
A couple of phishing schemes are currently targeting contractors who do business with two U.S. federal government agencies.
Anomali Labs uncovered a malicious server hosting the two schemes in late February 2019. The first scheme begins when users visit transportation[.]gov[.]bidsync[.]kela[.]pw, a suspicious-looking subdomain which contains the legitimate "transportation.gov" domain for the U.S. Department of Transportation. This site, in turns, redirects web browser users to a site located at hxxps://transportation[.]gov[.]qq-1[.]pw/V1/ that mimics the DOT eProcurement portal.
The page differs from the actual DOT eProcurement portal, however, in that it displays a pop-up window asking qualified contractors to submit bids for government work. This window includes a fake email address for Leonardo San Roman, who actually works for the DOT as the acting manager of its Office of Small and Disadvantaged Business Utilization’s Procurement Assistance Division.
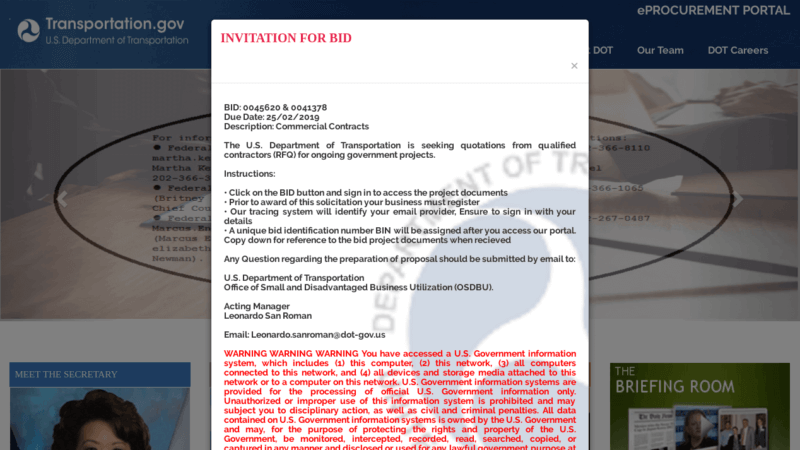
Additionally, the illegitimate DOT eProcurement portal contains a slider box in the middle of the page announcing the Invitation to Bid. Finally, it includes a red box in the middle of the page titled "Click here to bid." This feature redirects visitors to a fake login page designed to steal contractors' usernames and passwords.
In their analysis, Anomali's researchers found that the server hosting the phishing transportation site used a self-signed TLS certificate to add a sense of legitimacy in the eyes of unsuspecting government contractors. They also determined that the server resolves to a shared IP address 107.180.54[.]250, the hosting location for a few other phishing schemes. Among them is dol[.]gov[.]qq-1[.]pw, which leverages the Department of Labor's "dol.gov" domain to target even more government contractors.
This second scheme functions similarly to the transportation ruse. As Anomali Labs explains in a blog post:
When navigating to the fraudulent hostname dol[.]gov[.]qq-1[.]pw, users are presented with a spoofed DOL page located at <hxxps://dol[.]gov[.]qq-1[.]pw/V1/. The spoofed site is a cloned version of the DOL mainpage with an additional feature, a red highlighted box with the words “Click here to bid”, located in the middle of the site.... Once users click to bid on the contract, a pop-up window for a login page appears that requests the potential victim’s email address and password....
Upon authenticating themselves, the fake login page displays the following error message: "Please Try again, Sign in with your correct email."

Anomal Labs recommends that government contractors protect themselves against these types of schemes by exercising caution with respect to unsolicited correspondence received from government agencies. They should also not blindly trust a padlock symbol at the top of the address bar. Indeed, they should inspect the address bar and verify that the domain actually belongs to a government agency before authenticating themselves.
Government contractors would also be wise to familiarize themselves with some of the most common types of phishing attacks preying on users. This resource is a great place to start.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

