
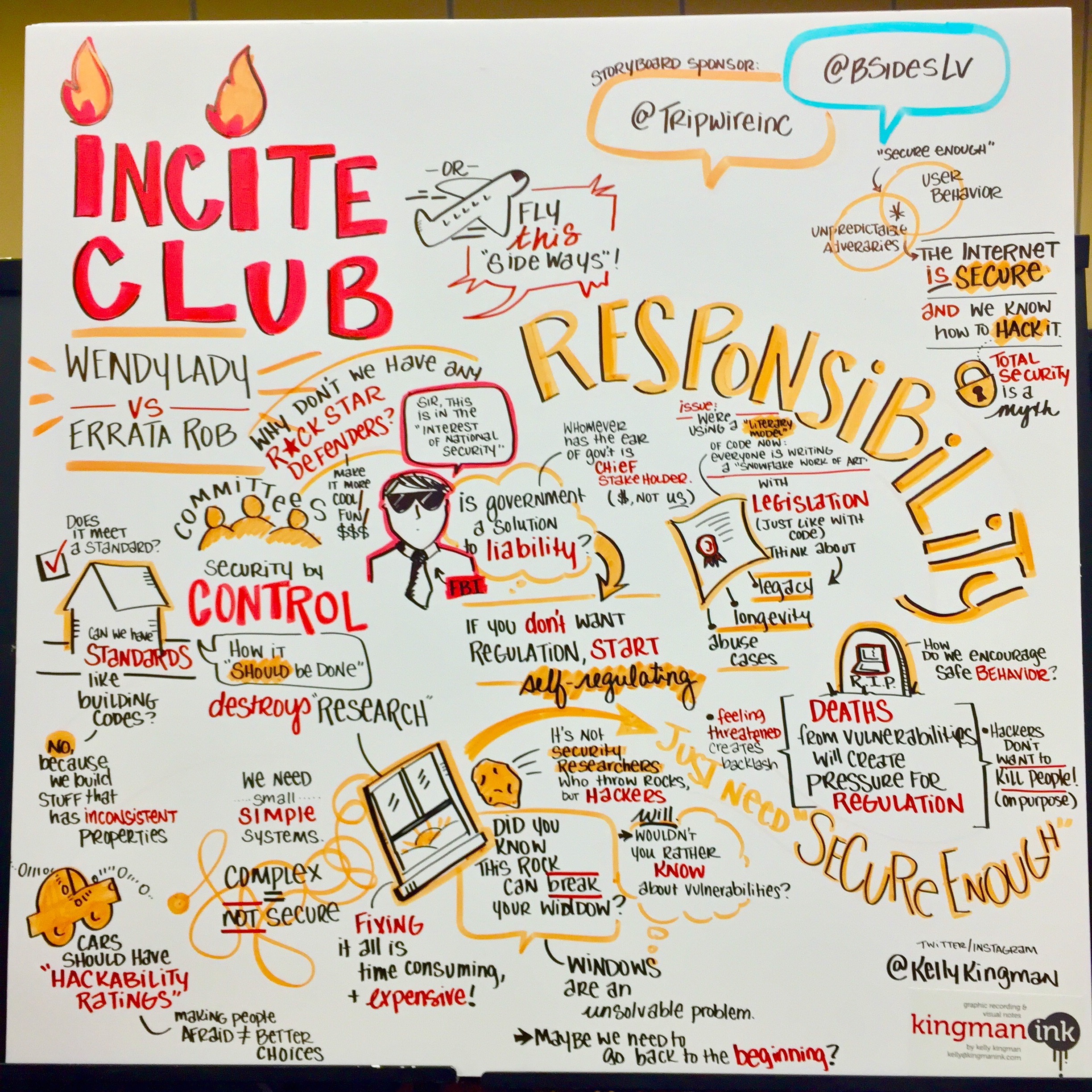
This year’s BSides in sunny Las Vegas, Nevada, is off to an amazing start, with an overwhelming crowd and a great lineup of presentations from some of the industry’s brightest – and most inspiring – professionals. In the biggest BSides LV event yet, hundreds of attendees gathered at the Tuscany bright and early – eagerly waiting to hear from experts in all things “cyber.” Below is a quick-read recap of some of the sessions I had the pleasure of attending today. Also, a special thanks to Kelly Kingman, our graphic artist, for creating these very cool visualizations of the talks in real-time. Up first was Wendy Nather, now Research Director at the Retail Cyber Intelligence Sharing Center, and Rob Graham, CEO of Errata Security. In their (Un)Keynote, the two argued valid points from both sides of the spectrum on how to get the world to take security seriously, including the growing concern of critical infrastructure protection, as well as the recent debate on stunt hacking.
