
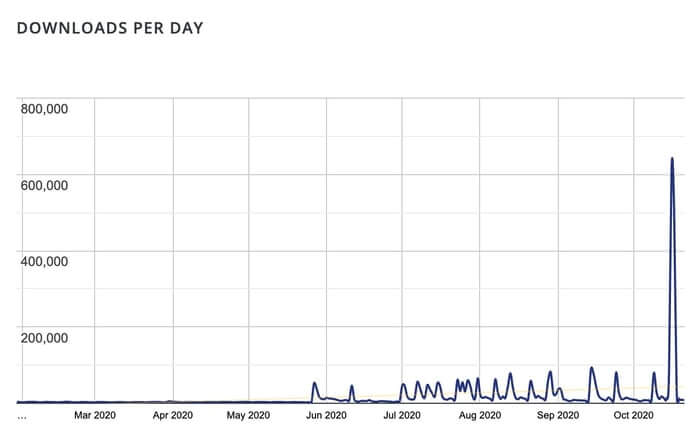
Loginizer, a popular plugin for protecting WordPress blogs from brute force attacks, has been found to contain its own severe vulnerabilities that could be exploited by hackers. The flaw, discovered by vulnerability researcher Slavco Mihajloski, opened up opportunities for cybercriminals to completely compromise WordPress sites. The flaw can be exploited if a user attempts to log into a Loginizer-protected website with a carefully-crafted username. Vulnerable versions of Loginizer did not properly validate and sanitise the username to prevent SQL injection and Cross-Site Scripting (XSS) attacks. The threat was significant, and made even more serious due to the fact that over one million sites are running the Loginizer plugin - believing it to be protecting their websites from attack. And this, it appears, is what motivated WordPress to initiate a forced update for the plugin on third-party sites running vulnerable earlier versions - even if administrators had not requested the plugin to install automatic updates. WordPress has had the ability to force updates on third-party sites since version 3.7 of the blogging platform, but it is a feature that has rarely been seen in action. That forced update, understandably, saw a massive spike in downloads for the fixed version of the Loginizer plugin.
Although most would argue that such a decision was good from the security point of view, there will no doubt be concerns from some that faceless techies at wordpress.org are able to force the installation of code on third-party sites. After all, what if a security update for a plugin, forced upon a site without the site's knowledge and permission, unexpectedly introduces a critical bug or incompatibility? Wordpress.org administrator Samuel Wood responded to a Loginizer support thread where users were questioning how their installation plugin had been updated without their permission:
"WordPress.org has the ability to turn on auto-updates for security issues in plugins. Has since WP 3.7, and we’ve used it for security releases for plugins many times."
If your WordPress-powered website is running Loginizer and has not already been updated to version 1.6.4 of the plugin already, I recommend you do so immediately. The cat is out of the bag and there may be malicious hackers exploring how they might explore the flaw on any sites that have escaped the patch. Proof-of-concept code demonstrating the flaw is scheduled to be released on November 4 2020. By then, hopefully, all sites running Loginizer will be running a version which has had the vulnerability patched.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

