Three men have been arrested in Nigeria, suspected of being members of an organised cybercrime gang that has targeted over 500,000 government agencies and private sector companies around the world.
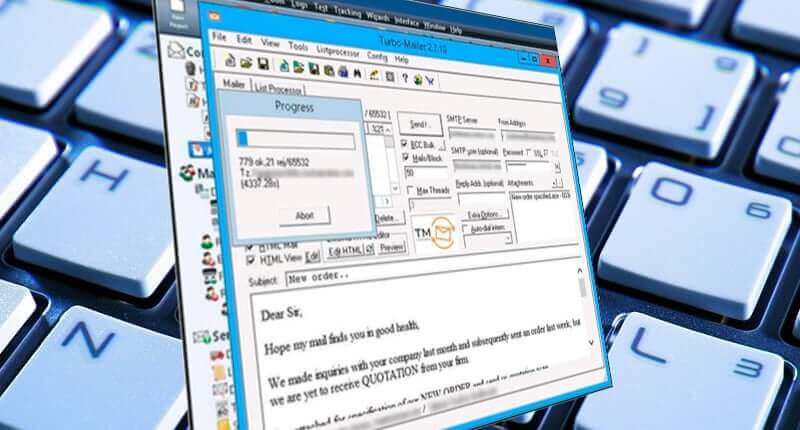
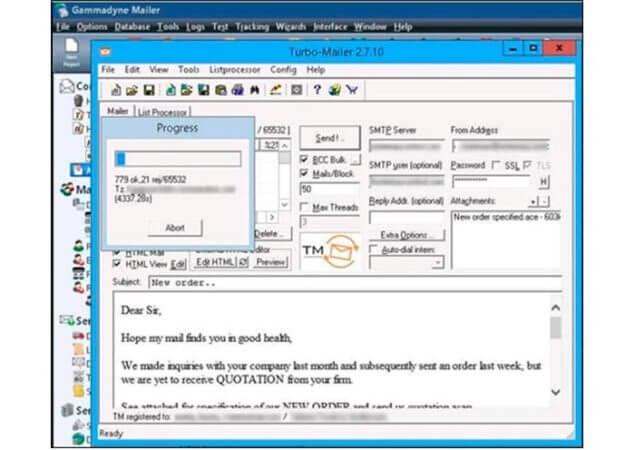
The group, dubbed TMT by threat researchers at Group-IB, is said to have engaged in attacks against businesses since at least 2017, tricking company employees into opening malware-laced emails posing as purchase orders, product inquiries, and even updates related to the COVID-19 pandemic.
If unsuspecting users were tricked into opening the malicious file attachments, hackers were able to remotely infiltrate organisations and steal data.
In all, according to a press release by Interpol, some 26 different malicious programs, including spyware and remote access tools, were distributed in the attacks, including AgentTesla, Azorult, Loki, Spartan, Nanocore, and Remcos.
With privileged access to company systems, the TMT gang would then launch Business Email Compromise (BEC) attacks, duping companies into wiring substantial amounts of money into bank accounts under the control of the criminals in the belief that they were paying genuine invoices.
A sophisticated BEC scammer will exploit their access to privileged information found in the hacked company's email accounts by reading communications and observing what projects are being worked upon. They will then pose as the supplier to have funds moved into a bogus bank account.
"Operation Falcon", a year-long investigation into TMT's activities, which saw Interpol, Group-IB's investigators, and the Nigerian Police Force working together, resulted in the recent arrest of three men in their thirties in Nigeria's largest city of Lagos, and their computer hardware seized.

And, if Interpol is to be believed, this may not be the last arrest related to the activities of the TMT gang.
"This group was running a well-established criminal business model," said Craig Jones, Interpol's Cybercrime Director. "From infiltration to cashing in, they used a multitude of tools and techniques to generate maximum profits. We look forward to seeing additional results from this operation."
Business email compromise, also sometimes known as "whaling" or "CEO fraud," is a considerable and growing threat for organisations around the world.
Companies must educate their staff about the threats and put measures in place to reduce the chances that they will become the next victim of a BEC attack.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