Speaking Metrics to Executives
Speaker: Michael St. Vincent (@JustOnePing) Michael gave an interesting presentation on the common tripping stone that is transforming the typical “geek numbers” into metrics that executives will understand and derive meaning from. Using good and bad examples, Michael stressed the importance of bringing forward the business issues that these metrics represent. Executives need quick value, so when you are presenting data – typically in the form of graphs – make sure to ask yourself these questions: Is this information actionable? Does it create a sense of urgency? Is it easy to understand? Is it trend-focused? And, is it an easy-to-see story?
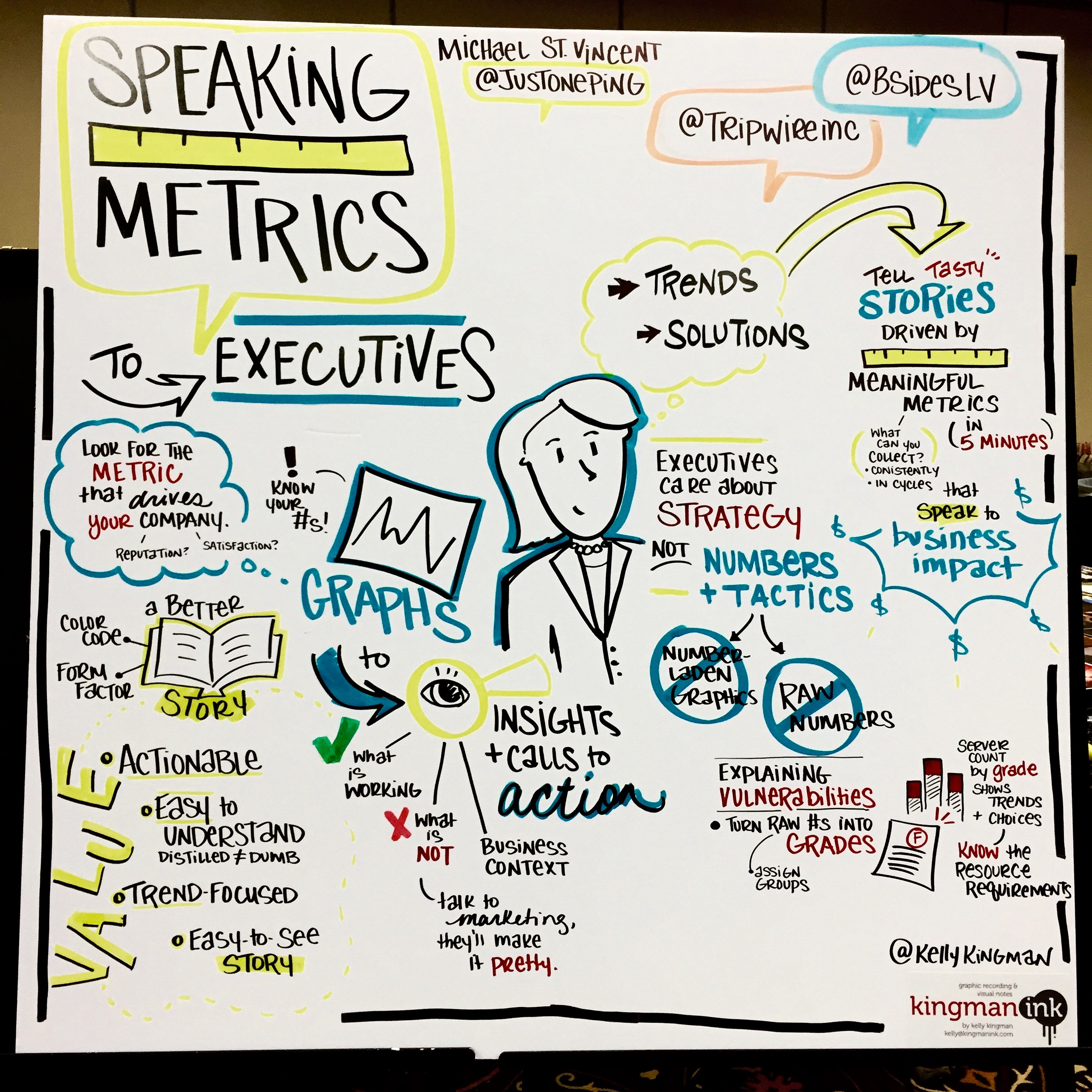
Michael reminded attendees that when the opportunity presents itself, we may only have a few minutes to get our point across to executives. He suggested reaching out to marketing or other colleagues on the business line to make sure the metrics you are presenting make sense and is also valuable to them.
