
The FBI has arrested a 33-year-old software engineer in Seattle as part of an investigation into a massive data breach at financial services company Capital One. Paige A. Thompson, also known by the online handle "erratic," has been charged with one count of computer fraud and abuse, after an investigation uncovered that a hacker had broken into cloud servers run by Capital One and stole data related to over 100 million credit-card applications. Exposed information, according to Capital One, included data collected in credit card applications between 2005 and early 2019 such as:
- names
- addresses
- zip codes/postal codes
- phone numbers
- email addresses
- dates of birth
- income
Beyond the credit card application data, the hacker also obtained portions of credit card customer data, including:
- Customer status data, e.g., credit scores, credit limits, balances, payment history, contact information
- Fragments of transaction data from a total of 23 days during 2016, 2017 and 2018
Capital One says that about 140,000 Social Security numbers and approximately 80,000 linked bank account numbers of its secured credit card customers were also breached. In a statement posted on its website, Capital One blames a "configuration vulnerability" for the security breach which allowed the hacker to access the sensitive information. Capital One determined on July 19 that an outside party had managed to access its systems without authorisation, and began working with federal law enforcement. However, it seems that the investigation only began after a security researcher who was an acquaintance of the alleged hacker emailed the firm's responsible disclosure program two days earlier, telling the company that sensitive data from its cloud-based Amazon Web Services' S3 bucket was present on Github.
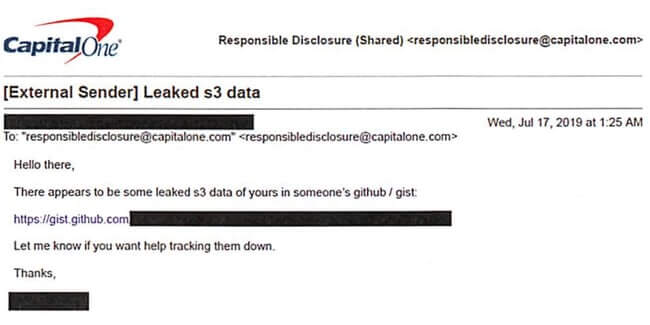
Hello there, There appears to be some leaked s3 data of yours in someone's github / gist [LINK] Let me know if you want help tracking them down, Thanks,
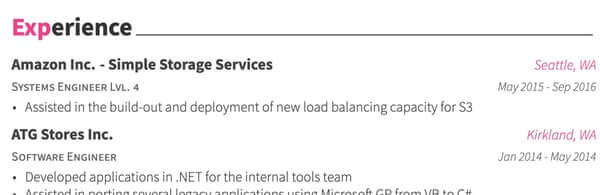
The Github account storing the stolen data was in the name of "paigeadelethompson." Perhaps coincidentally, Paige Thompson's online résumé (which contains her full name, address, and phone number) says that she was an Amazon S3 systems engineer from May 2015 to September 2016.
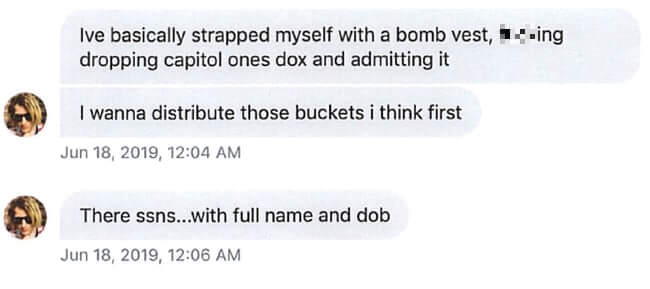
According to the FBI, a deeper investigation uncovered private Twitter direct messages between Thompson and the individual who ultimately informed Capital One of the breach, as well as conversations in a Slack group.
Armed with this and other information it didn't take the FBI long to track down their suspect and arrest her yesterday at the house where she lives in Beacon Hill, south east Seattle. During a search of Thompson's bedroom, the FBI seized a number of devices - which it is claimed contained files that referenced Capital One, Amazon, and her "erratic" alias. Downloading 100 million records doesn't sound like the kind of behaviour you would expect to see if someone was trying to raise the alarm about a configuration problem. It's perfectly possible to demonstrate that a security issue exists without stealing that volume of data. In a press release, Capital One's chairman and CEO apologise to affected customers and credit card applicants:
"While I am grateful that the perpetrator has been caught, I am deeply sorry for what has happened," said Richard D. Fairbank, Chairman and CEO. "I sincerely apologize for the understandable worry this incident must be causing those affected and I am committed to making it right."
The company says that it does not believe that the hacked data has been used for fraud or disseminated, but that it will continue to co-operate with the authorities and investigate. Capital One says that free credit monitoring and identity protection will be made available to everyone impacted.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

