For a Democratic Party desperate to unseat President Trump in November, the primary election process has been filled with large-scale technology failure, official miscalculations, voter annoyance and public embarrassment, not to mention piles of money spent in pursuit of an improved 21st-century process that turned out to be worse than what they had. They might have been better to just pass out paper ballots and pencils.
https://www.flickr.com/photos/cornelluniversitylibrary/4360087958 It’s no secret that America’s election process has fallen decades behind the capabilities of modern technology. The big issue is how to ensure that hackers don’t emerge from the Dark Web to stick their fingers in the mix in order to prevent votes from being counted quickly and reliably. Let’s take a look at a couple of public failures, Iowa and Los Angeles, to learn what went wrong and how best to create secure voting systems before the 2020 presidential election.
The Iowa Caucuses
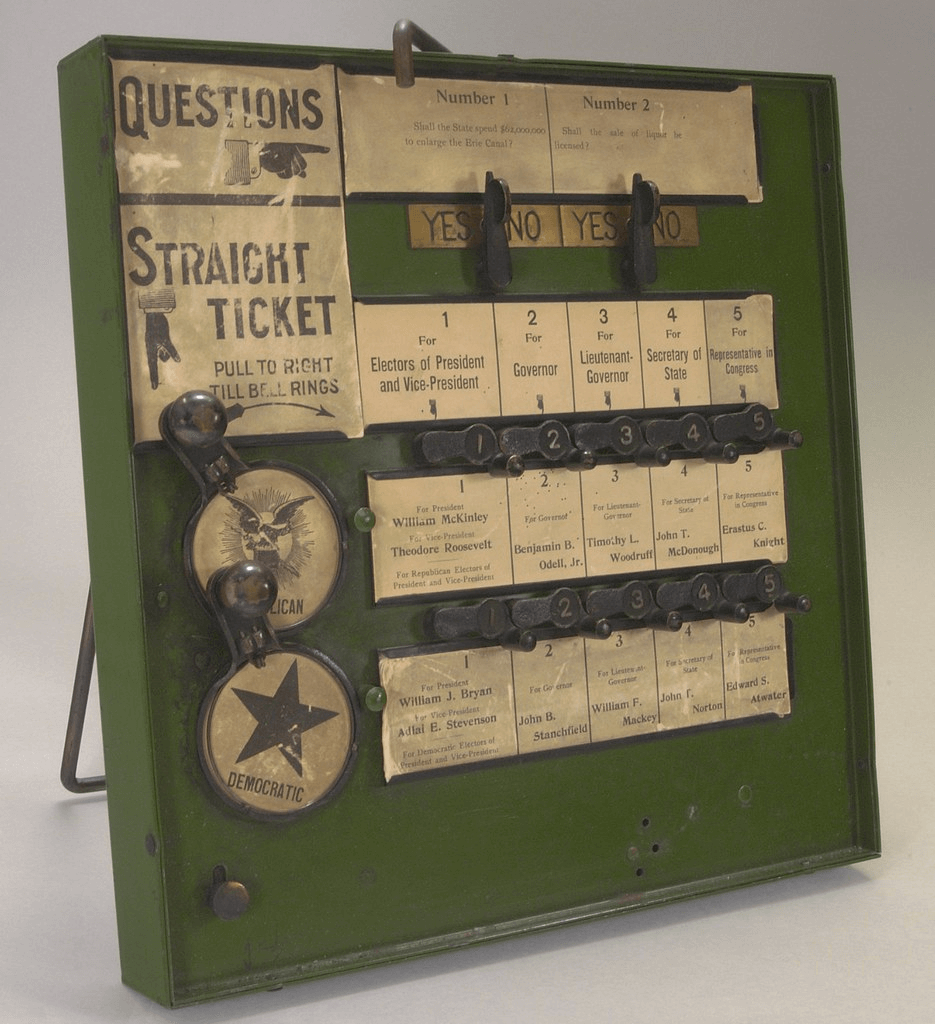
First up in the primary season is a (some would say) antiquated process that isn’t really a primary at all but rather something called a caucus. We’re all familiar with a typical primary. You go to the polls and vote like a sane human being. A caucus is a cat of a different flavor. Before voting, those who want to make their voice heard gather around the state in a series of smallish precinct meetings (there are 1,700+) and try to come to a conclusion on which candidate each precinct supports.