Hack the Future
Speaker: Keren Elazari (@k3r3n3) In this inspiring and lively presentation, Keren gave us an eye-opening overview of what cybersecurity has become. For the past 20 years, we’ve been all about protecting bits and data, said Keren. However, a number of recent high-profile breaches should teach us that these leaks mean that secrets are eventually going to get out there (the AshleyMadison and Sony Pictures hack, to name a few). People are afraid of hackers because they shatter their illusions of having privacy. Meanwhile, we are using social networking sites, such as Facebook, WhatsApp and Instagram, free of charge because we pay with our choices and our information we are willingly handing over – the places we go and the things we like are valuable information.
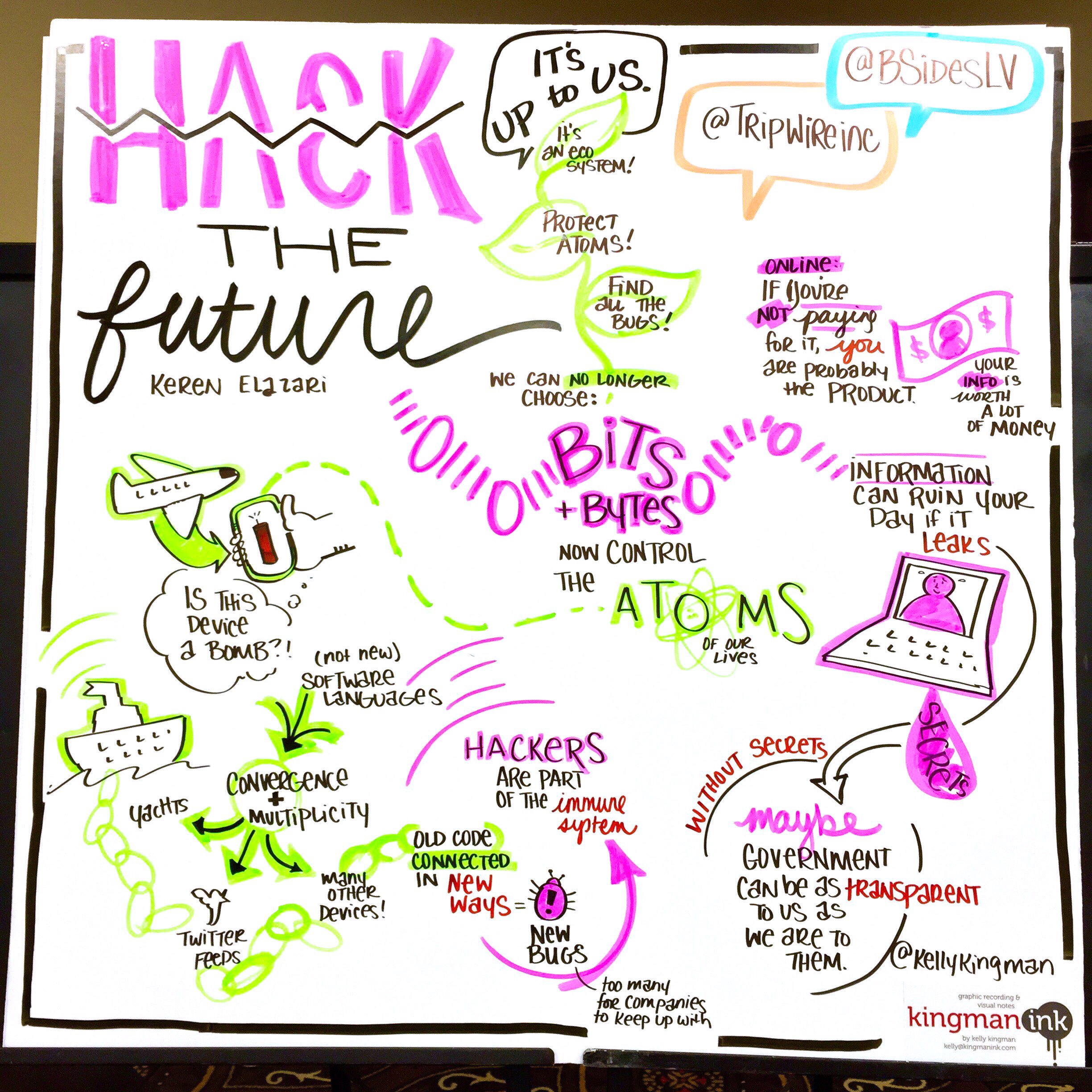
“The future of cybersecurity is not just about privacy or keeping things secret,” said Keren. If there are no more secrets, and our information is worth a lot of money, the power of releasing information can change the world (think Edward Snowden).
“Maybe in this reality, with the help of hackers, the government and corporations will be as transparent and exposed to us, as we are to them.”
