
Reckitt Benckiser, the household goods manufacturer of such famous products as Nurofen painkillers, Durex condoms, Dettol, and Harpic, has warned that it was hit hard by the June 27th global malware outbreak which struck power plants, airports, and government agencies in Ukraine before spreading to other multinational firms. In a sales warning for investors Reckitt Benckiser explained that the malware attack (variously referred to by different security vendors as Petya or NotPetya) that although it believed it had "largely contained" the outbreak, orders, billing and shipping were impacted at many of its factories worldwide.
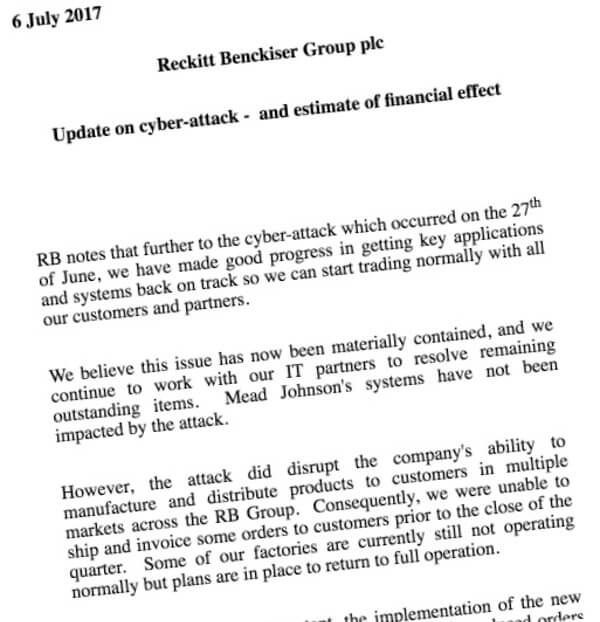
"...the attack did disrupt the company's ability to manufacture and distribute products to customers in multiple markets across the RB Group. Consequently, we were unable to ship and invoice some orders to customers prior to the close of the quarter. Some of our factories are currently still not operating normally but plans are in place to return to full operation."
In all, the company expects like-for-like sales to fall 2% in the second quarter, which equates to approximately £100 million in lost revenue. And although Reckitt Benckiser will make up for some of its losses in the next financial quarter, it's clear that the malware outbreak will leave a permanent scar on the company's fortunes:
"We expect that some of the revenue lost from Q2 will be recovered in Q3. However, the continued production difficulties in some factories mean that we also expect to lose some further revenue permanently."
Reckitt Benckiser is far from the only global company to have felt the pain of Petya. Maersk, for instance, is the world’s largest shipping company. It reported that it had been forced to redirect ships to alternative ports after the malware attack disrupted computer systems to such an extent that it was unable to allow them to dock and unload their containers. Other well-known victims of the attack include FedEx, Russian oil company Rosneft, and marketing giant WPP. No company can guarantee that it is impervious to any malware attack. Although risks can be reduced through following best practices and putting layered defences in place, it's clear that every firm should prepare its own disaster recovery plans to get up and running as soon as practically possible should the worst happen. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.

