
An analysis of a new backdoor called "Poison Frog" revealed that the OilRig threat group was sloppy in its development of the malware. Kaspersky Lab came across Poison Frog while scanning its archives using its YARA rule to hunt for new and old malware samples employed by OilRig. It launched this investigatory effort shortly after crackers operating under the name "Lab Dookhtegan" used a Telegram channel to dump information about OilRig, a group which appears to be linked to the Iranian government. In its analysis of one sample, Kaspersky's researchers found an executable written in C# that dropped a PowerShell script containing a DNS and HTTP backdoor, executed the script and then deleted it. OilRig sought to avoid alerting a user to the presence of Poison Frog by disguising their malware as the legitimate Cisco AnyConnect application. This fake app displayed an error message whenever a user clicked on its "Connect" buttonp. The threat group employed this technique to mislead the user into thinking that something was wrong with their web connection or the app itself. Meanwhile, Poison Frog secretly installed itself on the user's machine.
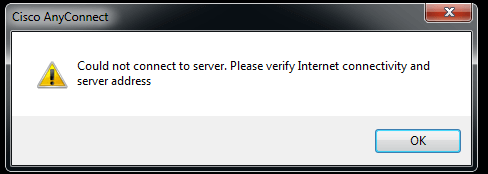
The fake Cisco AnyConnect application's error message. (Source: Securelist) That being said, OilRig made several mistakes in developing Poison Frog. Kaspersky Lab found one sample that didn't execute because it used a command for "Poweeershell.exe" instead of "Powershell.exe," for instance, while others still had the PDB path inside their binary. The researchers shed light on another common flaw affecting the samples in a post for Securelist:
With other samples, they changed the compilation date to a future date – one that was after its release. For instance, one sample – 87FB0C1E0DE46177390DE3EE18608B21 – has a compilation date of 2018-07-25, though we found it on our systems a year earlier.
News of Poison Frog's discovery comes more than a year after researchers spotted the OilRig group conducting at least one attack campaign that contained an updated variant of the BONDUPDATER trojan as its final payload.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

