Last week, we used the United States’ 2015 National Security Strategy (NSS) as a reference point to analyze “A Strong Britain in an Age of Uncertainty: The National Security Strategy,” the United Kingdom’s 2010 National Security Strategy. Though limited in scope, this comparative analysis revealed a number of important findings, including the UK’s recognition of benefits and challenges of cyberspace, as opposed to the more security-centric, militarized language used by the United States. After additional research, however, I have found that not all states produce national security strategy documents on a regular basis. Even so, I've determined that many of the world’s cyber powers have published written strategies detailing how they intend to utilize cyberspace in pursuit of their national interests. I will therefore avail myself of these cyber security strategies (CSS) to understand how different states’ conceptualizations of “cyber” compare with one another. For our first analysis in this new phase of our series, I will evaluate the United States’ International Strategy for Cyberspace (ISC 2011) and establish this document as our reference point looking ahead. I will then compare this document’s usage of the term “cyber” to U.S. NSS 2015 in an effort to measure the extent to which American cyber strategy has remained consistent over the past several years. The United States’ International Strategy for Cyberspace uses the term “cyber” a total of 155 times over the course of 30 pages. This includes 14 separate instances of the word being used in page headers, occurrences which we will exempt from our study, thereby bringing down our total usage to 141. Statistically, the document therefore references the term “cyber” an average of five times on each page. My analysis reveals that the ISC 2011 employs the term “cyber” in only three context points: “cyber space,” “cyber security,” and “cyber crime/criminal.” “Cyber space” is by far used the most frequently at 62% (87 times) of the total, as is illustrated in Chart 1 below:
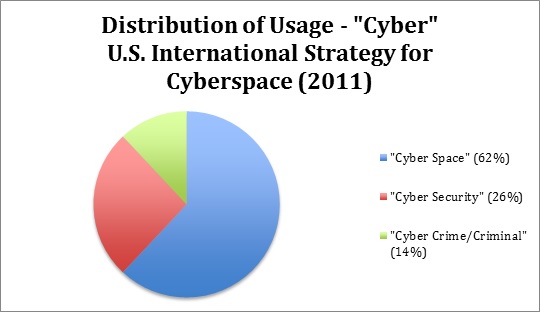
Chart 1 “Cyber space” is then followed by “cyber security” and “cyber crime/criminal,” which number at 26% (37 unique instances) and 14% (17 unique instances), respectively. It is important to note that the document does not mention “cyber attack.” In fact, the ISC 2011 employs the word “attack” in only eight separate instances and usually in reference to protecting federal and defense networks, including systems that monitor ICS/SCADA systems, against intentional disruption. By contrast, “cyber crime/criminal” occurs more than double the times of “cyber attack.” This suggests that after accounting for the greater challenges associated with “cyber security” in general, the United States is statistically more concerned about the impact of data theft and extortion (a law enforcement issue) as unique “cyber” threats than it is attacks against its federal systems (an issue that it concedes here and elsewhere might warrant “self-defense” on the part of the U.S. military). Our finding here reflects the greater focus of the International Strategy for Cyberspace, which emphasizes norm frameworks and international partnerships, such as those designed to combat the rise of cybercrime, at the expense of purely national security. This focus is reflected in how the authors of ISC 2011 have arranged the document. The second main section, entitled “Cyberspace’s Future,” is divided into two main sub-sections: “The Future We Seek” and “Our Role in Cyberspace’s Future.” The former sub-category is further divided into three sections—“Open and Interoperable: A Cyberspace That Empowers,” “Secure and Reliable: A Cyberspace That Endures,” and “Stability Through Norms”—all of which emphasize norms. Diplomacy, defense, and international development all relate to the United States’ efforts to secure those norms, suggesting that international cyber security partnerships are a means to an end: a peaceful cyber domain. It is therefore no surprise that the ISC 2011 also makes it explicit that the United States’ concerns with respect to cyber security mirror broader international issues that it feels it must take the lead in solving. As such, the document uses the term “cyber security” carefully and frequently mentions the importance of balancing security with democratic norms, such as privacy and the free flow of information.
The United States’ 2015 National Security Strategy
As a refresher, the United States’ 2015 National Security Strategy uses the term cyber a total of 19 times on 35 pages. The distribution of the word’s usage is demonstrated below in Chart 2:
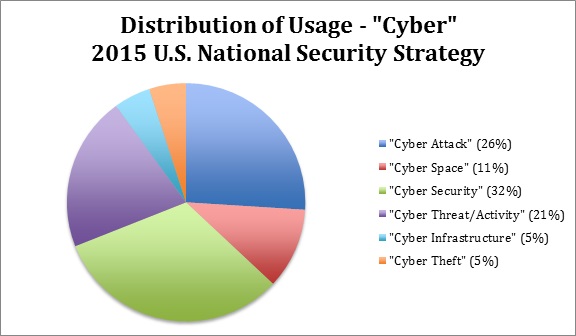
Chart 2 Unlike the ISC 2011, the U.S. NSS 2015 uses the term “cyber attack” more than 25% of the time whenever it employs the term “cyber.” When one combines this context point with “cyber threat/activity,” that percentage increases to just under half (47%). In the years after it released the International Strategy for Cyberspace, the United States has broadened its “cyber” vocabulary, as evidenced by its utilization of the terms “cyber threat,” “cyber activity,” “cyber infrastructure,” and “cyber theft.” This reflects the growing number of “disruptive and even destructive” cyber attacks against American public and private networks since 2011. As such, U.S. NSS 2015 not only categorizes “cyber security” with traditional, non-digital threats, including Russian aggression, terrorism, and disease, but it also militarizes cyberspace, referring to the development of “cyber” capabilities in the same breath as articulating its commitment to maintaining its nuclear deterrent. Norms with respect to cyberspace are directly mentioned only once. The United States does articulate, however, the need to foster international partnerships in response to the cyber threats shared by all upon numerous occasions.
Conclusions
The International Strategy for Cyberspace reflects the United States’ commitment to advancing “cyber security” and international partnerships as means of securing a peaceful cyber space. To be sure, the U.S. NSS 2015 takes a more nation- and security-centric approach than ISC 2011 with respect to its usage of the term “cyber.” But this is to be expected given the fact that the document is a national security strategy. While its understanding of cyber threats has become sharper since 2011, the United States overall continues to uphold the mission of the International Strategy for Cyberspace.
Related Articles
- A “Cyber” Study of the U.S. National Security Strategy Reports
- A Comparative “Cyber” Study of National Security Strategies – UK and the U.S.