Cryptocurrencies are hot. According to CoinMarketCap, there are now over 1,300 cryptocurrencies with new initial coin offerings (ICOs) accelerating all the time. Even Kodak is getting into the act with KODAKcoin. And currently, the price trajectory of Bitcoin is higher than a North Korean rocket, with Blockchain saving the world one application at a time. Cybercrime, which quickly adopted cryptocurrency as the payment method in the ransomware plague, is now turning its eye to other uses for cryptocurrency technology. We are seeing stolen account and credit card shops use the peer-to-peer DNS technology in Blockchain as a technique for bulletproofing their offerings. Jokers Stash (see Figure A), which has been linked to the Sonic Drive-In breach, is using .bazaar top level domains as an alternative to traditional DNS and tor-based naming systems.
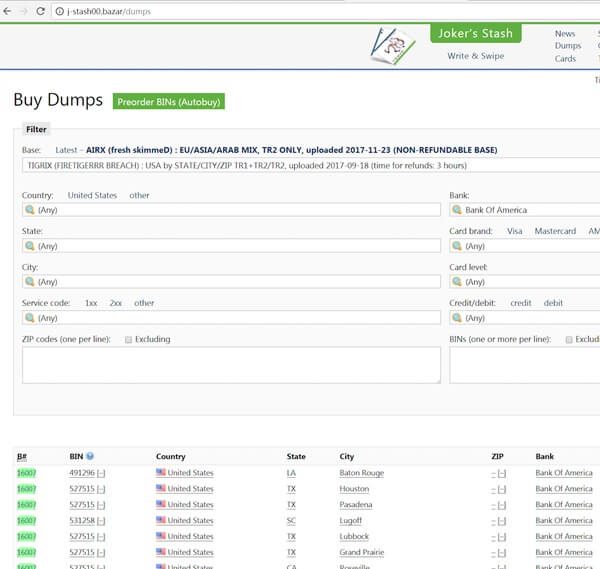
Figure A: Joker’s Stash website offering stolen account details uses a .bazaar domain, as shown in the URL at the top of this screen shot. In addition, the bandwagon for placing JavaScript that operates a coin mining function onto vulnerable websites and referred advertisements, #minevertising, has started to gallop away. We are seeing ads (see Figure B) on the dark markets offering to inject Monero JavaScript coin-miners with a criminal’s unique identifier. The result is that anyone who visits a compromised website is infected with malware that hijacks 100 percent of its CPU cycles to mine Monero cryptocurrency on the criminal’s behalf. This activity has been named cryptojacking.
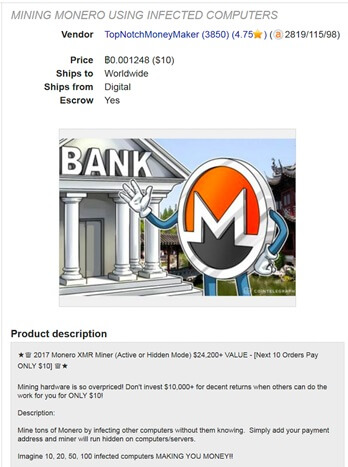
Figure B: Online ad offering Monero mining malware. A stream of high-profile sites already have fallen victim to being injected with mining JavaScript from coinhive.com. CBS’s showtime.com and cristianoronaldo.com are probably two of the most notable cases to date. The trend of the referred domains in cryptojacking JavaScript (Figure C) shows how quickly this technique accelerated in late 2017.
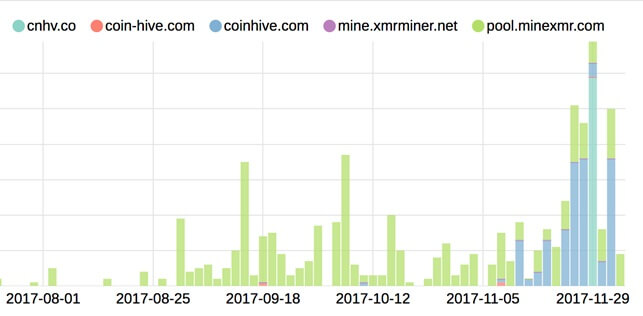
Figure C: Coinhive.com has replaced poolminexmr.com as the most popular mining domain. Cryptojacking payloads look set to become a mainstream attack in 2018. We may even see this method of monetization, which doesn’t require the victim to actually do anything, take over from current ransomware options that require victims to actively make the ransom payment. About the Author: Andy Norton is a Director of Threat Intelligence at Lastline, inc. You can find him on LinkedIn here. See how you can greatly reduce the time needed to accurately detect and protect against advanced and persistent threats, from the network edge, to endpoint systems with Tripwire Enterprise and Lastline, here. Editor’s Note: The opinions expressed in this and other guest author articles are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.

