
The emergence of IoT is especially pronounced in the workplace. Indeed, as revealed by a recent Tripwire survey, 63 percent of executives anticipate they will need to adopt "smart" things and other IoT devices due to the pressures exerted by business efficiency and productivity. Such enthusiasm notwithstanding, security has not kept up with the changing market. While a majority of executives are willing to embrace IoT, only 27 percent are "very concerned" about the risks. Additionally, security teams at both Veracode and Hewlett-Packard discovered "significant" vulnerabilities in many of the consumer IoT devices they recently analyzed in two separate studies. Enterprises might, therefore, be underestimating the challenges associated with integrating the Internet of Things into their networks. To adequately protect their organizations, security professionals and executives alike need to develop a firmer grasp of the security risks involved in connecting IoT devices to enterprise networks. Fortunately, this was the explicit purpose behind publishing the OpenDNS 2015 IoT Report (PDF).
The State of IoT
OpenDNS, a proactive domain name service (DNS) security firm, published its study after conducting a detailed analysis of the DNS requests crossing over its network. (Typically, the firm processes approximately 70 billion requests on a daily basis.) Due to the high volume of requests, OpenDNS sampled its data on February 15, March 15, and April 15 of this year, after which it sanitized and in some cases enriched the requests using OpenDNS, Shodan and MaxMind. Via this methodology, the firm found that five different categories of IoT devices – personal electronics, consumer appliances, home/office automation, security and monitoring, and platform-based – were partially or wholly present in 56 industry verticals. The firm found the greatest query count in three verticals in particular: higher education, managed service providers and healthcare at 6,451; 6,298; and 5,557 queries, respectively. Digging deeper, the study revealed some 879 fully qualified domain names (FQDNs), or DNS entries associated with an identified list of parent domain names, that were each uniquely related to IoT infrastructure.
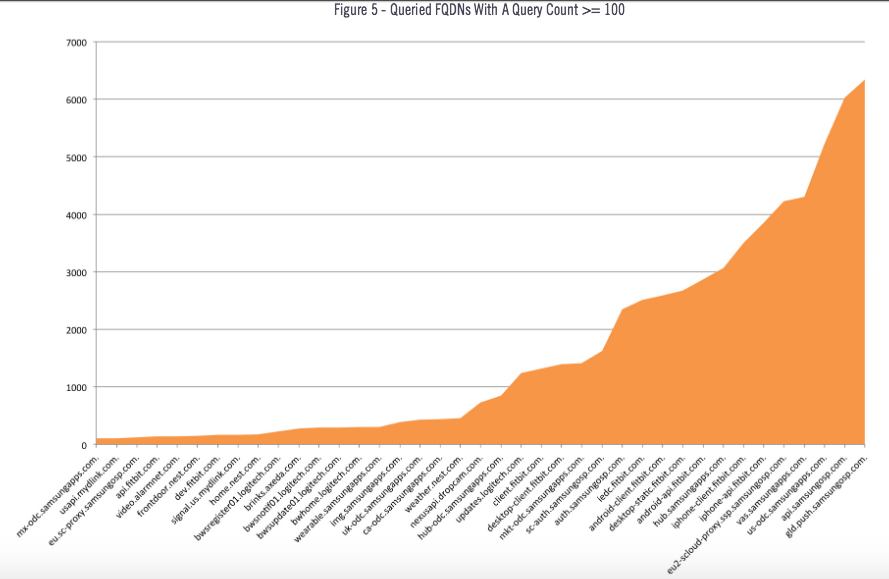
Source: OpenDNS Many of these pertained to Samsung, which led OpenDNS to analyze the electronic manufacturer's smart TV. (These television sets are commonly used in boardrooms. Furthermore, they made headlines earlier this year when it was revealed that their voice recognition feature could be listening in on users' conversations.) The researchers arrived at the following observations:
"Nothing directly malicious was found in the examination of the Samsung Smart TV’s network communications, however the behavior of the xpu.samsungelectronics.com does not fit into any logical use case," they explained. "Additionally the frequency with which the Smart TV makes requests to this domain makes it significantly easier for Samsung to track the overall usage of the device. It is our opinion that the average user does not expect their Smart TV to make incessant external calls to various services without any interaction. The fact that a Smart TV does so almost every minute it’s powered on – even without user interaction – is concerning because it makes the use of these devices much easier to determine from outside a corporate network."
