
Getting root is fun, and with IoT gadgets, getting root is generally easy. This is why the IoT Hack Lab @ SecTor will be so much fun! If you still reminisce about (or look forward to) the first time you got root on a device, and you will be in Toronto on October 20-21, visit us at the convention centre where we’ll be setup in the expo hall. Expo passes are free with pre-registration using the code SecTor2015Expo, so there’s really no excuse not to check it out. Throughout both days of the conference, we will have brief presentations (outlined here), as well as devices available for security assessments. A few of us will be on-site to assist in learning the arts of vulnerability assessment in a hands-on practical manner. Topics will range from black box testing to firmware extraction and binary analysis. The targets will include all the usual suspects, including XSS, CSRF, SQLi, OS injection and of course, authentication bypass. After spending some time with us, you will be able to walk away empowered to vet the security of your gadgets rather than simply hope that they are secure (or assuming they are not). Here is just one of the many device vulnerabilities we will be using as an example:
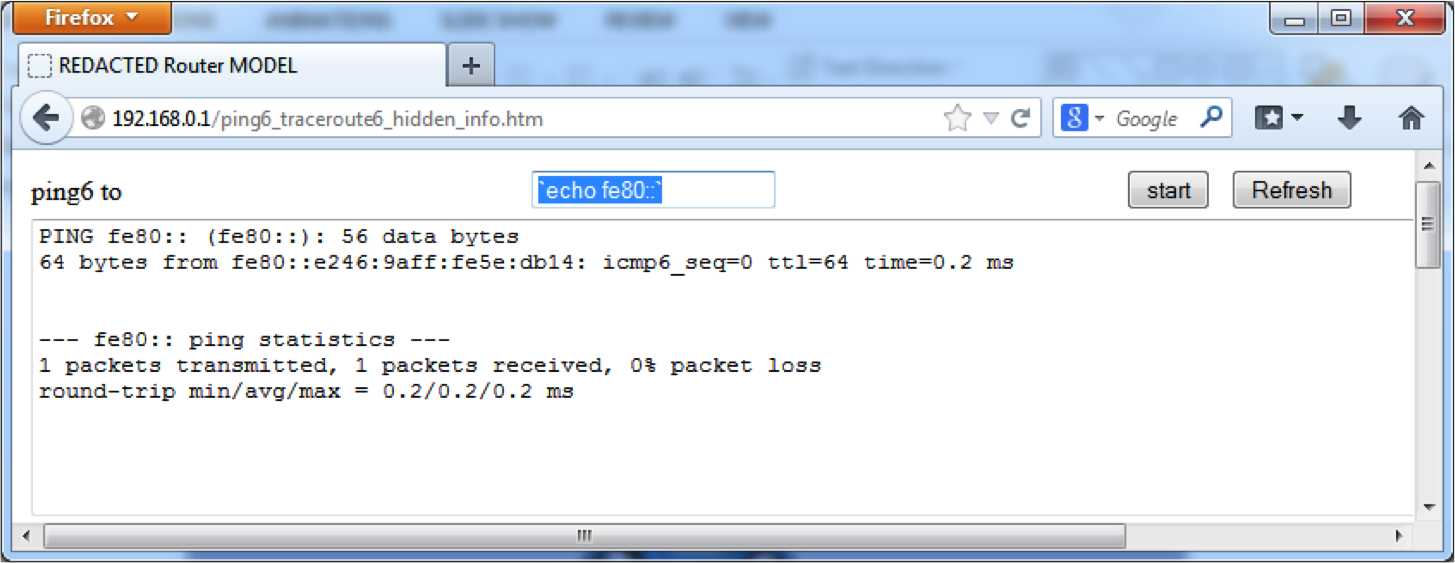
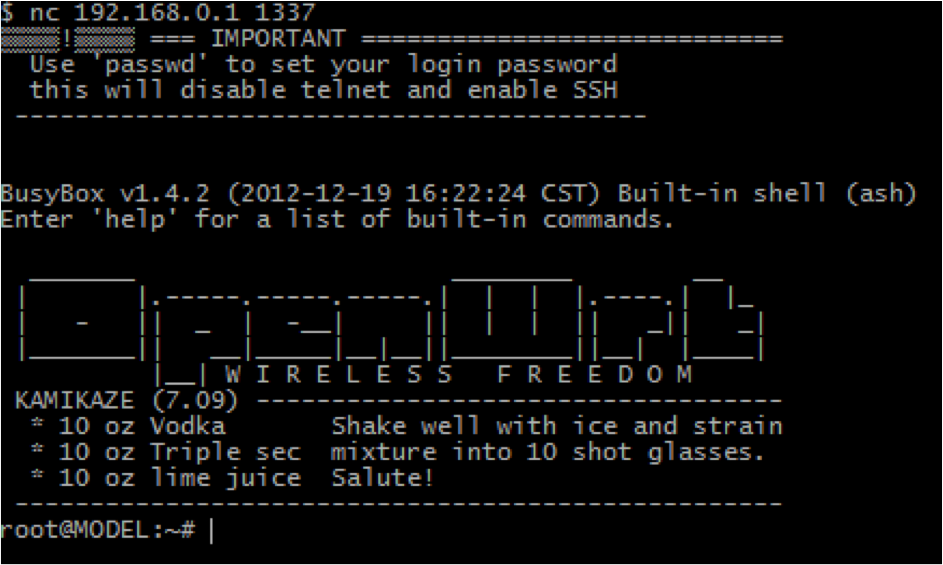
This command injection was discovered through a combination of simple firmware analysis and black box testing. The same system was also found through binary analysis to have a complete authentication bypass exposing this root command injection to anyone able to route to the device. An HTTP request or two later, and we have a shell:
That’s all the time I have for sharing today, but I hope to see you at SecTor, one of our gems in the world of information security conferences, where there will be plenty of time for much more! Title image courtesy of ShutterStock
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

