
Users of popular online forums are being advised to change their passwords following the leak of some 45 million credentials. As LeakedSource reports, millions of user credentials from over 1,100 websites and communities - including techsupportforum.com, autoguide.com, petsguide.com and motorcycle.com - have been exposed after parent company VerticalScope suffered a previously undisclosed hack in February. VerticalScope confirmed the breach obliquely in a security advisory posted on its website, where it described how it was rolling out stricter password rules:
"...we recently became aware of potential risks to community accounts (username, userid, encrypted password and email address) on many Forum online communities, including some owned and operated by VerticalScope. To be safe, these changes are being implemented on all of our Forum communities to help protect all of our users on each of our websites."
A ZDNet report provides more information, explaining that many of the affected websites appear to have been running outdated versions of the VBulletin forum software and did not have elementary HTTPS in place to prevent man-in-the-middle attackers from simply sniffing passwords as users logged in. Furthermore, if LeakedSource is to be believed, most of the records (over 40 million) were using the MD5 hashing algorithm to store passwords - a technique which is not felt to provide adequate protection against password cracking. What does this mean if you are one of the many users of VerticalScope's popular and varied online forums? You should obviously change your passwords as soon as possible. And ensure that you are not using the same password anywhere else on the internet. After all, you may not care that much if your account on petsguide.com is compromised, but if a hacker were to use that same information to break into your Gmail account, you may feel very differently about things. But the data breach also throws up another interesting question: just why are so many people seemingly using the same bizarre passwords? LeakedSource's analysis of the leaked data reveals, for instance, that over 91,000 people appear to have chosen to use the password "18atcskd2w," making it the second most popular password in the haul. It's nestled between the sadly, rather more predictable "123456" and "password":
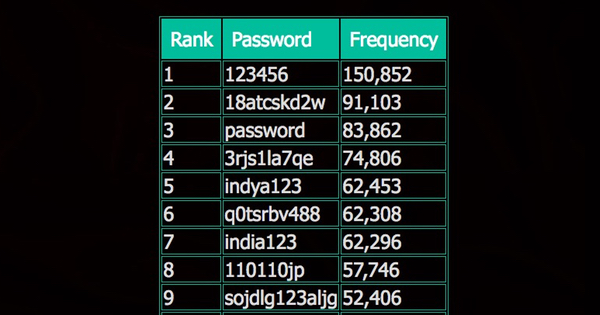
Can so many people really be choosing to protect their online accounts with the same, seemingly random choice of "18atcskd2w", "3rjs1la7qe," or "q0tsrbv488"? The answer, of course, is no. People are not choosing those passwords. Yes, those credentials can be found amongst the stolen data, and those passwords are being used on many tens of thousands of accounts, but it wasn't a human being who chose that password. It was a computer. Human brains were responsible for choosing passwords like "123456", "password," and "qwerty." But there is no way that 91,103 people independently chose to secure their accounts with "18atcskd2w." Instead, what I believe happened is that these accounts were created by bots, perhaps with the intention of posting spam onto the forums. If a user forum does not have strong measures in place to verify that an account is being registered by a living, breathing human being, it's relatively trivial for someone with mischievous intent to write a program that creates multiple accounts for the purposes of spreading spammy messages or malicious links. It's equally possible for the ne'er-do-well to generate a random password for each of their bot accounts, but that clearly requires more coding effort on their part and can complicate the later exploitation of the accounts because of the need to remember which password goes with which rogue account. All in all, it's easier for a spammer who is creating tens of thousands of accounts to use the same password over and over again - especially if the site doesn't appear to notice anything suspicious is going on. This is all by-the-by, of course, to anyone whose credentials have been exposed because of the hack of some 1100+ websites run by VerticalScope. You probably don't care too much about the bogus accounts on the sites at the moment and, quite rightly, are more concerned about your own security. So, if you believe you might be at risk, change your passwords both on the sites and anywhere else on the web that could be using the same passwords. As I explained in a recent video, I'm not a big fan of users being forced to change their passwords regularly (a regime that VerticalScope says it plans to introduce), but there is no argument in this case: your password has been exposed, so you really must change your password. My recommendation is to use a good password manager to help you with that process. A password manager can generate truly random passwords for you and remember them for you, thereby reducing the chances that you reuse passwords in future or choose weak ones that are easy to guess. To learn more about password managers, click here. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

