
Insider threat relates to malicious activity from an organization’s internal employees, contractors, or ex-employees who abused access to the company’s internal systems and applications to compromise the confidentiality, integrity, or availability concerns to critical information systems or data with or without malicious intent. Insider threat includes IT sabotage, fraud, or theft of intellectual property. Insiders may act on their own or aid an external threat actor unintentionally. It is vital that organizations understand their target insider threat use-cases, model the normal employee baseline behaviors and ensure employees understand how they can be a target by a sophisticated attacker to obtain business critical information. This article discusses the critical indicators of insider threats and suspicious or anomalous events. It also presents a design approach to model the insider threat to identify such events and high risk insiders.
Insider threat indicators
Identification of insiders is an integral part of a targeted detection strategy. Insiders can be identified based on the access to sensitive information, crown jewels, or other business critical information. General characteristics of insiders at risk of becoming a threat include the following:
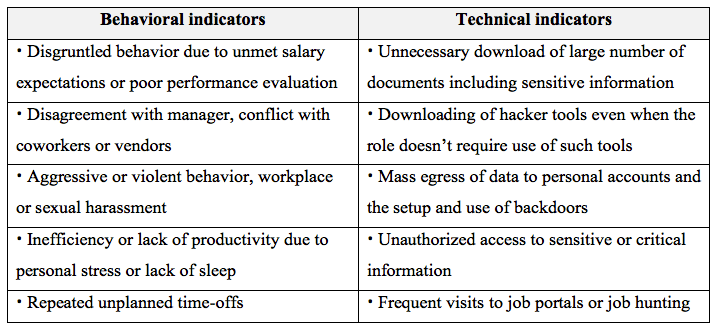
Building a baseline understanding of the normal activity behavior of the insiders will make detecting deviations in these norms easier and help identify anomalous events or activity.
Suspicious insider events
The goal of an insider is to misuse access intentionally or unintentionally to impact the confidentiality, integrity, or availability of an organization’s critical data, systems, or infrastructure.
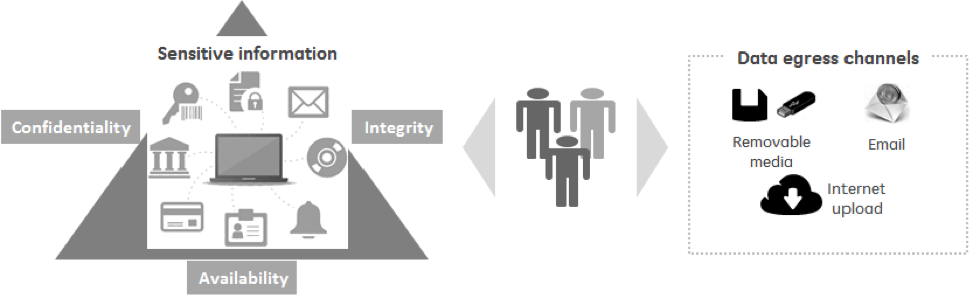
Figure 1: Insider threat events goal Some of the malicious or anomalous events that can cause insider risk in the organizations are:
- Unnecessary downloading of sensitive information (intellectual property, financial, personal) and identifying ways to egress data over personal emails, public drives, print server, USBs, and other removable media
- Configuration changes to critical infrastructure, applications, or data to cause integrity and or availability concerns
- Attempting privileged access to critical or sensitive information at multiple time-zones and or geographies beyond the normal working hours
- Unauthorized access to critical or sensitive information that's inconsistent with role requirements
Design approach
This section delves into an approach that an organization can employ to design a solution to address insider threat events and detect malicious insider activity.
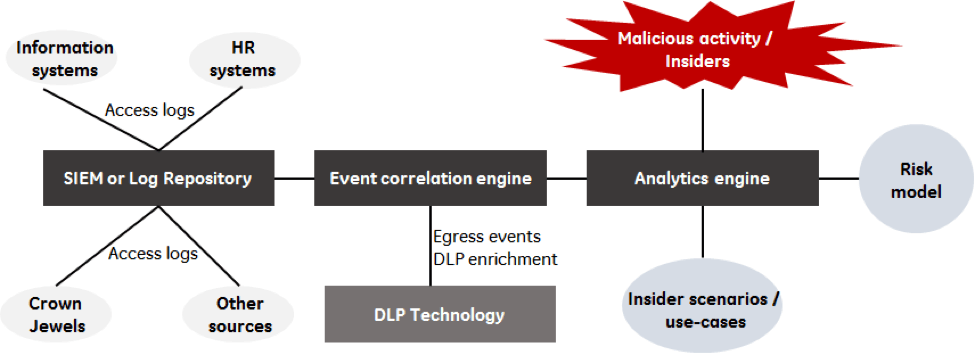
Figure 2: Insider threat model Source systems: Establish data discovery and tag sensitive data, identify crown jewels along with sensitive or mission critical data, and employ adequate measures to classify the information. SIEM or Log repository: Capture the access logs and ingest the logs into a SIEM (Security Information and Event Management) system or big data log repository. Define the retention period and storage in compliance to security and privacy policies. DLP: DLP (Data Loss Prevention) technology or agents can be installed on a company’s internal assets and endpoints to capture the events and data movement. Advanced tagging and preventive controls could also be implemented based on the nature and sensitivity of the data. Event correlation engine: Employs statistics, rules, and/or behavioral patterns. Correlate two or more events (example: system logs and DLP events) to drive insights into the data. Analytics engine: Generate targeted output (list of malicious events, insiders) or insights (data visualization) based on the specific insider threat use-cases that works in conjunction with the correlation engine and the risk model. Risk model: A risk model would help identify the anomalous events based on a baseline or set thresholds. Assign risk score to each user or identity for each anomalous event. Aggregate all the risk scores per day to identify top users or identities that require further investigation to determine any insider threat activity involved. Risk models can be maintained and updated by analysts manually or can be based on AI and machine learning algorithms.
Conclusion
Whether it’s caused by a malicious activity from an insider or an honest mistake, the threat from insiders is real and growing. It is vital that the organizations understand the insider threat, as well as have means to identify high risk users and an approach to detect and combat the insider threat. There are various tools and technologies emerging in this space, however; the success lies in identifying the organization specific use-cases. The design approach highlighted in this article provides foundations for building a targeted insider threat platform.

About the Author: Ashish Mahajan is an innovative information security leader with over 15 years of progressive responsibilities and distinguished Information Security risk, Cyber threat management, architecture and strategy experience across Financial and Industrial domains in Fortune 100 organizations. He's a pioneer of the insider threat program, Crown Jewel protection, and threat hunting programs at GE. Ashish leads global teams across Financial, Healthcare, and Industrial businesses. He's lived and worked in India, USA, China, Italy, and the UK. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

