
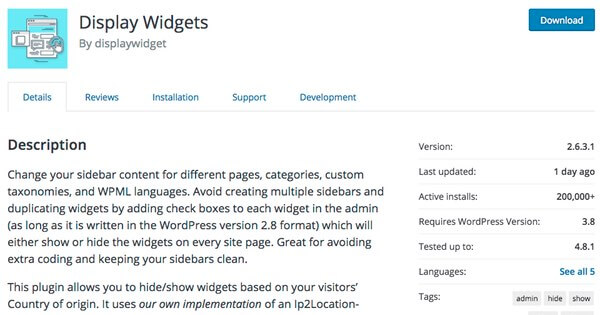
As many as 200,000 websites may have been running a WordPress plugin that allowed third parties to publish any content they wished on victims' sites via a backdoor. The popular Display Widgets plugin was removed from the official WordPress.org plugin repository after it was found collecting information about website visitors and inserting content into sites. Sneakily, the plugin prevented logged-in users from being able to see the spammy content it was introducing into sites, presumably in an attempt to avoid attracting the unwanted attention of website administrators. Concerns over Display Widgets plugin were first raised in June by British SEO consultant David Law, after he spotted it breaking various repository rules and potentially damaging WordPress users' sites.
Over the coming weeks, the WordPress.org plugin team removed offending version of Display Widgets from their site - only for it to be replaced with new versions containing malicious code. WordPress security firm WordFence published a warning earlier this week that the plugin was not to be trusted, uncovering that Display Widgets' code had changed ownership shortly before complaints began to be made of its malicious behaviour. Sure enough, if you visit the website of Strategy11 (the original developers of the plugin) you'll see confirmation that the plugin was sold to its new owners in May:
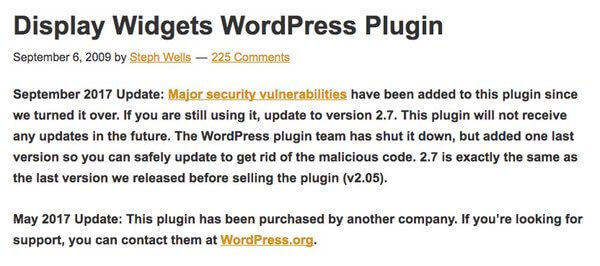
Stephanie Wells of Strategy11 confirmed to WordFence that her company had sold the Display Widgets plugin to someone called "Mason Soiza" for $15,000 earlier this year, after he expressed a desire to take over its development and "make it work better" with the latest versions of WordPress. "Mason Soiza", who also appears to go by the name of "Kevin Danna", appears to be an interesting character - and WordFence has done some detailed detective work investigating his various business ventures, glamorous lifestyle, and shady online activities. However, this article's purpose isn't about what Soiza's intentions may have been as he bought up a number of different popular website plugins. Instead, I'd like to take this opportunity to remind all website owners of the importance of recognising the risks that can come through third-party plugins. Even if you have used a WordPress plugin for many years without issue, there is always the risk that ownership of the plugin could pass into the hands of someone with malicious intentions - opening you up to the risk of a supply chain attack. Supply chain attacks - which target victims by compromising the systems of an upstream hardware or software provider - are becoming increasingly popular, and the rewards for criminals can be so great that they may have no qualms about paying thousands of dollars to buy complete control over plugin code running on your webserver rather than attempting to hack their way into the original developers' systems. If you give a third-party WordPress plugin permission to run on your server, you are trusting it to behave responsibly. In Display Widgets' case it was being used to create spammy pages advertising financial and escort services, but it could just as easily have been used in an attempt to infect visiting computers with malware - and potentially damage your company's brand. For now, the team at WordPress.org have replaced the poisoned edition of Display Widgets with a "safe" version (version 2.7), which has excised the malicious code. According to WordPress.org, there won't be any more updates to Display Widgets as the plugin is being shut down for good, and the code is not available for new users to download. Obviously websites using Display Widgets would be wise to update their systems as soon as possible, and then (probably) remove the plugin altogether as it will no longer be supported. But it's only a matter of time before the next WordPress plugin (or Joomla, or Drupal, or...) finds itself under new ownership, putting the safety and security of websites and their visitors at risk. My advice? Keep plugins to a minimum on your website, read reviews to judge which plugins are trusted the most (although this wouldn't have helped much in Display Widgets' case), and raise an querulous eyebrow if one of the plugins you use is unexpectedly removed from the WordPress.org repository. For more information on "Mason Soiza" and how Display Widgets turned malicious, be sure to read Wordfence's fascinating write-up.