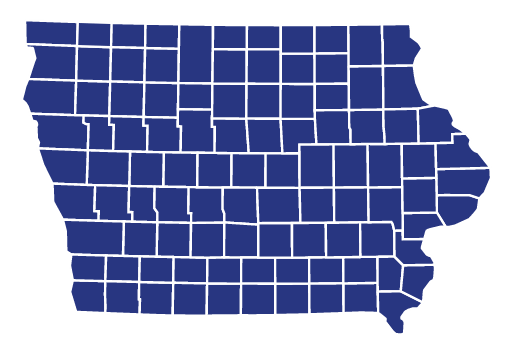
https://en.wikipedia.org/wiki/File:2020IAGOPcaucus.svg Iowa Republicans typically caucus in an orderly manner. Secret ballots are cast and delegates are apportioned by the results, a process not unlike a primary. But the Democratic caucus involves a lot of public shouting, arguing, and trying to persuade everyone in the room to vote one way or another. As you might imagine, it can be loud and messy. This year, the Democratic National Committee (DNC) decided to tighten up the rules for any state that wanted to continue to hold a caucus rather than a primary. The DNC-approved solution involved creating a virtual caucus where party members could call in their vote. After working in coordination with state officials on plan implementation for seven months, the DNC unexpectedly pulled the plug on the virtual caucus. It based its decision on security concerns, of which there are plenty in the world today. Voting returned to the old method, though an app was allowed to report. The short version of the disaster that followed was the app wasn’t rolled out until two weeks before the caucuses. On election day, there were glitches related not to the app but rather a data storehouse. Out of 1,765 precincts, only 624 managed to download and install the app, and an unimpressive 439 completed the vote submission process. The final vote tallies weren’t formalized until two weeks after the election. By that time, Iowa had wasted its annual place in the spotlight as the first-in-nation voting and was relegated to laughingstock for the technical issues that arose. In the aftermath, the app’s manufacturer, Shadow, Inc., took responsibility for the fiasco, though one industry expert blamed election officials for cutting corners with a “smallish firm, a cheapish app” and for not testing it properly. The problem might have been more insidious. Research shows that more than 90% of customers will look into a company before making a purchase, but surprisingly, no one seemed to bother digging into Shadow, Inc (until recently). A report from Jacobin Magazine identified issues with the company, namely connections to Hillary Clinton’s 2016 campaign as well as 2020 U.S. presidential candidate Pete Buttigieg. Regardless of technical details, the bottom line issue that got the plug pulled on the virtual caucus plan was a lack of security. This is a common theme in the Technology Age in America.
Los Angeles Gives it a Whirl
Prior to the 2020 primary, Los Angeles County, the most populous county in the nation with more voters than 42 states, relied on an antiquated paper voting system straight out of the 1960s. Literally. It was deployed in the 1960s. This election would be the coming-out party for a $300 million new system that had been 10 years in the making. What could possibly go wrong? In this case, the system worked fine, but the process was completely unprepared to handle the number of people who wanted to vote. There were pinch points along the way. Specific problems such as long lines and too few Spanish-speaking election workers contributed to a situation where some voters queued for as long as three hours to make it to the front of the line. The actual voting process went well, and in the opinion of many, it was a vast improvement over the old system. Don’t be surprised if this process becomes a state and national model minus the screwups. Were there security concerns? Of course. There will always be security concerns. While some new voting systems are connected to the internet, popular cybersecurity software like VPNs don’t provide ironclad protection since there are still unaddressed vulnerabilities at a network’s endpoints. The good news is that the LA County election machines are not connected and thus, unlike the app used in Iowa, harder to hack.
