
In early February, the White House released its 2015 National Security Strategy (NSS). Each NSS report is symbolic to the extent that it reveals the security issues the acting U.S. president intends to focus on for the coming months and years. While not constituting “hard,” actionable strategies, these documents help to articulate the future security foci of the United States. Cyber security has become a growing issue in recent NSS reports. This is in part reflected by President Obama’s recent executive order that calls on greater information-sharing between governments and the private sector with regards to cyber threats. But in what context does the White House view cyber threats as a national security concern? And how has the U.S. President’s interpretation of these threats evolved over the time? To answer these questions, I completed a brief study of the United States’ past National Security Strategy reports. This study sought to evaluate these documents’ usage of the term “cyber,” both quantitatively (number of times used throughout) and qualitatively (the context in which the term was used). I present my findings in Table 1 below:
Table 1: A Historical Study of “Cyber” in U.S. National Security Strategy Reports
| Title of Document | Year | Acting President | Link | # of Times “Cyber” Used | Context Words |
| A National Security Strategy for a New Century | 1998 | Clinton | http://nssarchive.us/NSSR/1998.pdf | 4 | Infrastructure protection, crime, international partnerships |
| A National Security Strategy for a New Century | 2000 | Clinton | http://nssarchive.us/NSSR/2000.pdf | 10 | Infrastructure protection, crime, partnerships (international and private), info-sharing, threat detection |
| A National Security Strategy for a Global Age | 2001 | Clinton | http://nssarchive.us/NSSR/2001.pdf | 8 | International threat, asymmetric warfare, information, cyber resilience |
| The National Security Strategy of the United States of America | 2002 | G. W. Bush | http://nssarchive.us/NSSR/2002.pdf | 0 | N/A |
| The National Security Strategy of the United States of America | 2006 | G. W. Bush | http://nssarchive.us/NSSR/2006.pdf | 1 | Cyber and space domains, militarization of cyberspace |
| National Security Strategy | 2010 | Obama | http://nssarchive.us/NSSR/2010.pdf | 22 | Military support, global priority, partnerships, terrorism, awareness, asset |
| National Security Strategy | 2015 | Obama | http://nssarchive.us/wp-content/uploads/2015/02/2015.pdf | 19 | Cyber espionage, norms, infrastructure, growing threat, militarization, resilience, partnerships |
A number of important highlights from my study deserve mention. From a quantitative standpoint, as illustrated in Chart 1 (see below), the White House is for the most part increasing its use of the term “cyber” from year to year. Indeed, my data suggests that between 1998 and 2015, a direct relationship emerged between time and usage of the term “cyber.” President Obama has by far been the most cyber-conscientious U.S. president, having used the term 22 times in his 2010 National Security Strategy and 19 times in the nation’s most recent report. Obama is then followed by Clinton, who used the term 10 times in 2000, eight times in 2001, and four times in 1998. Out of the three presidents, George W. Bush used the term but once in his 2006 National Security Strategy. He did not use it at all in his 2002 report—a finding which likely reflects the nation’s growing concern with international terrorism in the wake of the September 11 attacks.
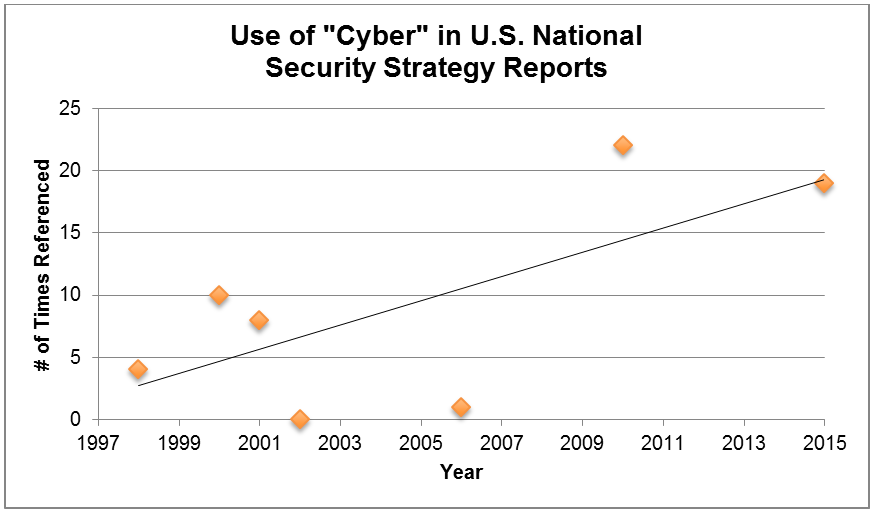
Chart 1: Number of Times "Cyber" Used Qualitatively, the White House first began to conceive of “cyber” under President Clinton back in 1998. All of his National Security Strategy documents—1998, 2000 and 2001—generally related cyber threats to the protection of critical national infrastructure, as well as international crime and interstate partnerships. Between 2000 and 2001, we began to see the militarization of the term “cyber,” which in part reflected the growing cyber conflict between China and Taiwan at the time. Acknowledging this shift, the White House emphasized building a comprehensive plan for cyber resilience, which included public-private information-sharing partnerships, threat-detection measures and a capable workforce, in additional to the safeguarding of infrastructures. As the United States prepared itself for the War on Al Qa’ida under President George W. Bush, the usage of the term “cyber” diminished in frequency. In 2002, the term was not used a single time, whereas in 2006, “cyber” was paired with space as a means of providing military support for kinetic force projection abroad. It was not until Obama was elected President that the nation saw the usage of the term “cyber” diversify in its National Security Strategy reports. In 2010, cyber was allotted its own section, “Secure Cyberspace,” for the first time in any NSS document. This reflected the document’s more urgent verbiage with respect to cyber threats, language which labeled “cyber” as “one of the most serious national security, public safety, and economic challenges we face as a nation.” Along these lines, the document recognized how cyber security reaches beyond infrastructure protection and extends to other threats, such as terrorism as lost profits for companies. The report therefore proposed a campaign for “cyber security awareness and digital literacy” in boardrooms across the country. 2015 echoes many of the concerns put forth in 2010, but in the shadow of the Sony hack, it places a special emphasis on cyber espionage, international norms, and the need to preserve the shared global “cyber domain.” Reflecting its central role in creating the Internet, the United States has long been a leader regarding its ability to interpret new and emerging cyber threats, a position of authority which it has sought to convey in its National Security Strategies. However, this study begs the question: How do other nations compare to the United States? In the coming weeks, I will examine the security documents of a number of other countries and seek to understand how they compare to U.S. national security strategy. This exercise will help shed light on the United States’ alleged leadership in cyber security, as well as provide insight into any opportunities and challenges for international cooperation on the issue of cyber security in today’s world.
RESOURCES:

The Executive’s Guide to the Top 20 Critical Security Controls Tripwire has compiled an e-book, titled The Executive’s Guide to the Top 20 Critical Security Controls: Key Takeaways and Improvement Opportunities, which is available for download [registration form required].
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

