As information security professionals, we have come across hundreds, if not thousands, of phishing attacks in our time.
Our experience tells us that all phishes have certain things in common. Daniel Magana, IT Security Analyst at Tripwire, identifies three such characteristics:
- Requests personal information – Phishing emails will commonly ask for a target’s name, phone number, address, account number, social security number, etc.
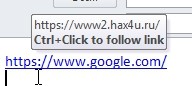
- Bad or forged links – Links in phishing emails may look legitimate but upon closer inspection, the target can usually find misspellings or a different suffix than expected, such as .biz instead of .com).
- Sense of Urgency – Phishers try to create a sense of urgency in their targets, like threatening to close a target’s account or delete their information if they do not respond in a timely manner.
However, we also know that no two phishing attacks are alike. This not only applies to the number of platforms phishers use to target their victims, including email, social media and SMS, but also to the manner in which they launch their attacks.
Let’s face it: some scammers are truly gifted in the art of deception, whereas others are downright terrible.
Here are some tips to help us discern a bad phish from a good one:
BAD PHISHING: SLOPPY “SIRS” AND “MADAMS”
Dwayne Melancon, CTO of Tripwire, observes that spotting a phish is not always so difficult, saying, “Most phishing scams are fairly obvious; lots of grammatical errors and misspelled words, the sender’s email address doesn’t match the name included in the body of the email, and so forth.”
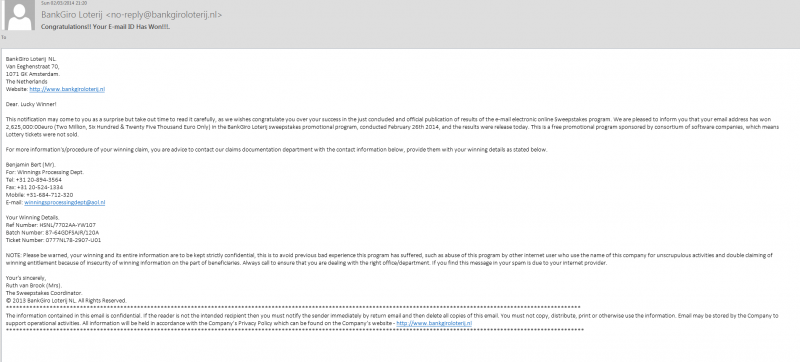
That’s not to say that all emails with misspelled words or incorrect email addresses are scams. However, it should, in the very least, send up a red flag, since most people would proofread their correspondence before sending it.
Additionally, phishing is all about social engineering, so scams that lack some personalization tend to trick users less. Magana explains: “Since phishing emails are commonly sent in large batches, phishers tend to use a generic greeting, such as ‘Dear Customer,’ ‘Dear Sir or Madam,’ or even a simple ‘Hello.’
Most reputable organizations have methods to personalize emails even when sending in large batches, so be on the lookout for messages with these types of greetings.”
GOOD PHISHING: FALSE FAMILIARITY
Successful phishing scams, by contrast, do not draw attention to their spelling or greetings. “Some scams are quite deceptive with professional-looking graphics and convincing calls-to-action,” said Melancon.
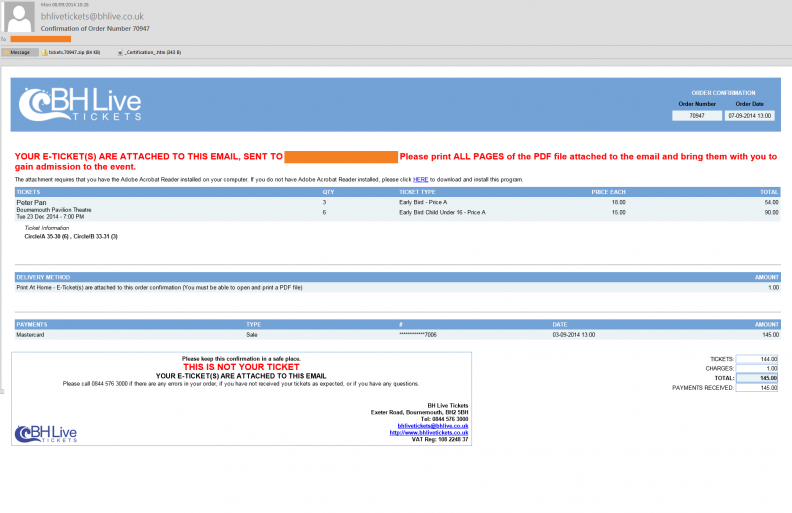
Those that truly succeed are those that make it sound like the sender truly knows the victim or has a legitimate purpose for contacting him or her, added Melancon.
An important part of lulling targets into this false sense of familiarity is using “RE” in the subject line. Lori MacVittie, Security Evangelist for F5 Networks, expands upon this tendency: “A lot of phishing scams rely on the fact that we send a lot of e-mail—so much so we can’t remember every conversation we may have started or have been involved in. The use of ‘RE’ in the subject line is intended to exploit this reality and convince you it is a ‘safe’ conversation.”
