
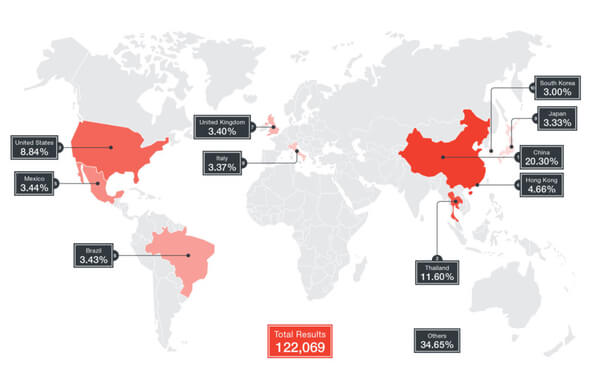
Internet-connected cameras around the world are once again being hijacked by malicious hackers in order to carry out distributed denial-of-service (DDoS) attacks. Security researchers at Trend Micro have identified that over 1,000 different models of Internet Protocol (IP) cameras are at risk of being compromised by the threat dubbed Persirai, which gains access to the IP camera's web interface via TCP Port 81. After an attacker logs into the vulnerable interface, commands can be injected to force the IP camera to connect to a remote server, from where malicious code and instructions can be downloaded. The hijacked cameras then hunt for other vulnerable devices connected to the internet, exploiting a zero-day vulnerability which can steal the password file. Using Shodan, a search engine that crawls the internet for connected devices, researchers were able to discover 122,069 vulnerable internet-connected cameras - with most at-risk devices found in China (20.3%), Thailand (11.6%) and the United States (8.8%).
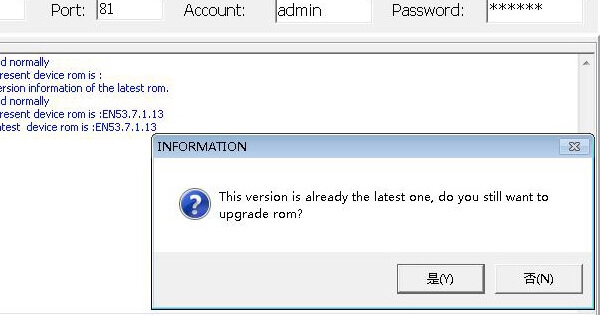
Owners of the Chinese-made wireless cameras are likely to be oblivious to the fact that their devices have been infected with malware, and are now under the control of malicious hackers who could easily direct them to launch DDoS attacks against internet services in a similar fashion to the infamous Mirai worm. A large number of the infected devices are thought to still be using the default password that they shipped with, making it child's play to hack the devices. It should go without saying that not changing default passwords on internet-enabled devices is a classic error that makes life all too easy for online criminals. Unfortunately, in this case, a unique password does not appear to be enough to protect devices - as the zero-day vulnerability can be exploited to steal the password file regardless. The best solution, therefore, is to either block your at-risk IP camera from being accessible from the public internet, or install a firmware update from the manufacturer. Trend Micro's researchers claim that at least one of the affected manufacturers said that they had addressed the security issue with a firmware update, but other at-risk IP cameras continue to believe that they are already running the latest version.
Intriguingly, researchers report that the command & control (C&C) servers sending instructions to the botnet use the .IR country code which is not available to non-Iranians, and special Persian characters are used in the malware. The suggestion, therefore, is that the botnet is likely to being controlled by hackers with a link to Iran. Internet-of-things devices are being exploited with all too much regularity, and with serious consequences. It's no wonder that last year the Department of Homeland Security issued a warning to users and system administrators about the steps they should take to harden their IoT security. These tips include:
- Ensure all default passwords are changed to strong passwords. Default usernames and passwords for most devices can easily be found on the Internet, making devices with default passwords extremely vulnerable.
- Update IoT devices with security patches as soon as patches become available.
- Disable Universal Plug and Play (UPnP) on routers unless absolutely necessary.
- Purchase IoT devices from companies with a reputation for providing secure devices.
- Consumers should be aware of the capabilities of the devices and appliances installed in their homes and businesses. If a device comes with a default password or an open Wi-Fi connection, consumers should change the password and only allow it to operate on a home network with a secured Wi-Fi router.
- Understand the capabilities of any medical devices intended for at-home use. If the device transmits data or can be operated remotely, it has the potential to be infected.
Stay safe folks.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

