Critical infrastructure is under attack with disastrous implications that could alter our environment, such as disrupting service or even threatening public safety. The Ukraine attack resulting in six hours of loss of power for more than 80,000 customers is a recent reminder. According to an October 2015 report in CyberWarNews, “every bit of U.S. infrastructure – from power grids to dams to air and ground traffic control to water treatment plants and our financial institutions – are all accessible online. And while these systems are defended, some are still more vulnerable than others.” Industrial Control Systems (ICS), typically managed by the operation technology group, are the critical systems for energy and power organizations, which are coming online. Typically, the malware enters through information technology (IT) and transverses to the operations systems like ICS – often times, through typical IT threat vectors like published vulnerabilities, misconfigurations or email phishing scams. Recently, the Electricity Information and Sharing Center (E-ISAC), a provider of security services to electricity service owners and operators in the USA, Canada and portions of Mexico, urged members “to do a better job” on their cyber defenses following the Ukraine incident. Recent reports indicate the Ukraine attack was a very well coordinated attack with such tactics as flooding the customer service lines to prevent indication that power was lost. It also included a range of tactics to distract operators. The SANS blog noted, “The malware also appears to have been used to wipe files in an attempt to deny the use of the SCADA system for the purposes of restoration to amplify the effects of the attack and possibly to delay restoration.” The utility's operators quickly recovered by switching to manual operations, essentially disconnecting infected workstations and servers from the grid. Attackers are resourceful and have a tendency to evolve existing malware. A well-known malware, Black Energy (found in the Ukraine attack) has been around since 2007 has recently been updated to destroy parts of a computer’s hard drive and has the capability to sabotage industrial control systems. One would think that it should be easier to detect if known for that so many years. ICS-CERT advises that the YARA rules can be used to detect the newer Black Energy malware but offer caution and recommend a phased approach to avoid unintentional interaction with ICS. Will 2016 be the year of the ICS attacks? Many key ISC components were programmed long before security was a concern, resulting in no security. On top of this, there are few ICS security experts. The IT security experts know very little about ICS but they should protect the IT infrastructure to minimize malware to enter and traverse to the ICS. Though this security expertise gap exists, the friction between IT & OT also needs to manage with a common goal to secure. So, how can energy and power organizations strengthen their defenses?
- The Department of Homeland Security (DHS) has just released a helpful report on “7 Steps to Effectively Defend Industrial Control Systems.” Learn how Tripwire implements the 7 steps offered by DHS.
- Consider continuous monitoring & control of assets to avoid a coordinated effort from a malicious actor like the Ukraine attack. To decrease operating costs and the introduction of human error make sure your solution is integrated with other security solutions and operates with an automated workflow. Take a look at this Executive Guide to The Top 20 Critical Security Controls.
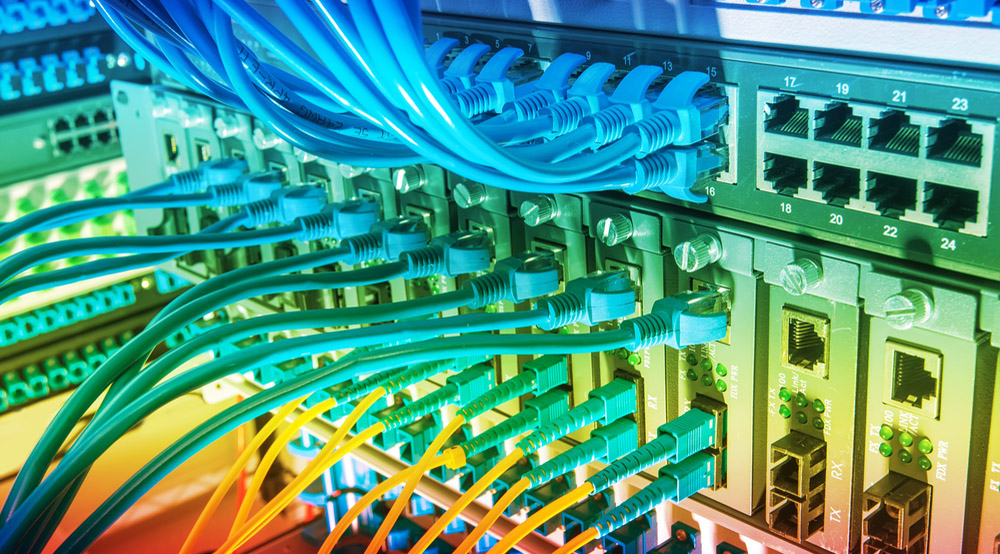
ICS infrastructure should not be taken for granted. Let’s make 2016 a year of significant cyber security progress with critical infrastructure for Energy and Power. Title image courtesy of ShutterStock

