
Digital attackers used spearphishing campaigns to target oil and gas companies with samples of the AgentTesla infostealer family. In the first campaign spotted by Bitdefender, malicious actors sent out emails that appeared to originate from Egyptian state oil company Engineering for Petroleum and Process Industries (Enppi). Those emails invited recipients to submit a bid for materials and resources as part of an upcoming project. But when they downloaded a .ZIP archive that claimed to contain that list of materials and resources, recipients unknowingly infected their computers with AgentTesla.
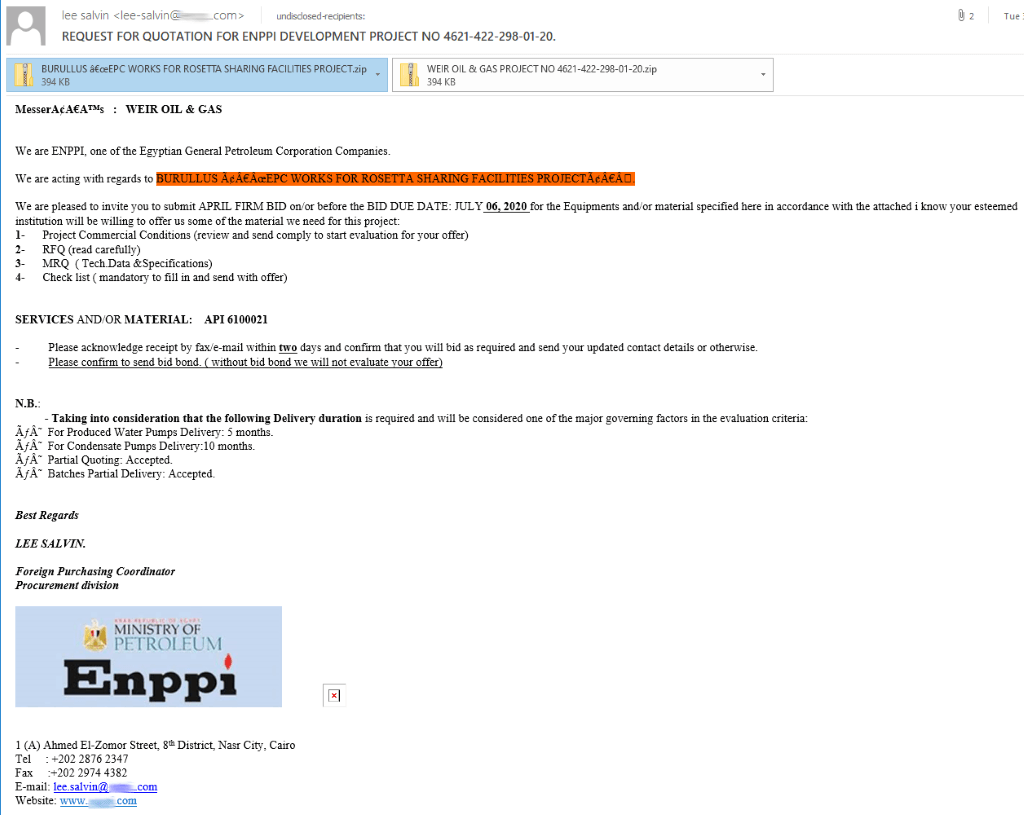
A screenshot of an attack email impersonating Enppi as its sender (Source: Bitdefender) Malicious actors used spyware such as Remcos RAT to target the oil and gas sectors in this past. But Bidefender found that this campaign stood out among some of the attack operations it's observed in recent years. As it explained in its research:
However, these campaigns seem to deliver the Agent Tesla spyware Trojan instead, and beyond just the oil & gas sector, they also target other energy verticals that have been tagged as critical during this Coronavirus pandemic. Analyzing the profile of the affected victims, we found them activating in oil & gas, charcoal processing, hydraulic plants, manufacturers of raw materials, and transporters of large merchandise.
Most reports of this campaign came from Malaysia, Iran and the United States—countries where the oil and gas industry plays an important part in their national economies. In the second campaign observed by Bitdefender, attackers informed recipients via email that they needed to send over the Estimated Port Disbursement Account (EPDA) for the shipping vessel MT.Sinar Maluku along with container flow management (CFM) information. The attack emails instructed recipients to open a .RAR file that contained a version of AgentTesla.
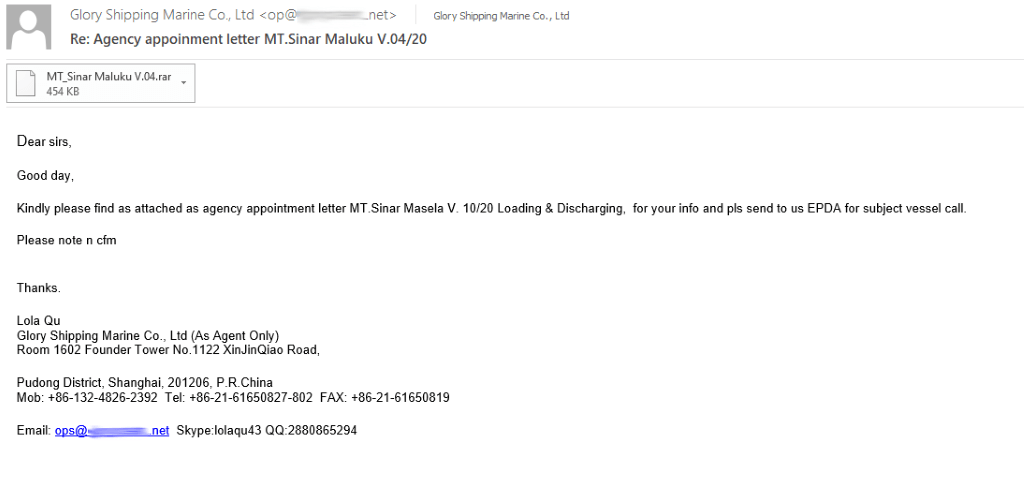
The attack email demanding information in reference to MT.Sinar Maluku (Source: Bitdefender) News of these campaigns arrived just a couple of months after the security community learned of a new spam campaign that leveraged malicious RTF documents to distribute notorious infostealers including AgentTesla and Lokibot.

