Yesterday, we at The State of Security offered a recap of some of the notable presentations that have occurred at RSA Conference USA 2016. We now continue our coverage of this week's event with Part 2 of our RSA Conference 2016 Takeaways series.
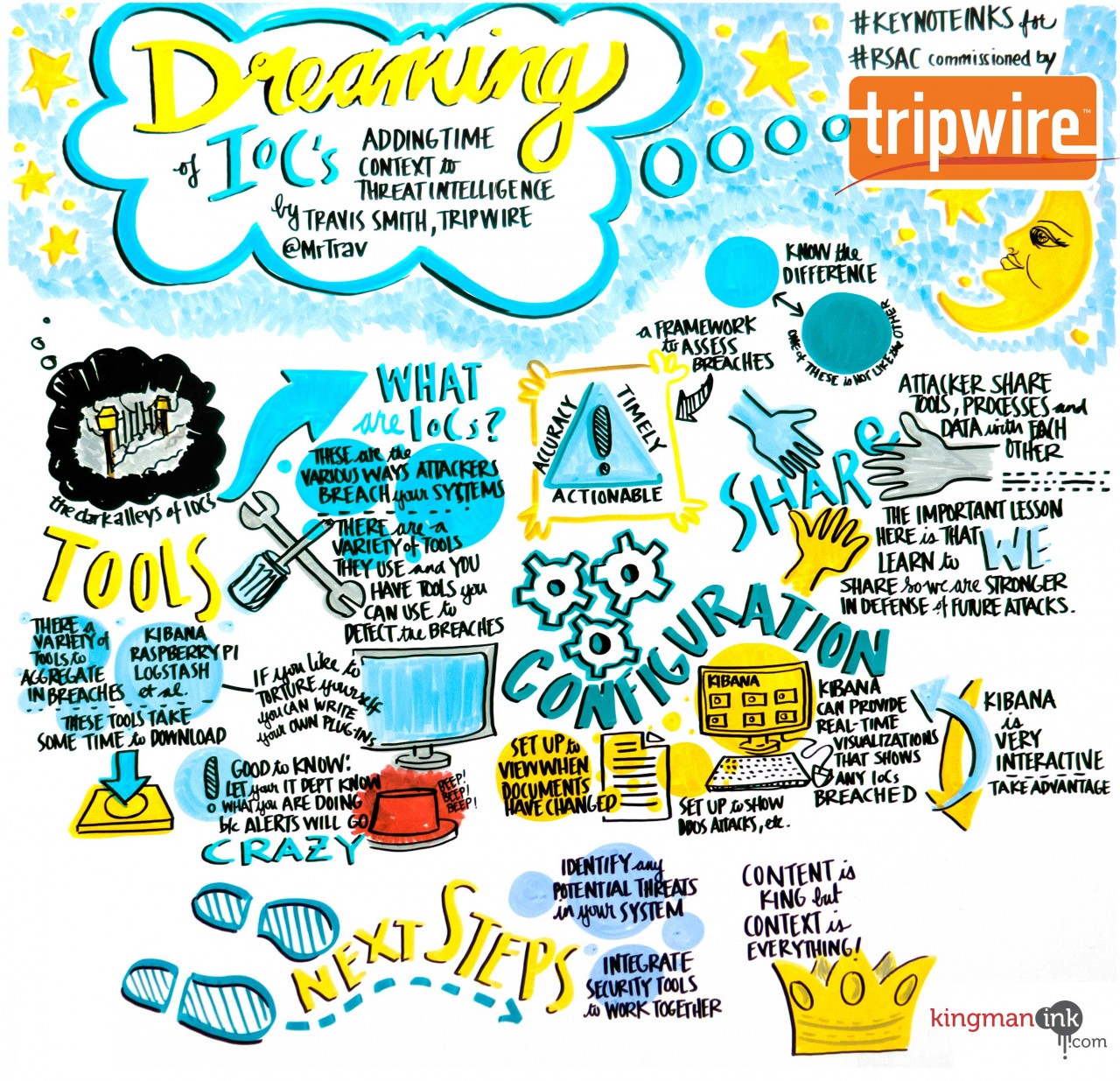
Dreaming of IoCs: Adding Time Context to Threat Intelligence
Speaker: Travis Smith (@MrTrav), Senior Security Research Engineer, Tripwire, Inc. Travis Smith, a Senior Security Research Engineer here at Tripwire, discussed the importance of context when gathering security data. Many organizations today collect this data from systems, applications, and network devices as a way to get alerts of abnormal behavior. However, Smith noted that security data is more than big data – it’s morbidly obese data – and the more data we collect, the more noise it collects. This is where time context and threat intelligence proves extremely helpful. Smith gave an overview of the various forms of threat intelligence sources, as well as their pros and cons. He went on to introduce TARDIS – an open-source framework he developed, which helps perform historical searches using attack signatures. TARDIS covers threat analysis, reconnaissance, and data intelligence systems by taking the data of Indicators of Compromise (IoCs) and looking at historical logs for signs of exploitation. By adding valuable time context to threat intelligence, Smith said organizations can pinpoint exactly when a breach occurred, as well as gain other critical forensic analysis information. See his presentation slides here.
