into the magazine's WordPress admin console, and posted an article), leaked the details of over one million readers, and served up malicious ads that redirected users to pages hosting the Neutrino and Angler exploit kits.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.

