
I am pleased to present Part 2 of my recent interview with Graham Cluley, an award-winning security blogger on grahamcluley.com DB: How do you feel the security industry has changed since you first started in the 1990s? GC: The industry has grown up enormously. Originally, it was just a cottage industry made up of little – often one-person – companies that operated out of spare bedrooms and produced small utilities for their users. Some of these became successful and have helped build information security into the global industry that it is today. However, some of those success stories might have been an accident of geography. After all, what John McAfee produced way back when was certainly no better than, say, Frisk’s F-PROT, but as Frisk was based in Iceland and did not capture a large part of the American market, it’s McAfee that’s the household name. That’s just the luck of the draw sometimes. The security industry’s growth has seen a parallel increase in the number of computer threats. When I first started out, about 200 new computer viruses were discovered every month (we thought that was a lot back then). Most of our customers received updates via the post on 5¼ inch floppy disks every three months. For those who were really paranoid, they could connect their modem to an antivirus company’s bulletin board and download an update about once a month. Even in the worst case of a virus outbreak, we might fax our users and ask them to type in the update at the other end. But these types of events were rare. Most people didn’t need updates more frequently because malware was so slow to spread. We didn’t have these sprawling networks back then, and because most people did not have email, viruses didn’t bother being email-aware. They mainly spread via floppy disk, so our job was to try to mitigate that threat.
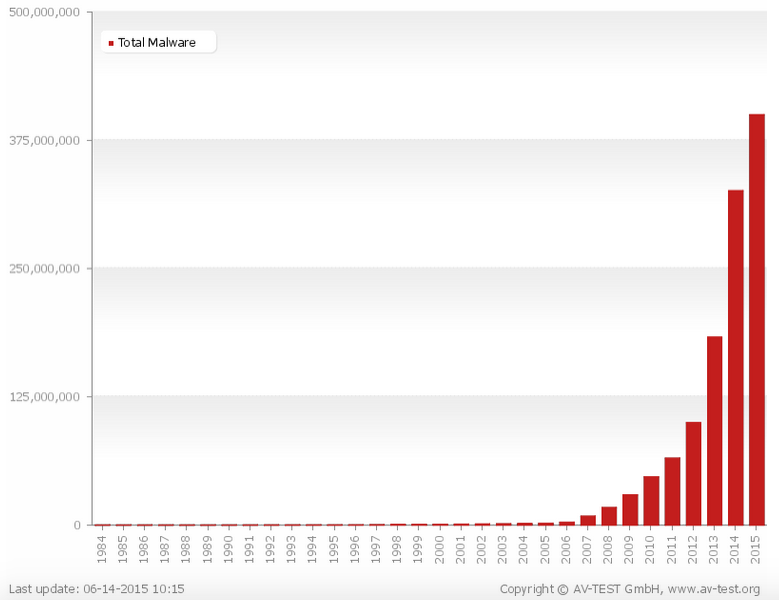
Source: AVTest Things have changed enormously since then. Now 400,000 new malware samples are discovered each day, which equates to about 3-4 malicious programs uncovered per second. This is bad news, of course, not only because of the growth of crime but also because it means that most malware does not receive the proper analysis it deserves. Reverse engineers have only so much time and so many resources. And if another 400,000 samples are coming tomorrow, who really cares? They need to pick and choose which samples they’ll analyze today. This is in stark contrast to back then when everything was analyzed in minute detail. Beyond quantitatively, malware has also changed qualitatively. When I began my career, malware wasn’t designed to make money or spy on people. Typically, viruses were written to display messages or wipe data – it was the electronic equivalent to graffiti, making a name for the program’s author(s), who were primarily immature young men. Today, government agencies and intelligence bodies have joined in, but they, and many other malware authors, no longer want to draw attention to themselves. They are after our information, and so they want to remain hidden. All of this would have seemed like science fiction when I first started out; I can’t believe we’re there. As a result of the influx in malicious programs, most malware analysis is now done by computers, which are overseen by expert analysts. This points to some good news for the road ahead. Just as criminals have seized both better technologies and the web to disseminate their attacks, so too can we use the Internet and new technology to build better systems that will help us deliver updates more quickly and collect intelligence about what is happening on our client computers. We can then begin to see trends about new outbreaks of malware, information which can be fed into the technical solutions of security firms. Clearly, much is up in the air with regards to where the security industry is going. That is why I feel that anyone who tries to predict the future must be crazy. You cannot predict anything in information security, for who in their wildest dreams could have imagined back then that we’d be where we are today? All I can say is that people will continue to abuse computers, to spy on users, and to steal information, and they will continue to invest significant resources into these efforts. DB: What is the most pressing threat facing computer users today? Do you have any recommendations for how users can protect themselves? GC: Privacy by far is the biggest threat today. The Internet began with the assumption that people could communicate with one another without being snooped or spied upon. This anonymity, this privacy, was a great thing that came with many benefits. But this tenet has been shaken. Governments around the world are beginning to try to limit users’ privacy under the logic that anonymity threatens national security. Such a mindset spells bad news for the ordinary computer user. To meet the threat of privacy, users should not only complain and go to the ballot box. They should also try to protect themselves so that intelligence agencies and ad companies are not trying to collect too much information about their online activities. Various resources are open to them, such as VPNs and encrypted email. While some of these might be complicated to use, an even greater barrier to users taking action is the fact that a large percentage of people just don’t care. I feel like most people got upset for about 20 minutes when the Edward Snowden revelations first broke. Every time a new tidbit has been published since then, people have tuned out just as quickly and have logged onto Facebook to check out their friends’ cat videos. I can tell you it’s like shouting into the wind sometimes. Governments are doing a lot today to try to scare us into thinking we need protection from this threat or that threat. For example, they argue that they can’t hope to stop terrorism unless they can see what people are doing online. Well guess what? You can’t stop terrorism even if you wanted to. There will always be those who try to use terror to reach their own ends. Of course, it’s horrific when innocent people get hurt or have their loved ones killed by terrorists, but it is still very very rare. If we give away our freedom, then the terrorists really will have won. We need to begin shying away from thinking along the lines that these and other problems are too big for us to make a difference. Collectively, we can have our voices heard. We just need to have enough people engaged in making this happen. DB: What would you recommend to someone who is looking at a career in information security? GC: That’s a tricky question for someone who first entered the field because someone liked the video games he programmed! I would say that some people could work towards gaining a career in information security by working inside an IT department. With this type of job, you may end up specializing in IT security and work your way up from there. I would also recommend everyone to never use their computer skills for criminal purposes. You hear a lot about how some penetration testers today have, shall we say, somewhat murky backgrounds. I feel that for those individuals there will always be a shadow cast over their ethics, so I would be hesitant to ever have anyone like that work for me. Similarly, if you find a vulnerability, you should always engage in responsible disclosure, working with the organization to get it fixed. No benefit comes from people going public before a firm has had a chance to fix a flaw – if you think the company isn’t listening to you, take your concerns to the media. Reckless behavior needlessly places the whole Internet at risk, especially when many companies nowadays have created bug bounties to explicitly dissuade glory-seeking researchers. Finally, if you’re interested in computer security, I strongly recommend that you should get on Twitter. I know that I hear about breaking security news on Twitter first, so it’s a great way to network with people and stay ahead of the curve. To read the first part of this interview, please click here. Graham Cluley is regular contributor to Tripwire’s The State of Security. To read some of his most recent articles, please click here.

