
Recently, Tripwire published a study on the use of the term “cyber” in the United States’ National Security Strategy (NSS) documents. This analysis reveals that each NSS report has used the word “cyber” more frequently than its immediate predecessor. It also demonstrates how the meaning of “cyber” has diversified and evolved over time. I will now utilize this study, particularly those insights revealed from the 2015 U.S. National Security Strategy, as a reference point from which I will examine the national security documents of other countries. I begin my comparative analysis with the United Kingdom’s 2010 National Security Strategy, entitled, “A Strong Britain in an Age of Uncertainty: The National Security Strategy.”*
The UK – A Level-Headed Approach
The 2010 UK National Security Strategy references the term “cyber” a total of 29 times over the course of 39 pages. Statistically, this means that “cyber” appears on approximately three out of four (74 percent) of the report’s pages. My analysis reveals that “cyber” is used in four major points of context: “cyber attack,” “cyber space,” “cyber security,” and “cyber crime.” The relative distribution percentages of those context points are displayed below in Chart 1.
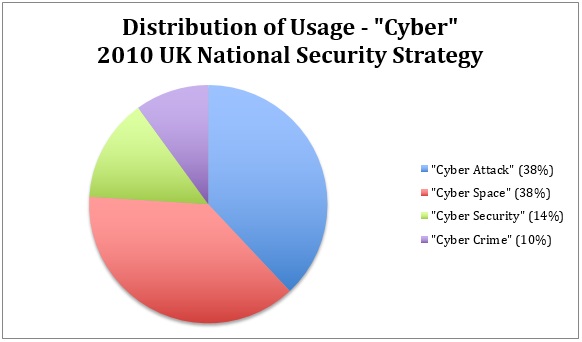
Chart 1 As one can see, both “cyber attack” and “cyber space” occur the most frequently with regards to usage of the term “cyber” in UK NSS 2010. The fact that they both register at 38 percent is significant to the extent that the document dedicates equal focus to the need to protect against cyber attacks and to recognize the connections and opportunities for peace inherent in our shared “cyber space.” These two context points are then followed by “cyber security” and “cyber crime” at 14 percent and 10 percent, respectively. On at least five separate instances, the document refers to “cyber” as one of the nation’s “highest priority risks.” In fact, the “cyber” threat is second only to the threat of international terrorism, but even then, the authors of UK NSS 2010 recognize that “cyber” is an enabler of terrorism and is therefore growing as a threat. (29) Below “cyber” on the United Kingdom’s list of threats are major accidents and natural hazards, as well as international military crises, i.e. war and other forms of armed combat. It is significant that the document elevates the “cyber” threat above the threat of war. This threat hierarchy likely reflects the fact that no state in the international sphere currently threatens the UK. Additionally, it mirrors the growing danger of cyber crime and cyber espionage to companies, governmental agencies, and UK citizens above all other forms of attack. Under the section “Cyber Attack” in Part 3: Risks to Our Security, the document reads, “Activity in cyberspace will continue to evolve as a direct national security and economic threat, as it is refined as a means of espionage and crime, and continues to grow as a terrorist enabler, as well as a military weapon for use by states and possibly others” (29). Espionage and crime are mentioned before terrorism and a militarized cyber domain, which suggests that even with regards to the possibility of a “cyber attack,” the UK views the issue of data being stolen or compromised as the most serious cyber threat confronting the nation. Despite these dangers, some optimism is evident in the document. On more than one occasion, the UK mentions leveraging certain cyber security “advantages” to address the current threat landscape. The document therefore recognizes that the United Kingdom can draw upon its national resources to protect against cyber attack and make the most out of cyberspace’s overall potential.
The U.S. – A Wary "Securitized"Approach
The United Kingdom’s 2010 National Security Strategy differs in some important ways from the United States’ 2015 NSS. This document mentions “cyber” 19 times on 35 pages, which means that the term is included on just over half (54%) of the document’s pages. My analysis reveals that unlike UK NSS 2010, the context points “cyber security,” “cyber attack,” and “cyber threat/activity” dominate most of U.S. NSS 2015 at 32%, 26%, and 21%, respectively. Only then does the context point “cyber space” factor in at 11%, followed by “cyber infrastructure” and “cyber theft” at both five percent. Although the UK’s 2010 National Security Strategy document names “cyber” as one of the nation’s highest priorities, no similar mention is made here. In fact, cyber security receives its own section only in the context of ensuring access to shared spaces, including space and air, as opposed to UK NSS 2010, which gives “Cyber Attack” its own section with regards to risks that threaten UK security. As the context point distribution chart above suggests, most of the document’s emphasis is on protecting against “disruptive and destructive” cyber attacks to critical infrastructure. The cyber threat is also frequently paired with the military, which suggests that United States’ approach to the cyber threat landscape is (at least rhetorically) more securitized than that which is followed by the UK. Also unlike UK NSS 2010, the United States makes no mention of advantages in cyberspace. It does mention, however, the importance of establishing norms for the peaceful use of this shared domain, hinting at the United States’ self-perception as a “cyber leader.”
Conclusions
The United Kingdom recognizes both the potential threats and benefits of cyberspace. The nation sees the cyber threat as one of the UK’s highest priorities behind terrorism and before war, with cybercrime and cyber espionage at the forefront of its mind. This differs with the United States’ approach to cyber security, which is marked by greater emphasis on protecting against cyber attacks without as much of an emphasis on ensuring cyberspace’s peaceful uses. The United States is also more prone to use securitized language when discussing the cyber threat. *This document is the UK’s most recent national security document, although separate updates have been released since 2010. A year later, the United Kingdom released a national cyber security strategy, but for the purpose of understanding how “cyber” relates to other pressing threats confronted by the UK, I have narrowed my study only to NSS 2010.
Related Articles
Resources:

The Executive’s Guide to the Top 20 Critical Security Controls Tripwire has compiled an e-book, titled The Executive’s Guide to the Top 20 Critical Security Controls: Key Takeaways and Improvement Opportunities, which is available for download [registration form required]. Title image courtesy of ShutterStock
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