Keren concluded stating that there is no way everything will be secure, but this is exactly why the world needs hackers – they are part of the Internet’s immune system. It’s about finding the problems and sparking the solution, she said. Keren gave a Ted talk on this subject, which you can view here.
The Journey to ICS
Speaker: Larry Vandenaweele (@lvandenaweele) Attacks on critical infrastructure have been a growing concern as of late, especially with the catastrophic consequences that one may potentially have. This talk gave an overview of industrial control system security, including types of attacks and common weaknesses. With over 14,000 interconnected devices, Larry pointed out the attack landscape is vast and industrial systems continue to experience several types of attacks, such as DoS, leveraging insecure protocols, hardcoded credentials, man-in-the-middle, rogue modems and of course, physical attacks.
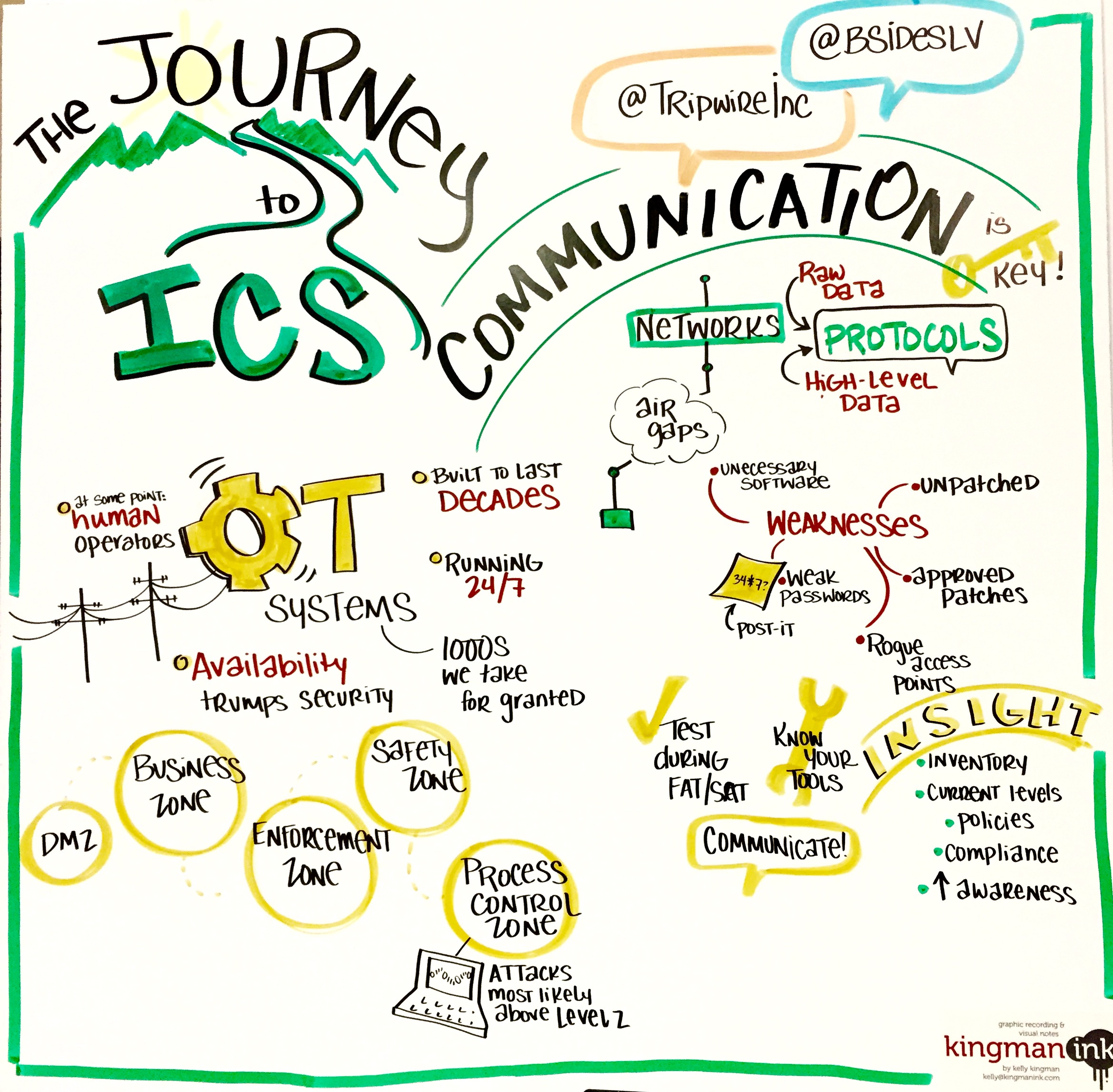