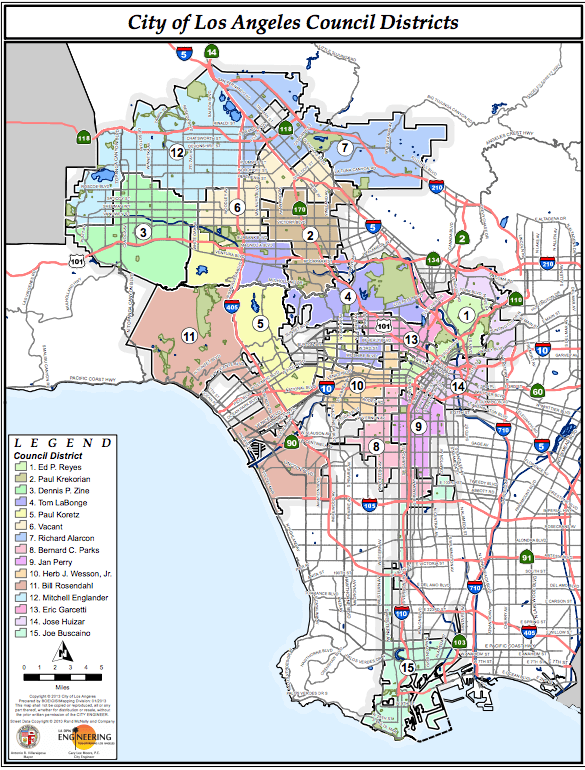
https://commons.wikimedia.org/wiki/File:Map_of_LA_City_Council_Districts.png
The Future of Elections
From a quick review of the recent Iowa and Los Angeles primary elections, it’s obvious that there are a few areas that need greater focus going forward. The first is simply the logistics of resolving election day pinch points so everything flows smoothly. Second is to have a system ready way ahead of time (LA did this, Iowa didn’t) to permit a thorough testing period. Lastly, and perhaps most importantly, is to have adequate security measures, both physical and cybersecurity. You need to be able to prevent the possibility that election officials could tinker with votes as well as keeping out any hackers in the mood to cause a little chaos. While we’re still in the early phases of figuring out the best way to secure elections, here are some areas where the effort will focus.
Partnerships
Securing elections effectively shouldn’t be left to state or local governments alone. The federal government and private companies need to be part of the process, as well. It’s the only way we can ever secure the entire election infrastructure, which is more complex than some might realize and includes:
- Voter registration databases
- Necessary IT systems to manage counting, auditing, and displaying results, as well as post-election certification and validation
- Voting systems and support infrastructure
- Storage facilities for voting machines
- Polling location security, including early voting
The Department of Homeland Security (DHS) is the point agency that will lead the collaborative effort by assigning roles and responsibilities among state, local, public, and private entities.
Security Strategy
When it comes to the actual security strategies involved, the software, apps, utilities, and methods are no big secret. They are used by security experts around the world every day and include:
- Cybersecurity Advisors/Security Advisors: Experts should be available at every level (federal, state, local, private) to provide on-demand advice and assistance with cyber and physical threats.
- Cybersecurity Assessments: These would include, but aren’t limited to, cyber hygiene scanning, risk, and vulnerability assessment and cyber resilience reviews. Detection and Prevention: Implementation of cutting edge software for threat detection and elimination.
- Incident Response: In the event of a breach, the response should be pre-planned, thorough, and immediate.
- Ongoing Cybersecurity Training and Education: This should likely come from the federal government.
With the COVID-19 pandemic expected to drive already high household debt rates even higher, the result will be an election system under even more stress in November due to higher voter turnout or a lesser turnout driven by some level of quarantining still in effect. Hopefully, it will be the former because more people voting is a good thing. Here’s hoping those in charge of managing the voting process get it right.
Final Thoughts
For those who think elections can ever be completely and utterly secured, you’re deluded. That reality is no more likely than achieving peace on earth. But that doesn’t mean you shouldn’t try and can’t make progress. The battle between hackers and cybersecurity experts will never end because there are smart, creative warriors on both sides. As soon as one side deploys a new strategy, the other side makes a move to even it up. Attackers will always have a slight advantage over defenders, but that’s life. Let’s raise a slice of toast to fair elections! Everyone should be in favor of that.
About the Author: Sam Bocetta is a freelance journalist specializing in U.S. diplomacy and national security, with emphasis on technology trends in cyberwarfare, cyberdefense, and cryptography. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.