Some phishers take it up a notch, attempting to lure users through a more sophisticated phishing tactic. Melancon is well aware of this brand of scamming, stating, “The most dangerous are ‘spearphishing’ scams, in which the attacker specifically targets you as an individual (as opposed to scamming a huge list of people).”
In these cases, the attackers mine social media, buy information about you, or know you well enough to inject personalized information into the phishing email, explains Melancon.
HOW TO PROTECT YOURSELF AGAINST PHISHING SCAMS
Given the wide variety of phishing attacks, it is important that we all know what to do when we come across what we suspect might be a phish. Hence, here are a few suggestions for how you can protect yourself against these phishing attacks.
Tip #1: If It Sounds Too Good to be True, Leave It Alone
We may receive messages out of the blue that offer us money, fame or other valuable gifts. For those that seem too ridiculous to be real, it’s better to just leave those alone.
Thom Langford, one of the founding members of Host Unknown, weighs in on this recommendation: “I have yet to come across an example of when someone really was giving away iPad’s, cash or holidays without some kind of quid pro quo involved. If you feel that the message might be too good to be true, the email and its contents can probably be ignored.”
Of course, the same logic applies on mobile phones, as Georgia Weidman rightly notes: “If you get a text message that says you have won a $500 gift card to <store> and log in here to claim your prize with a link, chances are it’s not a good idea to log in with your legitimate <store> credentials (Not that I’m speaking from experience here or anything). Always remember if it sounds too good to be true, then it probably is.”
Tip #2: Don’t Click Anything!
If you feel a message is trying to phish you, don’t click on any links. “There are some very real implications and consequences if we unwittingly click on a phishing link,” reiterated Melancon. “Be very cautious when clicking on links in emails and watch the URL bar for strange addresses.”
With this in mind, it’s very important to hover over any suspicious link and see if the embedded URL matches the link’s display text.
Neira Jones, chair of the Advisory Board for mobile innovator Ensygnia & the Global Advisory Board for Centre for Strategic Cybercrime & Security Science, also recommends that we look a bit closer at unfamiliar links and do some investigative work.
“Start from the right-hand most full stop, such as in ‘genuinedomain.com.’ If ‘genuinedomain’ is the correct spelling of a company you normally associate with, then OK. But if it looks like ‘genuinedomain.com.maliciousdomain.com,’ you’re in trouble!”
We can also type the link’s text directly into a browser, as MacVittie suggests: “Typing in a suspicious URL helps in two ways: first, it makes you pay attention to the URL and any oddities that may be included (extra host names, odd-sounding domains, etc.); and second, if the proffered link is portrayed as being an official one, it will actually take you to the site you intended to visit rather than whatever lurks beneath in the HTML. You’ll very quickly know whether or not you’ve been targeted when the site isn’t able to serve up that URL.”
Tip #3: Know Who’s In Your Network
We may at times receive potential phishing scams from our friends or colleagues. If we suspect we are being phished, we need to ask ourselves if their behavior matches with what we already know to be true about how they generally act and behave.
Langford provides us with an example: “Is the email from a close friend, but they haven’t addressed you by your nickname, they seem oddly formal, and/or they have more spelling mistakes (or even not enough) in their message? It could be that they have been compromised and you are in their address book and are therefore being targeted.”
If there is any doubt in our minds, we can call that person and ask them if they intended to send that particular message.
The same goes for strange correspondence from banks and other companies. “Contact the organization directly by manually going to their website or calling their support line,” recommends Magana. “If there is indeed an issue with your account, they will be able to help.”
Tip #4: Outbound Secure Gateways and Threaded Conversations
Aside from what we can do on an individual level to protect ourselves, there are a number of ways we can help protect our companies from being phished. One effective resource is corporate outbound secure gateways.
“Most have URL and host filtering, maintain large and up-to-date databases of known ‘bad’ sites and can assist users by preventing them from ever reaching a potentially dangerous site after ignoring the admonition not to click on unknown links,” said MacVittie.
“Open communication with employees and regular updates that incorporate newly discovered scams are important parts of this solution.”
Additionally, when it comes to phishers using “RE” in their message subject lines, we should encourage everyone in our corporate environment to use threaded conversations. As MacVittie explains, this will help us identify messages that are really phishing scams posing as just another e-mail in a legitimate conversation and those that are actually part of legitimate conversations.
COMMON SENSE: OUR GREATEST ANTI-PHISH WEAPON
Phishers vary in their ability to make us click on suspicious links. But regardless of the content of their message, our common sense goes a long way in helping us identify fake messages and scams.
Common sense that something is too good to be true; common sense to hover over a link before clicking on it; and common sense to know who the people are in our networks and how they generally behave toward us.
Armed with this healthy dose of skepticism, we are well-equipped to spot every scam, no matter how ingeniously crafted and subsequently maintain the integrity of our information.
Continue Learning
Read the Guide: Cybersecurity Is Everyone's Job
How to build a cyber-secure culture at your organization

