A few years ago, I worked alongside some oil commodity traders. Environmental concerns aside, I never realized how many parts were required to get the oil out of the ground, not to mention everything else that finally resulted in the production of refined products that surround our lives. As a cybersecurity professional, I was more interested in how all the pipelines were intertwined and, of course, protected.

When the commodity traders asked me to install the America Online Instant Messenger application onto their desktops, I hesitated. For what legitimate purpose could an office use such an application? They informed me that a person standing on an oil rig in the ocean would use AOL-IM to communicate operational advisories to people working on the mainland, including the commodity traders. This instant knowledge enabled them to execute trades, predict the futures markets, and facilitate a group of other commodity trading endeavors. However, I was thunderstruck at this lack of security forethought by an entire industry!
I saw some of the communications, which were quite elegant in their simplicity, and quite scary from a security perspective. To paraphrase:
Oil Rig Operator: Valve 725 open at line 60.
Group recipients: Understood. Will notify downstream operators.
Can you ponder some of the varied ways that a malicious actor could wreak havoc with such information?
Introducing the Pipeline Cybersecurity Initiative
Fortunately, in recent years, the Department of Homeland Security has developed a plan to increase security of this area of critical infrastructure. This plan was then assigned to the Cybersecurity & Infrastructure Security Agency (CISA) to carry out its implementation. It is called the Pipeline Cybersecurity Initiative (PCI), and while I wish they came up with a better name as to avoid confusion with the PCI-DSS Standard, I will not quibble.
It turns out that there are more than 2.7 million miles of pipelines responsible for transporting oil, natural gas, and other commodities across the globe. Think of that distance for a moment. Then, in light of the unsecured communication technique used by the industry, think of what it would take to disrupt that as well as the cascading consequences that such a disruption could produce. According to the PCI overview, “a compromise of pipeline systems could result in explosions, equipment destruction, unanticipated shutdowns or sabotage, theft of intellectual property, and downstream impacts to National Critical Functions (NCF).”
When hearing about pipeline security and anything related to critical infrastructure, most people immediately think of securing Industrial Control Systems (ICS). While the PCI guidance addresses that, it takes a broader approach, as well. Topics such as evaluation of the overall security posture of a system and engaging with partners and stakeholders are considered.
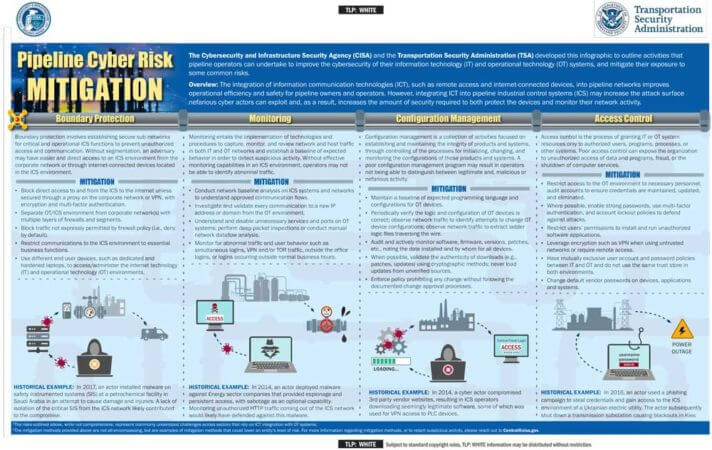
CISA also offers a handy Pipeline Cyber Risk Mitigation Infographic, a resource which outlines activities that pipeline owners and operators can undertake to improve their ability to prepare for, respond to, and mitigate against malicious cyber threats. The infographic also includes historical examples to add context to some of the exploits that have occurred through a lack of the various security labels.
Many of the recommendations in the PCI guidance are similar to those of other familiar security strategies, such as boundary protection, monitoring, configuration management, and access control, so one may wonder why the oil industry doesn’t just follow all the other available advice. While I am sure that they do that, there is just something different about advice when it is more directly focused to a particular industry. Similar to any advice, guidance always has more authenticity when addressed to a specific audience.
Other industries could also benefit by examining the PCI information. Since collaboration is key to the success of any cybersecurity plan, cross-industry awareness is also important for a more complete approach to these critical networks.
I am optimistic that the commodity traders no longer rely on unsecured messenger systems. Now, the entire pipeline industry can have a place to turn for more guidance.