Researchers have called for users to patch and upgrade their vulnerable software as soon as possible after three severe vulnerabilities were found in libarchive, a widely-used open source compression library. The libarchive programming library was originally developed for the FreeBSD project but is now used by software coders around the world to provide real-time access to a wide range of compressed file formats - including zip, tar, 7z, cab, and many more. The risk, explain security researchers at Cisco Talos, is that malicious attackers could create boobytrapped archive files that exploit one of the three newly discovered vulnerabilities in order to execute unauthorized malicious code on a user's computer. All an attacker would need to do is send a poisoned archive file to their intended target. And as libarchive is used by a number of file and package managers included in Linux and BSD systems, as well as security tools and file browsers including tools running on OS X and Chrome OS, it isn't necessarily trivial to ensure that your system is completely patched. In a blog post, Cisco Talos researchers summarized the problem neatly:
"Writing secure code can be difficult. The root cause of these libarchive vulnerabilities is a failure to properly validate input - data being read from a compressed file. Sadly, these types of programming errors occur over, and over again. When vulnerabilities are discovered in a piece of software such as libarchive, many third-party programs that rely on, and bundle libarchive are affected. These are what are known as common mode failures, which enable attackers to use a single attack to compromise many different programs/systems. Users are encouraged to patch all relevant programs as quickly as possible."
The Cisco blog post provides detailed information about each of the three vulnerabilities. They are:
- CVE-2016-4300 - where a specially crafted 7-Zip file can cause an integer overflow, resulting in subsequent memory corruption and code execution
- CVE-2016-4301 - where buggy code permits an attacker to cause a stack-based buffer overflow
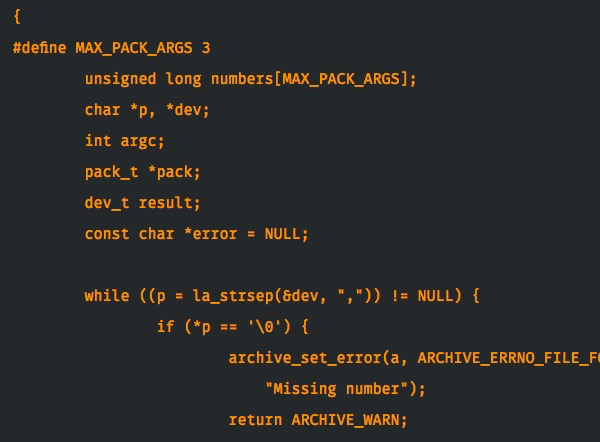
- CVE-2016-4302 - a heap overflow in the libarchive RAR restartmodel
Fortunately, the researchers (who also found serious vulnerabilities in the 7-Zip file archiving code a month ago) responsibly disclosed details of the vulnerabilities to libarchive's maintainers, and patches for the library have been released. However, it's inevitable that it will take time for the fixes to make their way into the many third-party tools that use the library, as often coders are lax in tracking vulnerability announcements in the in the code they are relying upon. The problem is compounded by the fact that the issue also impacts vendor hardware - including switches and routers - which have embedded the libarchive library as well. In short, updates are going to be trickling through for quite some time. When it comes to the crunch, all we can do is hope that vendors and software developers impacted by the libarchive flaws update their products as quickly as possible, and alert users to the need to update their systems. Otherwise, there is a very real danger that online criminals could exploit the flaws for their own advantage. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.