Using real-world examples, Larry mentioned many of the most common weaknesses seen in ICS – from poor authentication and using post-its for passwords, to ineffective physical security like leaving doors or windows open, to rogue access points and unnecessary software. Lastly, Larry recommends we can protect ourselves by first, building a team to work together with, gaining insight on the current situation and creating an inventory. This is not an easy process, and it may take several small steps to make progress. With management’s involvement, Larry stressed that communication is key.
What Would Fix Passwords? Some Weekly Passwords Audits
Speaker: Rick Redman (@CrackMeIfYouCan) In this presentation, Rick Redman of KoreLogic demonstrated how one particular enterprise was able to dramatically minimize its risk posed by password cracking attacks – from 85% cracked, down to only 50% cracked – after implementing weekly password auditing.
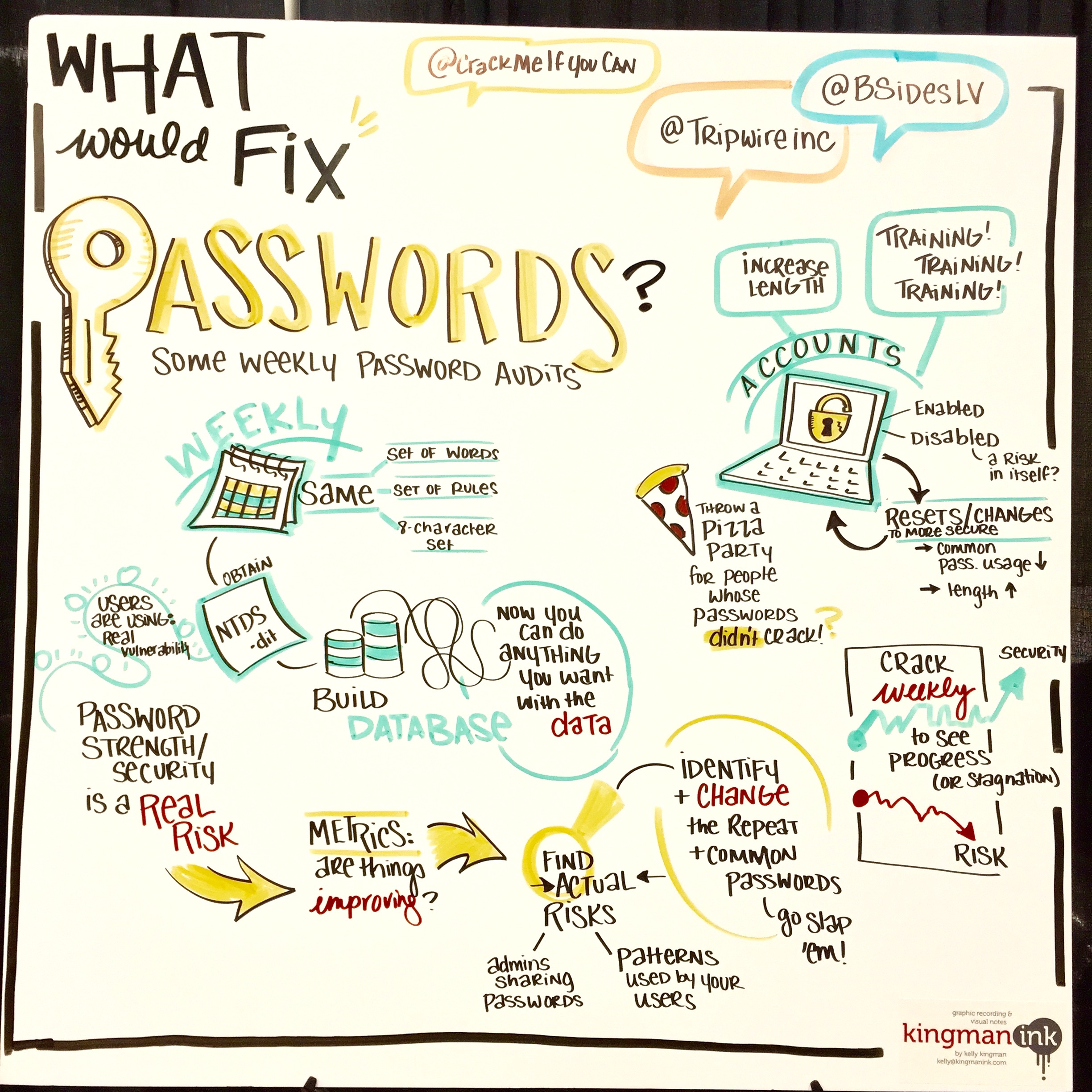
Rick outlined many of the benefits of this practice, such as finding admins who share passwords with non-admin users, finding default help desk passwords and identifying patterns used by user. It also helps find which administrators are not rotating passwords and the account management behavior of admins. Using the example of a real enterprise, Rick showed several graphs illustrating patterns and trends on employee account passwords. They identified that the majority of users were using 8-character passwords, while the use of 9-character passwords was declining and 10-, 11- and 12-character passwords remained steady. On a weekly basis, they disabled the most common passwords, which in some instances, amounted to more than 100 accounts using the same password. They also chose to change the passwords of disabled accounts, instead of getting rid of them to avoid "breaking things." Rick said the company saw significant progress with this strategy. His recommendations on diminishing risk included increasing password character length to 9, incentivizing employees and lots of training.
State of Automotive Cyber Safety
Speaker: Josh Corman (@joshcorman) For the last session of the day, I chose to attend a talk by Josh Corman on the automotive space and its recent engagements with the security industry. Josh opened with this clear statement: “All systems fail.” It’s a given that there’s a certain defect rate for every thousand lines of code, and today, our automobiles have become computers on wheels.
