
An investigation claims that the UK's National Health Service, which was hit hard by the notorious WannaCry worm in 2017, has seen a marked fall in ransomware attacks since. A report published by Comparitech, based upon Freedom of Information requests, reveals the somewhat surprising news that since WannaCry there have only been six recorded ransomware attacks against the NHS.
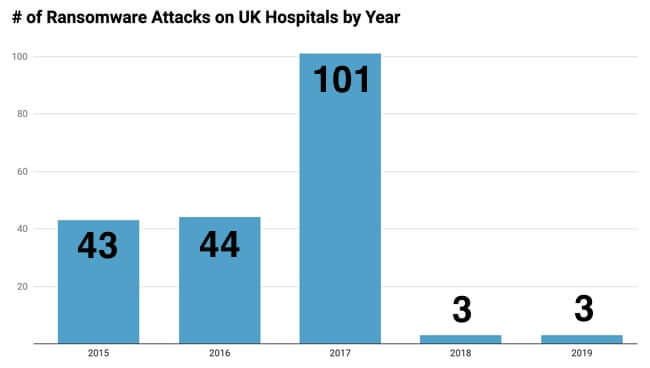
In all, the NHS has suffered a total of 209 reported ransomware attacks since 2014, but the drop in incidents since WannaCry is truly remarkable. Can it really be true? The NHS is one of the world's largest employers, and even if not all of its 1.5 million staff have computers it still seems an astonishingly low rate of infection. If the statistics are accurate, then surely there is much that other organisations could learn from the NHS's success. In Comparitech's view the lower number of attacks can be explained by the NHS putting into practice the lessons it learned from the WannaCry attack. NHS trusts increased spending to secure their infrastructure, reduce vulnerabilities, and update computers running legacy operating systems. In addition, there may well have been positive consequences from rolling out cyber awareness training amongst more staff, and reducing access to IT systems to only those personnel who need it and have undergone mandatory training. It should be borne in mind that the report's statistics are not complete - 20 per cent of hospitals unfortunately refused or failed to respond to the survey, and Comparitech notes that data from 2019 is still being processed by trusts, so the total number of attacks could creep higher. What's also disappointing is the lack of granularity about the data. After all, by just using raw numbers you get no real sense for how significant a ransomware attack might have been. If one computer is unfortunately enough to become infected with ransomware then that could be considered an attack, but it wouldn't be hard for a typical IT security team to respond. However, if hundreds of computers were simultaneously hit by a ransomware attack then the impact would be much more significant. Unfortunately, these statistics simply do not give us an insight on the severity of an attack. In addition, Comparitech notes that there was often an absence of meaningful data around how much downtime was suffered following an attack:
Some trusts noted zero downtime from the ransomware, dealing with the attack as “business as usual.” Others shut down systems as a precaution and some had to reimage PCs. The total downtime isn’t often recorded as it can affect various departments and/or staff costs are included as part of IT services. Nevertheless, when the trusts did offer downtime figures, these demonstrated just how disruptive ransomware attacks can be. The average attack causes up to 25 hours of downtime. One trust shut down its systems for 48 hours as a precaution while keeping some others off for several weeks so they could be repaired and restored as required.
A successful ransomware attack can be extremely costly for an organisation, and in some cases even put them out of business. Whether your business is big or small it's critical to take preventative steps now to both reduce the chances of becoming the next victim of ransomware, and ensure that you have measures in place to recover quickly with minimum disruption if you are ever unlucky enough to be hit.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