Avoid Epic Fails: Elements of Successful Breach Notification and Response
Speakers:
- Heidi Shey (@heidishey), Senior Analyst, Forrester Research
- Bo Holland (Bo Holland), CEO, AllClear ID
- Lisa Sotto (@lisasotto), Partner, Hunton & Williams
- Matt Prevost (@Prevost2121), Vice President, Cyber & Technology Product Manager, Chubb
When we think about incident response, so much of that attention is given to the technical components and not enough to the customer aspects, said Heidi Shey, senior analyst at Forrester Research. In this panel, the speakers discussed what to do when responding to a breach and notifying customers, as well as how to manage that risk. The majority of the audience said they had received a breach letter notification – a few more than once – so it’s evident organizations need to think of themselves in that situation. One important point made was that if an organization is not legally required to disclose a breach, should they still do so? This may apply when the information leaked is not subject to data breach notification laws, such as children’s data, geolocation, or chat logs. The panelists emphasized that we shouldn’t expect the bad guys to keep stolen data a secret – the last thing you’d want is for someone to report the breach before your company has properly framed it. You have to consider the potential reputational harm it could cause and ensure that you will be able to maintain your relationship with customers after the fact. However, even if an organization has done everything correct legally, it doesn’t necessarily mean they have a good incident response strategy. Panelists were also asked: What constitutes a successful job with customer-facing notification and response? If customers feel like they were not taken care of and that the company did not care about the compromise of their customer’s information, they will try to move away from the business.
“If customers feel like you have their back, they are actually quite forgiving and willing to come back,” said Bo Holland.
Furthermore, there are several cases where being in front of the media and showing preparedness turned out to be a a good thing. Everything is about trust, stressed Lisa Sotto. Be honest, contrite and forthright. Other key takeaways from this session included:
- Don’t notify too early – It’s better to wait until you have all the facts.
- Show evidence of due diligence – Use data flow maps, interviews, and ongoing monitoring.
- Ensure employees are aware of what is going on – If a customer knows more than they do, it’s not a good thing.
Tracking Hackers on Your Network with Sysinternals Sysmon
Speaker: Mark Russinovich (@markrussinovich), Chief Technology Officer, Microsoft Azure, Microsoft (Craig Young, attendee): In this session, the Azure CTO and sysinternals author explained how the sysmon tool from this suite can be used to identify malicious activity on a Windows PC or server. Through demonstration and documentation, steps were shown for identifying activity typical of malware, tracking the source of malware, and providing enhanced forensic collection from compromised hosts. In one example, Russinovich showed how he was able to find that his mother's computer was repeatedly getting infected via a signed binary, which had slipped past Microsoft Security Essentials and found its way to be added as a scheduled task. Other features included detecting direct disk access commonly used to steal password hashes as well as alerting on thread injection, timestamp modification and network socket activity. Perhaps of greatest interest to me, however, was learning about the so-called detonation chamber Microsoft uses to identify malicious content in Outlook 365 attachments as well as 0-day Internet Explorer exploits. This second use of the detonation chamber involves having automated IE sessions browsing the web while monitoring for processes created by IE. An example was shown of an exploit identified with sysmon in December. If you missed the session and are an administrator or simply a user of Windows systems, it is worth looking into sysmon and the other sysinternals tools if you are not already using them.
The (Inevitable?) Decline of the Digital Age…
Speaker: Mark McLaughlin (Mark McLaughlin), Chairman, President and CEO, Palo Alto Networks In his keynote presentation, Palo Alto Networks CEO Mark McLaughlin stressed that organizations need to be more concerned about consumers losing digital trust. He mentioned several new challenges for security today: the fact that physical and cyber are more and more blending together, how data is massively aggregated and available, and that computing power is limitless.
"These things combined mean that security goes way beyond technology – it transcends," he said. He made the analogy that security is like fabric – you can’t fix it without tearing it.
McLaughlin then stressed that the industry needs to work on maintaining and restoring trust because a lot of it has been lost already. Lastly, he addressed the importance of threat sharing and organizations cooperating and collaborating for the greater good.
"The security industry should not compete with what we know, we should compete with what we can do with it."
Are you attending RSA this year? If you are, please visit us at Booth #3301 to learn about all the exciting things Tripwire has planned for this year’s conference. In the meantime, please stay tuned for more coverage of RSA Conference 2016!