OpenDNS went on to identify some 46 different IoT hosting providers, with Amazon, SoftLayer Technologies, Verizon Business, Fastly, E.I. du Pont de Nemours and Co. ranking in at the top five. (Approximately 83.99 percent of IoT hosting infrastructure is located in the United States.) While it revealed that the hosting providers are taking the time to incorporate resiliency into their platforms ahead of major service interruptions, the researchers' analysis also uncovered more than 15,000 malicious domains observed to be sharing infrastructure with legitimate IoT product vendors' infrastructure. Five ASNs in particular – AS22773 (Cox Communications), AS20940 (Akamai International), AS20115 (Charter Communications), AS701 (Verizon Business), and AS3356 (Level 3 Communications) – registered a large number of malicious domains blocked; they were used by Western Digital, Logitech and Leapfrog, among other companies.
"Organizations need heightened awareness around IoT vendors’ choice of network neighborhoods, and how sullied those neighborhoods are," OpenDNS observed. "It’s far easier for an upstream ISP, or even one of your own firewall administrators, to block access to an IP address or subnet than to explicitly block a list of malicious domains. If not carefully scrutinized, your ISP or firewall administrator could prevent your IoT device from communicating with its cloud or hosted service."
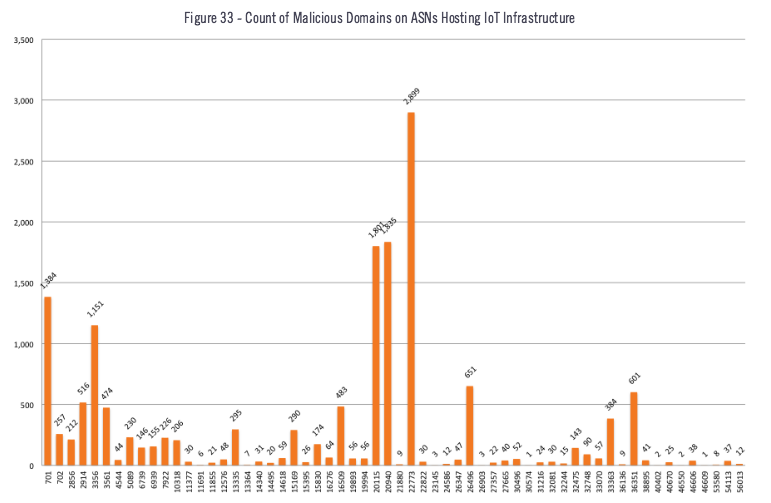
Source: OpenDNS The DNS security firm also recommended that IoT vendors vet potential platform candidates in order to avoid becoming blocked for associated malicious activity, which could include exploits of Heartbleed, FREAK and other high-profile vulnerabilities.
Conclusion
OpenDNS' report highlights the fact that while their numbers may have grown in recent years, IoT devices continue to introduce new routes for potential remote exploitation of enterprise networks. Furthermore, much of the infrastructure used to enable IoT devices is beyond any direct control by the user or IT, whose casual approach to IoT management could leave enterprises vulnerable. Indeed, in a survey OpenDNS conducted of 500 IT security professionals and 500 consumers, the firm found that 75 percent of infosec personnel work at organizations that have policies for IoT devices in place and that approximately an equal percentage (77 percent) feel that they can manage IoT risks. This is despite the fact that when it comes to mitigating risks, 23 percent of IT pros said they had no mitigation controls in place, and nearly half (43 percent) said they use credentials only. Going forward, the onus is on organizations to understand the risks posed by each and every IoT device installed on their networks. To learn more about how you can help protect your enterprise against the risks of IoT, please read OpenDNS' study here. Title image courtesy of ShutterStock

