
A battle between two rival families of malware is being blamed for the downtime that a Californian ISP suffered earlier this month. As BleepingComputer reports, customers of Sierra Tel unexpectedly found themselves without telephone and internet connectivity on April 10. In a statement issued by the ISP the following day, the blame was put firmly on "a malicious hacking event" that had disabled the Zyxel HN-51 routers in many Sierra Tel customers' homes.

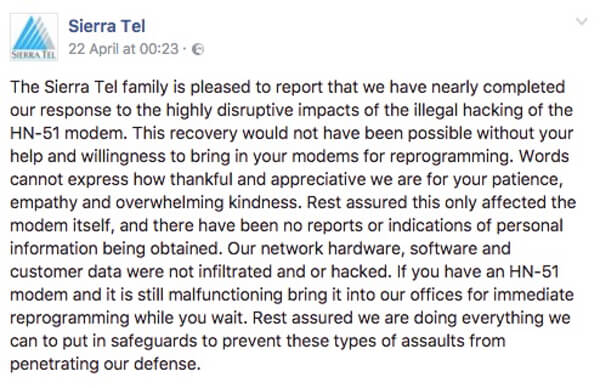
In a desperate attempt to resolve an escalating problem, Sierra Tel's affected customers were advised to physically take their broken routers into the ISP's offices and pick up a replacement. However, supply shortages meant that replacements quickly ran out, and users reliant on an internet connection had to drop off their devices and wait for news that they had been properly repaired. It took almost two weeks before Sierra Tel felt ready to announce on its Facebook page that it would soon have finished fixing the last of the affected modems:
Now, BleepingComputer reports that the blame for the outage is being put at the door of two warring malware families: Mirai and Brickerbot. Mirai needs little introduction, having infamously hijacked hundreds of thousands of IoT devices to launch a massive distributed denial-of-service attack last year against Dyn's domain name system infrastructure. BrickerBot, however, appears to be the creation of a vigilante grey-hat who goes by the online handle of "Janit0r". If his claims are to be believed, Janit0r wrote BrickerBot to firstly attempt to fix the security holes on vulnerable IoT devices and - if that fails - adopt what is euphemistically known as Plan B: Brick the devices. The thinking? A broken device can't be infected by further malware in the future, and effectively becomes the vendors' problem to sort out. You can't deny that a non-working broadband router is more likely to get the attention of the typical internet user than the standard security advisory. ICS-CERT warned organisations of the threat posed by Brickerbot earlier this month Those of you with a long memory may recall that Zyxel broadband routers were also at the centre of an attack which knocked offline customers of the UK Post Office, TalkTalk, Deutsche Telekom, and Ireland's biggest telcoms provider, Eir, offline last year. Sierra Tel seems to have worked hard to retain the support of its customers, and to be transparent in its communications about what was going on. But you can't help but feel that too many ISPs are foisting poorly protected routers onto the public, without properly considering the security implications. Much of the malware that has been seen impacting IoT devices has relied upon default passwords, or functionality which allows service providers to manage customers' hardware remotely without restricting such access to, say, the ISP's own managed network. My fear is that this won't be the last time we see innocent people inconvenienced while malware battles for control over their poorly-secured IoT gear. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc