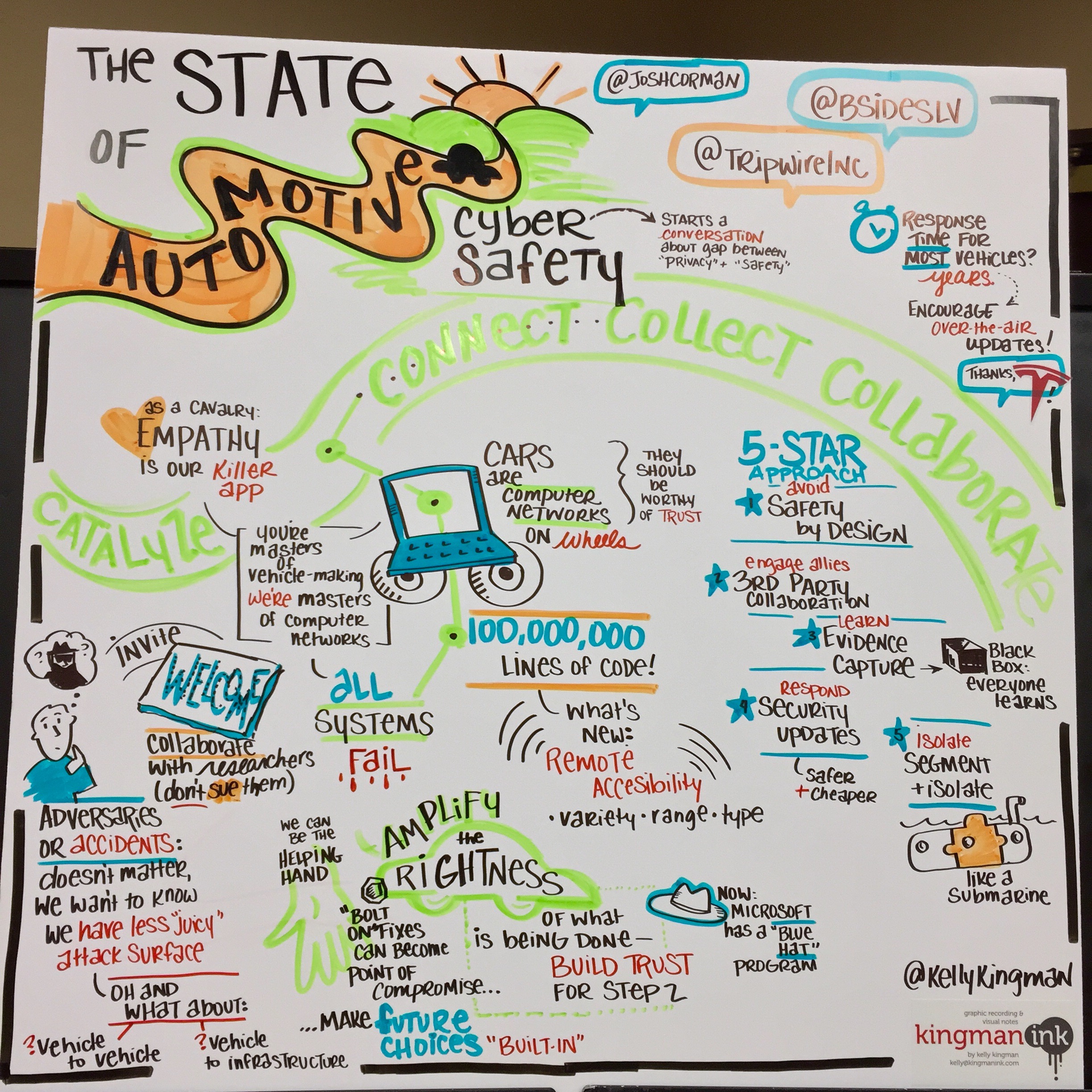
Our cars now have numerous hackable features, such as anti-theft systems, Bluetooth, radio data systems, in-car Wi-Fi and smart keys. The Internet is hard-wired onto these vehicles, and the problem is that our society is adopting connected technology faster than we are able to secure it. Josh outlined a “5-star approach” to addressing the automotive cyber systems:
- Safety by Design
- Third-party Collaboration
- Evidence Capture
- Security Updated
- Segmentation and Isolation
In plain speak, this framework translates to:
- Avoid failure
- Engage allies to avoid failure
- Learn from failure
- Respond to failure
- Isolate failure
Josh added that there is a difference between bolt-on vs. built-in security, and there are many prone, vulnerable and unpatchable vehicles; while some may not be able to be fixed completely, the key is to help them improve.

