
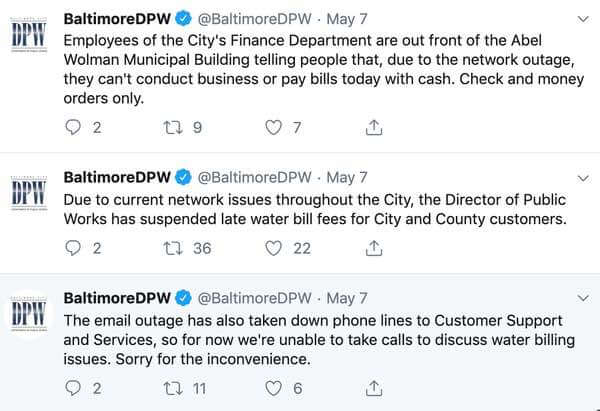
For the second time in a year, Baltimore city government computers have been infected by ransomware. Malicious hackers are demanding that a ransom is paid for the safe recovery of encrypted files on affected computers and servers. On Tuesday, Mayor Bernard C. “Jack” Young tweeted how the city had "shut down the majority of its servers" out of "an abundance of caution," but that the city's core essential services (such as police and fire brigades) remained operational. However, the email systems used by municipal employees, phone lines and online bill payments were impacted by the attack. Amongst those workers affected were Baltimore's Department of Public Works (DPW) who reported that their customer support line was unable to take calls due to its network being down, and was suspending customers' late water bill fees as it was unable to accept payments other than those delivered via cheque or money order.
According to Mayor Young, the City of Baltimore had seen no evidence that any personal data had been exfiltrated from the compromised computers. That's normal with ransomware - the attackers are typically not interested in the content of the files and documents that you store on your network of computers - they simply want to deny you your access to them. Frank Johnson, Baltimore's Chief Information Officer, confirmed in a press conference streamed via Facebook that the offending malware was the "very aggressive RobbinHood ransomware", and specifically that the FBI had identified it as a "fairly new variant." It's unclear whether the variant of the RobbinHood malware is the same as that which hit the network of the city of Greenville, North Carolina, last month. In that incident, the city was forced to shut down the majority of its servers - although similarly police and fire emergency communications were not impacted. Reporters at the Baltimore Sun managed to get a copy of the ransom note displayed by the malware on affected Baltimore government computers, and confirmed that it was initially requesting 3 Bitcoins (approximately US $18,000) for the recovery of encrypted files on each computer, or 13 Bitcoins (US $78,000) for the release of all the city's files.
"We’ve watching you for days and we’ve worked on your systems to gain full access to your company and bypass all of your protections." "We won’t talk more, all we know is MONEY!. Hurry up! Tik Tak, Tik Tak, Tik Tak!"
Just last month we described how the RobbinHood ransomware would, on the fourth day following encryption, increase its extortion demand by $10,000 every 24 hours.

After 10 days, if the RobbinHood ransomware is to be believed, the City of Baltimore would be unable to recover their data at all. In March 2018, Baltimore's 911 automated dispatch system was taken offline by a ransomware attack. It was later determined that a member of IT staff accidentally misconfigured a firewall in the hours before the attack, allowing the ransomware to successfully infect the city's computer-aided dispatch (CAD) system. Questions will no doubt be asked as to whether lessons were properly learned after the earlier ransomware attack, and if this latest ransomware infection could have been avoided. At the very least, this latest incident is a reminder to organisations of all sizes of the essential need for a layered defence and a comprehensive backup and disaster recovery process in preparation should an attacker manage to break through in future.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

